Architecting a Citrix Networking Solution Questions and Answers
For which two reasons should a Citrix Architect perform a capabilities assessment when designing and deploying a new Citrix ADC in an existing environment? (Choose two.)
Scenario: The Workspacelab team has implemented a Citrix ADC high availability pair and Citrix ADC Management and Analytics (Citrix Application Delivery Management). The Citrix Application Delivery Management was configured by a Citrix Architect to monitor and manage these devices. The Workspacelab team wants to load balance their Microsoft SharePoint servers on the Citrix ADC and needs the process to be streamlined and administered using Citrix Application Delivery Management. The following requirements were discussed during the meeting.
• The Microsoft SharePoint server should be optimized. Load balanced, and secured in the network and should be deployed using Citrix Application Delivery Management.
• All the configurations should be verified before getting pushed to the Citrix Application Delivery Management.
What is a prerequisite for installing Microsoft SharePoint using Citrix Application Delivery Management?
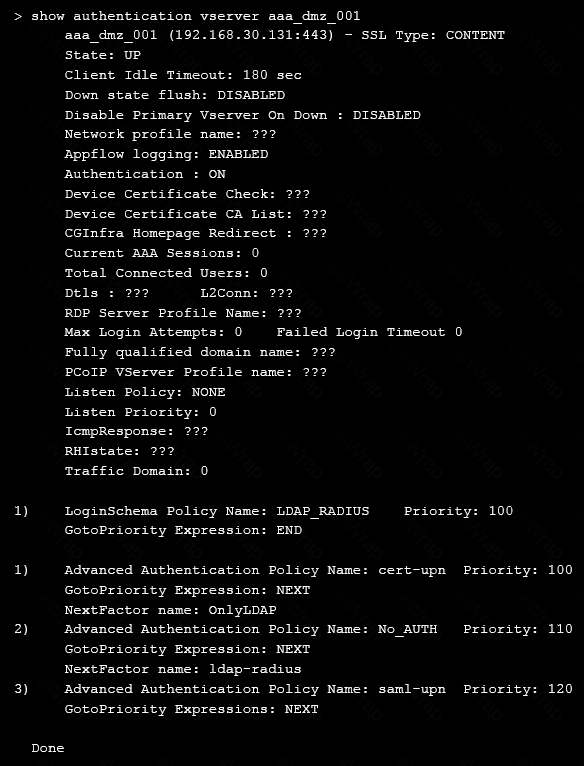
Scenario: A Citrix Architect needs to assess a Citrix Gateway deployment that was recently completed by a customer and is currently in pre-production testing. The Citrix Gateway needs to use ICA proxy to provide access to a Citrix Virtual Apps and Citrix Virtual Desktops environment. During the assessment, the customer informs the architect that users are NOT able to launch published resources using the Gateway virtual server.
Click the Exhibit button to view the troubleshooting details collected by the customer.
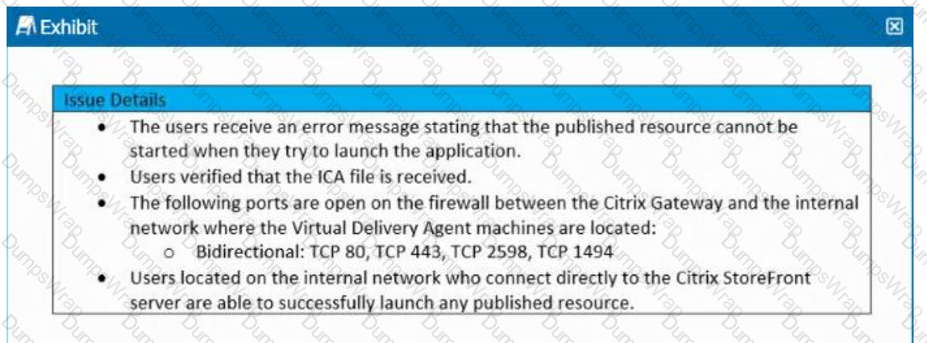
What is the cause of this issue?
Scenario: A Citrix Architect needs to assess an existing on-premises NetScaler deployment which includes Advanced Endpoint Analysis scans. During a previous security audit, the team discovered that certain endpoint devices were able to perform unauthorized actions despite NOT meeting pre-established criteria.
The issue was isolated to several endpoint analysis (EPA) scan settings.
Click the Exhibit button to view the endpoint security requirements and configured EPA policy settings.
Which setting is preventing the security requirements of the organization from being met?
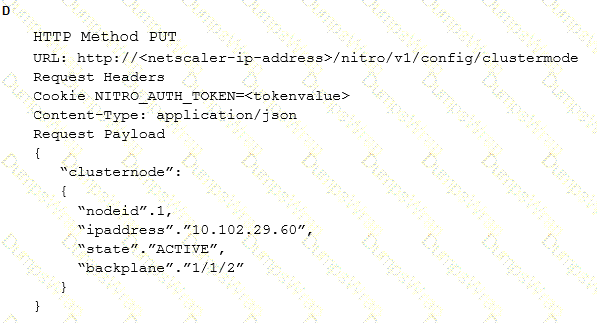
Scenario: A Citrix Architect has sent the following request to the NetScaler:
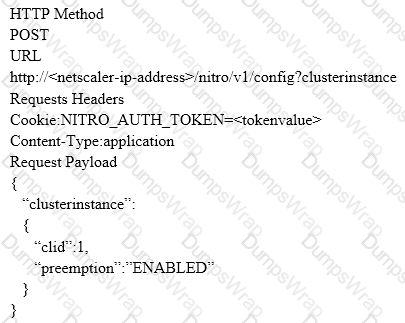
Which response would indicate the successful execution of the NITRO command?
Scenario: A Citrix Architect needs to design a hybrid XenApp and XenDesktop environment which will include as well as resource locations in an on-premises datacenter and Microsoft Azure.
Organizational details and requirements are as follows:
- Active XenApp and XenDesktop Service subscription
- No existing NetScaler deployment
- Minimization of additional costs
- All users should correct directly to the resource locations containing the servers which will host HDX sessions
Click the Exhibit button to view the conceptual environment architecture.
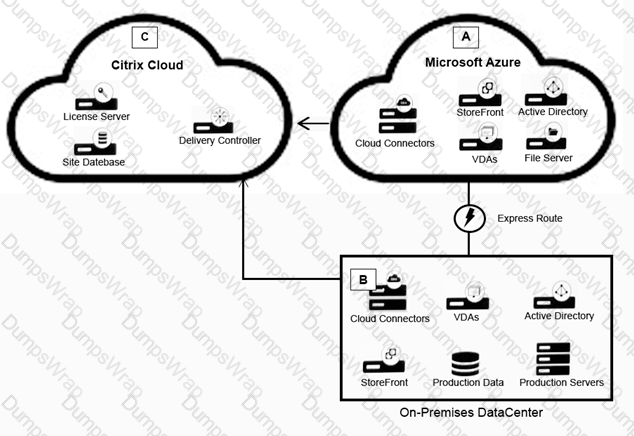
The architect should use___________ in Location A, and should use _______________ in Location B. (Choose the correct option to complete the sentence.)
Scenario: A Citrix Architect needs to design a new NetScaler Gateway deployment to provide secure RDP access to backend Windows machines.
Click the Exhibit button to view additional requirements collected by the architect during the design discussions.
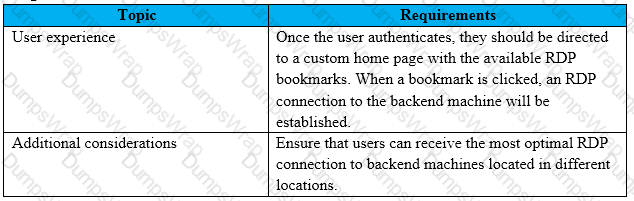
To meet the customer requirements, the architect should deploy the RDP proxy through ______ using a________ solution. (Choose the correct option to complete the sentence.)
Scenario: More than 10,000 users will access a customer’s environment. The current networking infrastructure is capable of supporting the entire workforce of users. However, the number of support staff is limited, and management needs to ensure that they are capable of supporting the full user base.
Which business driver is prioritized, based on the customer’s requirements?
Which three parameters must a Citrix Architect designate when creating a new session policy? (Choose three.)
A Citrix Architect needs to evaluate and define the architecture and operational processes required to implement and maintain the production environment. In which two phases of the Citrix Methodology will the architect define this? (Choose two.)
Scenario: A Citrix Architect needs to design a new Citrix Gateway deployment for a customer. During the design discussions, the architect documents the key
requirements for the Citrix Gateway.
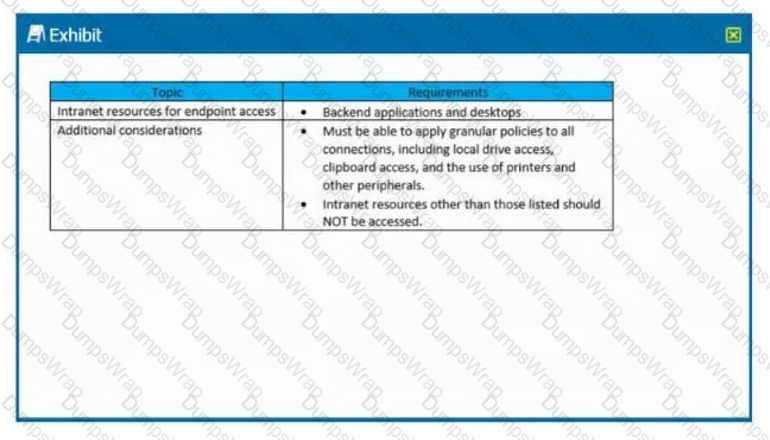
Click the Exhibit button to view the key requirements.
The architect should configure Citrix Gateway for __________________in order to meet the stated requirements. (Choose the correct option to complete the
sentence.)
A Citrix Architect can execute a configuration job using a DeployMasterConfiguration template on a NetScaler_________deployed_________. (Choose the correct option to complete sentence.)
Scenario: The Workspacelab team has configured their Citrix ADC Management and Analytics (Citrix Application Delivery Management) environment. A Citrix Architect needs to log on to the Citrix Application Delivery Management to check the settings.
Which two authentication methods are supported to meet this requirement? (Choose two.)
Scenario: A Citrix Architect and a team of Workspacelab members met to discuss a Citrix ADC design project. They captured the following requirements from this design discussion:
• All three (3) Workspacelab sites (DC, NDR, and DR) will have similar Citrix ADC configurations and design.
• The external Citrix ADC MPX appliances will have Global Server Load Balancing (GSLB) configured and deployed in Active/Active mode.
• ADNS service should be configured on the Citrix ADC to make it authoritative for domain nsg.workspaceIab.com.
• In GSLB deployment, the DNS resolution should be performed to connect the user to the site with least network latency.
• On the internal Citrix ADC, load balancing for StoreFront services, Citrix XML services, and Citrix Director services must be configured.
• On the external Citrix ADC, the Gateway virtual server must be configured in ICA proxy mode.
Which GSLB method should the architect utilize to meet the design requirements?
Scenario: Based on a discussion between a Citrix Architect and a team of Workspacelab members, the MPX Logical layout for Workspacelab has been created across three (3) sites.
They captured the following requirements during the design discussion held for a Citrix ADC design project:
- All three (3) Workspacelab sites (DC, NDR, and DR) will have similar NetScaler configurations and design.
- Both external and internal NetScaler MPX appliances will have Global Server Load Balancing (GSLB) configured and deployed in Active/Passive mode.
- GSLB should resolve both A and AAA DNS queries.
- In the GSLB deployment, the NDR site will act as backup for the DC site, whereas the DR site will act as backup for the NDR site.
- When the external NetScaler replies to DNS traffic coming in through Cisco Firepower IPS, the replies should be sent back through the same path.
- On the internal NetScaler, both the front-end VIP and backend SNIP will be part of the same subnet.
- The external NetScaler will act as default gateway for the backend servers.
- All three (3) sites, DC, NDR, and DR, will have two (2) links to the Internet from different service providers configured in Active/Standby mode.
Which design decision must the architect make the design requirements above?
Scenario: A Citrix Architect needs to configure a full VPN session profile to meet the following requirements:
- Users should be able to send the traffic only for the allowed networks through the VPN tunnel.
- Only the DNS requests ending with the configured DNS suffix workspacelab.com must be sent to NetScaler Gateway.
- If the DNS query does NOT contain a domain name, then DNS requests must be sent to NetScaler gateway.
Which settings will meet these requirements?
Scenario: A Citrix Architect needs to design a new multi-datacenter Citrix ADC deployment. The customer wants Citrix ADC to provide access to various backend resources by using Global Server Load Balancing (GSLB) in an Active-Active deployment. Click the Exhibit button to view additional requirements identified by the architect.
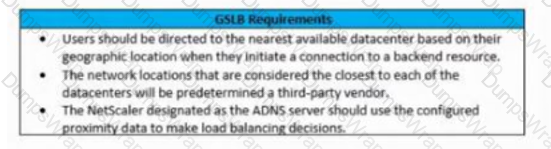
Which GSLB algorithm or method should the architect use for the deployment based on the stated requirements?
Scenario: A Citrix Architect holds a design discussion with a team of Workspacelab members, and they capture the following requirements for the NetScaler design project.
- A pair of NetScaler MPX appliances will be deployed in the DMZ network and another pair in the internal network.
- High availability will be accessible between the pair of NetScaler MPX appliances in the DMZ network.
- Multi-factor authentication must be configured for the NetScaler Gateway virtual server.
- The NetScaler Gateway virtual server is integrated with the StoreFront server.
- Load balancing must be deployed for users from the workspacelab.com domain.
- The workspacelab users should be authenticated using Cert Policy and LDAP.
- All the client certificates must be SHA 256-signed, 2048 bits, and have UserPrincipalName as the subject.
- Single Sign-on must be performed between StoreFront and NetScaler Gateway.
After deployment, the architect observes that LDAP authentication is failing.
Click the Exhibit button to review the output of aaad debug and the configuration of the authentication policy.
Exhibit 1
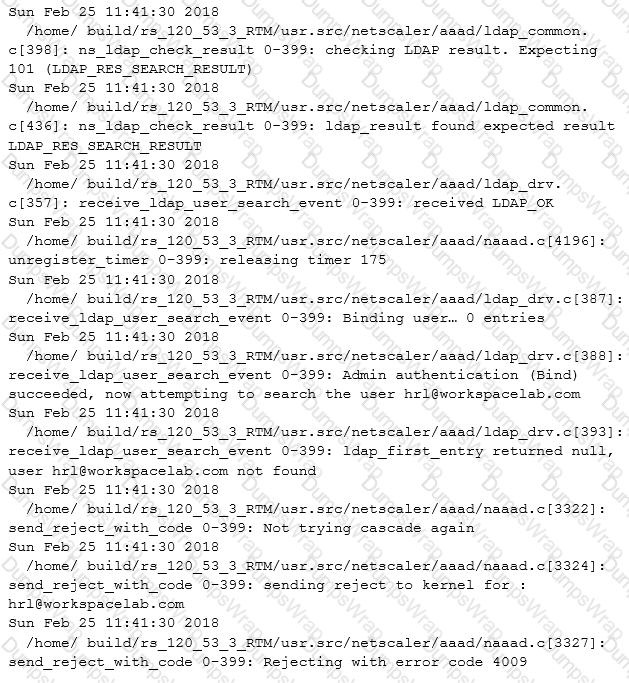
Exhibit 2
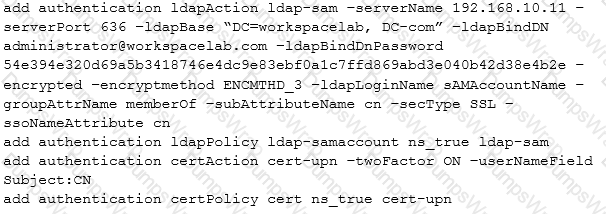
What is causing this issue?
A Citrix Architect needs to configure advanced features of Citrix ADC by using StyleBooks as a resource in the Heat service.
What is the correct sequence of tasks to be completed for configuring Citrix ADC using the Heat stack?
Which two settings must a Citrix Architect enable to deploy a shared VLAN on Citrix ADC VPX instance on an ESX platform? (Choose two.)
Scenario: A Citrix Architect needs to assess an existing on-premises NetScaler deployment which includes Advanced Endpoint Analysis scans. During a previous security audit, the team discovered that certain endpoint devices were able to perform unauthorized actions despite NOT meeting pre-established criteria.
The issue was isolated to several endpoint analysis (EPA) scan settings.
Click the Exhibit button to view the endpoint security requirements and configured EPA policy settings.
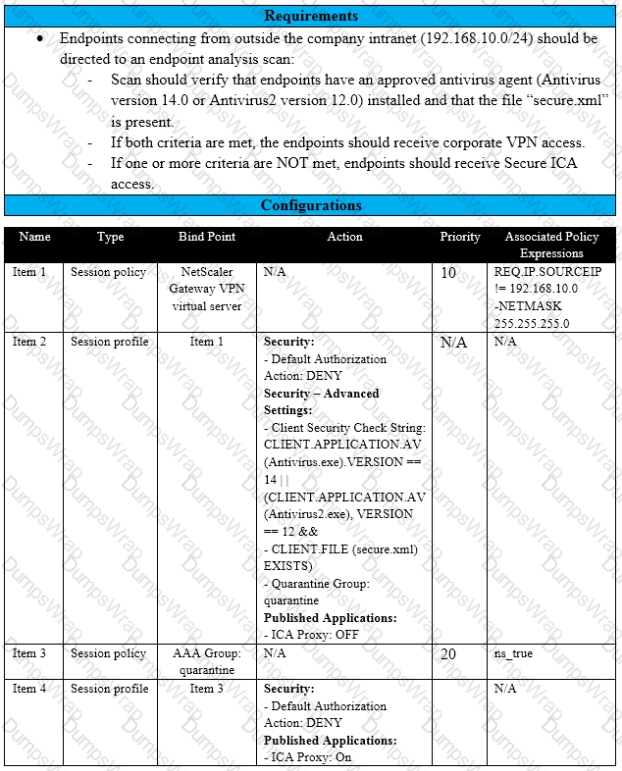
Which setting is preventing the security requirements of the organization from being met?
Which three methods can a Citrix Architect use to assess the capabilities of a network infrastructure? (Choose three.)
Under which two circumstances will a service be taken out of the slow start phase with automated slow start? (Choose two.)
Which parameter indicates the number of current users logged on to the Citrix gateway?
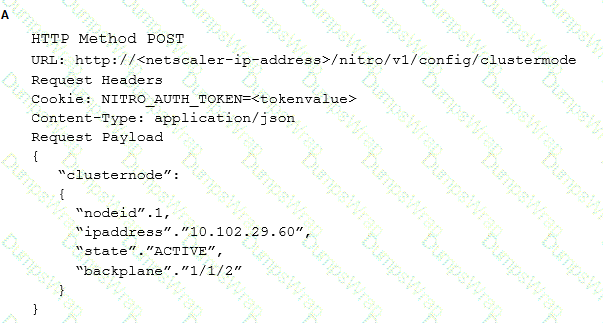
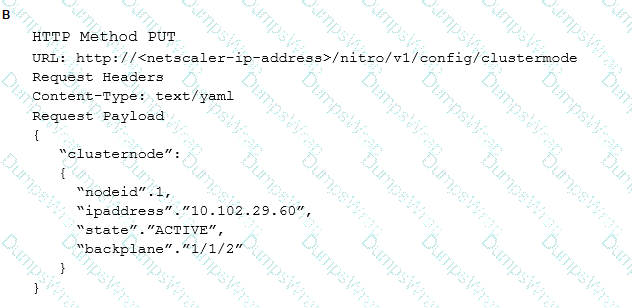
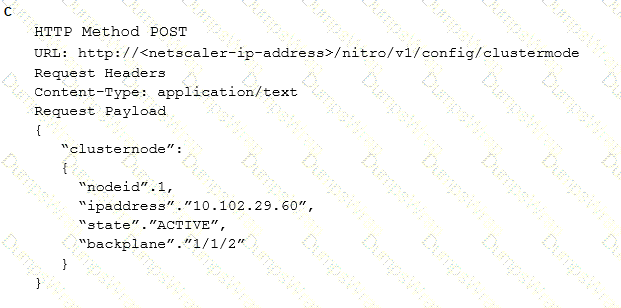
Which request can a Citrix Architect utilize to create a NITRO API command to add a NetScaler appliance with NSIP address 10.102.29.60 to the cluster?
Under which two circumstances will a service be taken out of the slow start phase with automated slow start? (Choose Two)
Scenario: A Citrix Architect needs to assess an existing Citrix ADC configuration. The customer recently found that members of certain administrator groups were receiving permissions on the production Citrix ADC appliances that do NOT align with the designed security requirements. Click the Exhibit button to view the configured command policies for the production Citrix ADC deployment.
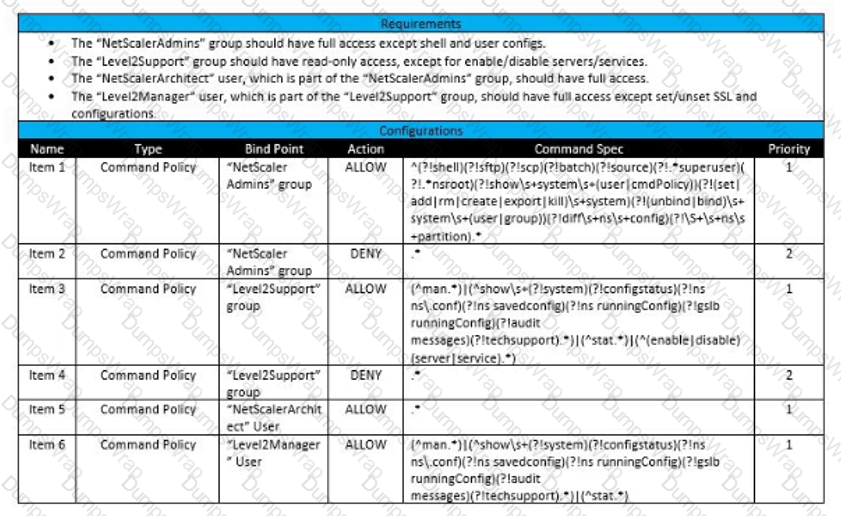
To align the command policy configuration with the security requirements of the organization, the__________for________________should change. (Choose the correct option to complete the sentence.)
Which step does a Citrix Architect need to ensure during the Define phase when following the Citrix Methodology?
Scenario: More than 10,000 users will access a customer’s environment. The current networking infrastructure is capable of supporting the entire workforce of users. However, the number of support staff is limited, and management needs to ensure that they are capable of supporting the full user base.
Which two business driver is prioritized, based on the customer’s requirements?
Scenario: A Citrix Architect needs to deploy three VPX instances on NetScaler SDX 11500 device to meet the following design requirements:
- Three (3) VPX instances must be provisioned on the SDX device.
- Instance 1 must be utilized for deploying NetScaler Gateway virtual server.
- Instance 2 must be utilized for deploying load balancing virtual servers for XML, Director, StoreFront, and Active Directory servers.
- Separate IP address must be utilized for the communication with XenApp environment and LDAP communication.
- Instance 3 must be used for deploying the test environment.
- In the test environment, NetScaler Gateway virtual server, load balancing virtual servers for XML, Director, StoreFront and Active Directory servers must be configured.
How many IP addresses will be required to meet these design requirements?
Scenario: A Citrix Architect has met with a team of Workspacelab members for a design discussion. They have captured the following requirements for the Citrix ADC design project:
• The Citrix Gateway virtual server is integrated with the Citrix Virtual Apps and Desktops environment.
• The authentication must be deployed for the users from the workspacelab.com and vendorlab.com domains.
• The workspacelab users connecting from the internal (workspacelab) network should be authenticated using LDAP.
• The workspacelab users connecting from the external network should be authenticated using LDAP and RADIUS
• The vendorlab users should be authenticated using Active Directory Federation Service.
• The user credentials must NOT be shared between workspacelab and vendor) ab.
• Single Sign-on must be performed between F and Citrix Gateway.
• A domain drop down list must be provided if the user connects to the Citrix Gateway virtual server externally.
• The domain of the user connecting externally must be identified using the domain selected from the domain drop down.
At which bind point should the architect bind the domain drop-down schema policy?
Scenario: A Citrix Architect needs to assess an existing on-premises NetScaler deployment which includes Advanced Endpoint Analysis scans. During a previous security audit, the team discovered that certain endpoint devices were able to perform unauthorized actions despite NOT meeting pre-established criteria.
The issue was isolated to several endpoint analysis (EPA) scan settings.
Click the Exhibit button to view the endpoint security requirements and configured EPA policy settings.
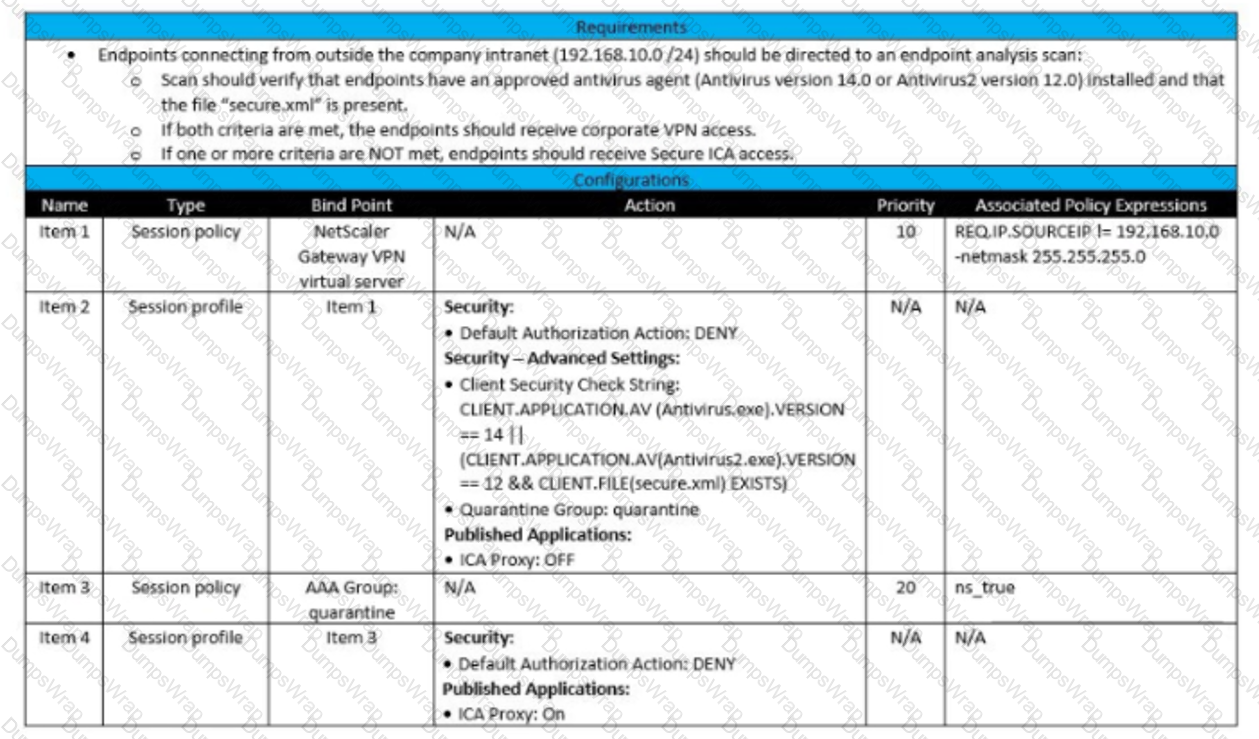
Which setting is preventing the security requirements of the organization from being met?
Scenario: A Citrix Architect needs to design a hybrid XenApp and XenDesktop environment which will include Citrix Cloud as well as resource locations in an on-premises datacenter and Microsoft Azure.
Organizational details and requirements are as follows:
- Active XenApp and XenDesktop Service subscription
- No existing NetScaler deployment
- Global Server Load Balancing is used to direct connection requests to Location B, if the StoreFront server in Location B fails, connections should be directed to Location A.
Click the Exhibit button to view the conceptual environment architecture.
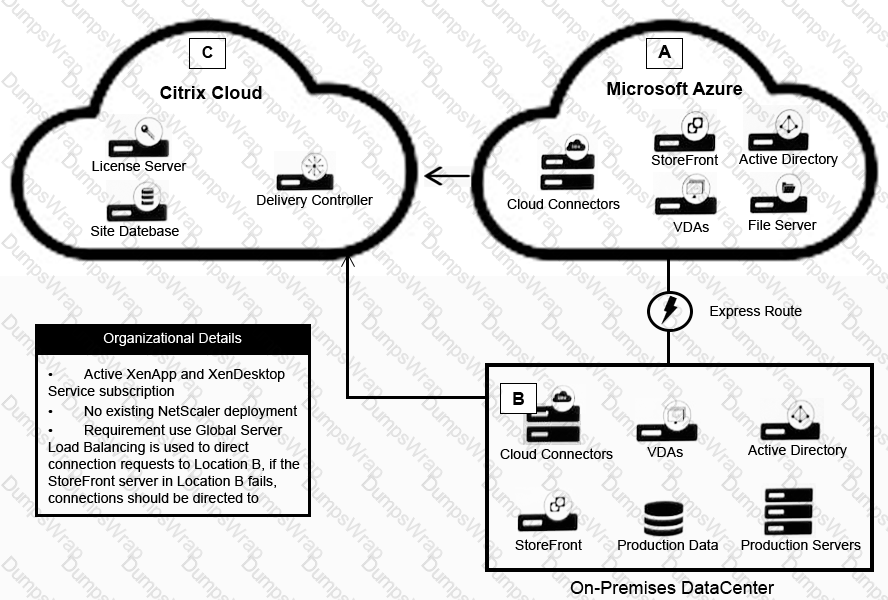
The architect should use _____ in Location A, and should use ________ in Location B. (Choose the correct option to complete the sentence.)
Scenario: A Citrix Architect and a team of Workspacelab members have met for a design discussion about the NetScaler Design Project. They captured the following requirements:
- Two pairs of NetScaler MPX appliances will be deployed in the DMZ network and the internal network.
- High availability will be accessible between the pair of NetScaler MPX appliances in the DMZ network.
- Multi-factor authentication must be configured for the NetScaler Gateway virtual server.
- The NetScaler Gateway virtual server is integrated with XenApp/XenDesktop environment.
- Load balancing must be deployed for the users from the workspacelab.com and vendorlab.com domains.
- The logon page must show the workspacelab logo.
- Certificate verification must be performed to identify and extract the username.
- The client certificate must have UserPrincipalName as a subject.
- All the managed workstations for the workspace users must have a client identifications certificate installed on it.
- The workspacelab users connecting from a managed workstation with a client certificate on it should be authenticated using LDAP.
- The workspacelab users connecting from a workstation without a client certificate should be authenticated using LDAP and RADIUS.
- The vendorlab users should be authenticated using Active Directory Federation Service.
- The user credentials must NOT be shared between workspacelab and vendorlab.
- Single Sign-on must be performed between StoreFront and NetScaler Gateway.
- A domain drop down list must be provided if the user connects to the NetScaler Gateway virtual server externally.
- The domain of the user connecting externally must be identified using the domain selected from the domain drop down list.
On performing the deployment, the architect observes that users are always prompted with two-factor authentication when trying to assess externally from an unmanaged workstation.
Click the exhibit button to view the configuration.
What should the architect do to correct this configuration?
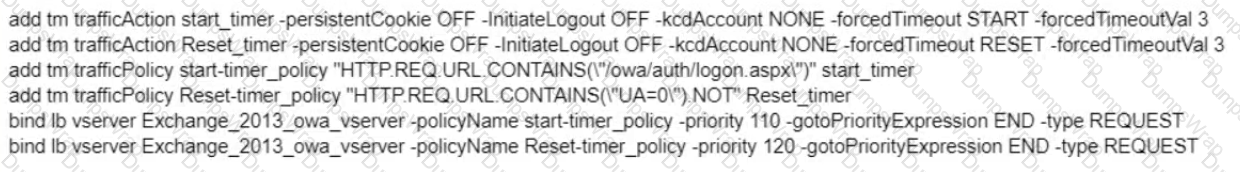 Scenario: A Citrix Architect has executed the following commands on the Citrix ADC:
Scenario: A Citrix Architect has executed the following commands on the Citrix ADC:
In which scenario will the timeout work as configured?
Scenario: A Citrix Architect needs to deploy SAML integration between NetScaler (Identity Provider) and ShareFile (Service Provider). The design requirements for SAML setup are as follows:
- NetScaler must be deployed as the Identity Provider (IDP).
- ShareFile server must be deployed as the SAML Service Provider (SP).
- The users in domain workspacelab.com must be able to perform Single Sign-on to ShareFile after authenticating at the NetScaler.
- The User ID must be UserPrincipalName.
- The User ID and Password must be evaluated by NetScaler against the Active Directory servers SFO-ADS-001 and SFO-ADS-002.
- After successful authentication, NetScaler creates a SAML Assertion and passes it back to ShareFile.
- Single Sign-on must be performed.
- SHA 1 algorithm must be utilized.
The verification environment details are as follows:
- Domain Name: workspacelab.com
- NetScaler AAA virtual server URL https://auth.workspacelab.com
- ShareFile URL https://sharefile.workspacelab.com
Which SAML IDP action will meet the design requirements?
Scenario: A Citrix Architect needs to assess a Citrix Gateway deployment that was recently completed by a customer and is currently in pre-production testing The Citrix Gateway needs to use ICA proxy to provide access to a Citrix Virtual Apps and Citrix Virtual Desktops environment. During the assessment, the customer informs the architect that users are NOT able to launch published resources using the Gateway virtual server.
Click the Exhibit button to view the troubleshooting details collected by the customer.
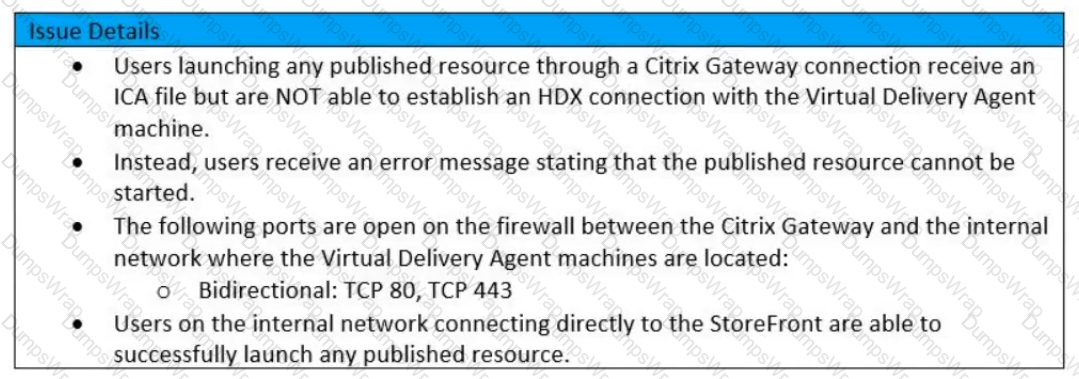
Which two reasons could cause this issue? (Choose two)
What can help a Citrix Architect prepare to discuss time scales and resource requirements?
Scenario: A Citrix Architect needs to assess an existing NetScaler gateway deployment. During the assessment, the architect collects key requirements for different user groups, as well as the current session profile settings that are applied to those users.
Click the Exhibit button to view the information collected by the architect.
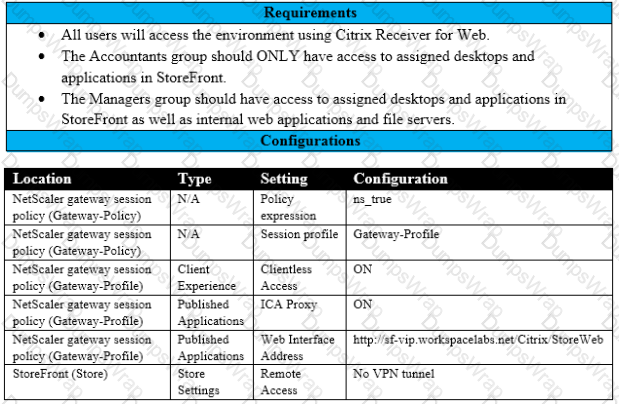
Which configuration should the architect make to meet these requirements?
Scenario: A Citrix Architect needs to deploy a Citrix ADC appliance for Workspacelab, which will provide application load balancing services to Partnerlab and Vendorlab.
The setup requirements are as follows:
- A pair of Citrix ADC MPX appliances will be deployed in the DMZ network.
- High availability will be accessible on the Citrix ADC MPX in the DMZ Network.
- Load balancing should be performed for the mail servers for Partnerlab and Vendorlab.
- The traffic for both of the organizations must be isolated.
- Separate Management accounts must be available for each client.
- The load-balancing IP addresses must be identical.
- A separate VLAN must be utilized for communication for each client.
Which solution can the architect utilize to meet the requirements?
Scenario: A Citrix Architect has setup Citrix ADC MPX devices in high availability mode with version 12.0.53.13 nc. These are placed behind a Cisco ASA 5505 firewall. The Cisco ASA firewall is configured to block traffic using access control lists. The network address translation (NAT) is also performed on the firewall. The following requirements were captured by the architect during the discussion held as part of the Citrix ADC security implementation project with the customer's security team: The Citrix ADC MPX device:
- should monitor the rate of traffic either on a specific virtual entity or on the device. It should be able to mitigate the attacks from a hostile client sending a flood of requests. The Citrix ADC device should be able to stop the HTTP. TOP, and DNS based requests.
- needs to protect backend servers from overloading.
- needs to queue all the incoming requests on the virtual server level instead of the service level.
- should provide access to resources on the basis of priority.
- should provide protection against well-known Windows exploits, virus-infected personal computers, centrally managed automated botnets. compromised webservers, known spammersThackers. and phishing proxies.
- should provide flexibility to enforce the desired level of security check inspections for the requests originating from a specific geolocation database.
- should block the traffic based on a predetermined header length, URL length, and cookie length.The device should ensure that characters such as a single straight quote (') backslash (); and semicolon (;) are either blocked, transformed, or dropped while being sent to the backend server.
Which security feature should the architect implement to meet these requirements?
Scenario: A Citrix Architect has implemented two high availability pairs of MPX 5500 and MPX 11500 devices respectively with 12.0.53.13 nc version. The Citrix ADC devices are set up to handle Citrix Gateway. Load Balancing. Application Firewall, and Content Switching. The Workspacelab infrastructure is set up to be monitored with Citrix Application Delivery Management version 12.0.53.13 nc by the Workspacelab administrators. The Workspacelab team wants to implement one more pair(s) of Citrix ADC MPX 7500 devices with version 12.0.53.13 nc.
The Citrix consulting team has assigned the task to implement these Citrix ADC devices in the infrastructure and set them up to be monitored and managed by Citrix ADC Management and Analytics {Citrix Application Delivery Management).
The following are the requirements that were discussed during the project initiation call:
- Citrix Application Delivery Management should be configured to get the infrastructure information under sections such as HDX Insight, WEB Insight, and Security Insight.
- Configuration on the new MPX devices should be identical to that of MPX 11500 devices.
- Configuration changes after the deployment and initial setup should be optimized using Citrix Application Delivery Management.
- Citrix Application Delivery Management should be utilized to configure templates that can be utilized by the Workspacelab team in future deployments.
- As per the requirement from the Workspacelab team, Citrix Application Delivery Management should store the audited data for only 15 days.
However, the architect is NOT able to view any Information under Analytics. What should the architect do to fix this issue?
Scenario: A Citrix Architect needs to assess a Citrix Gateway deployment that was recently completed by a customer and is currently in pre-production testing. The Citrix Gateway needs to use ICA proxy to provide access to a Citrix Virtual Apps and Citrix Virtual Desktops environment. During the assessment, the customer informs the architect that users are NOT able to launch published resources using the Gateway virtual server.
Click the Exhibit button to view the troubleshooting details collected by the customer.
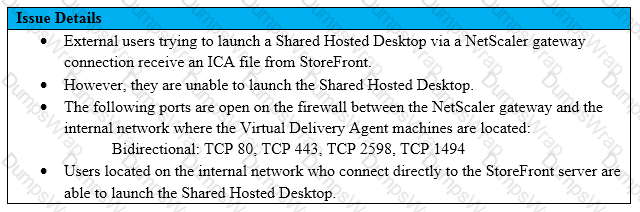
What is the cause of this issue?
Scenario: A Citrix Architect needs to plan for a customer environment in which more than 10,000 users will need access. The networking infrastructure needs to be able to handle the expected usage.
Which business driver should be prioritized based on the customer’s requirement?
Which two parameters must a Citrix Architect specify in the configuration job to replicate a specific configuration snippet from one Crtnx ADC instance to multiple instances? (Choose two.)

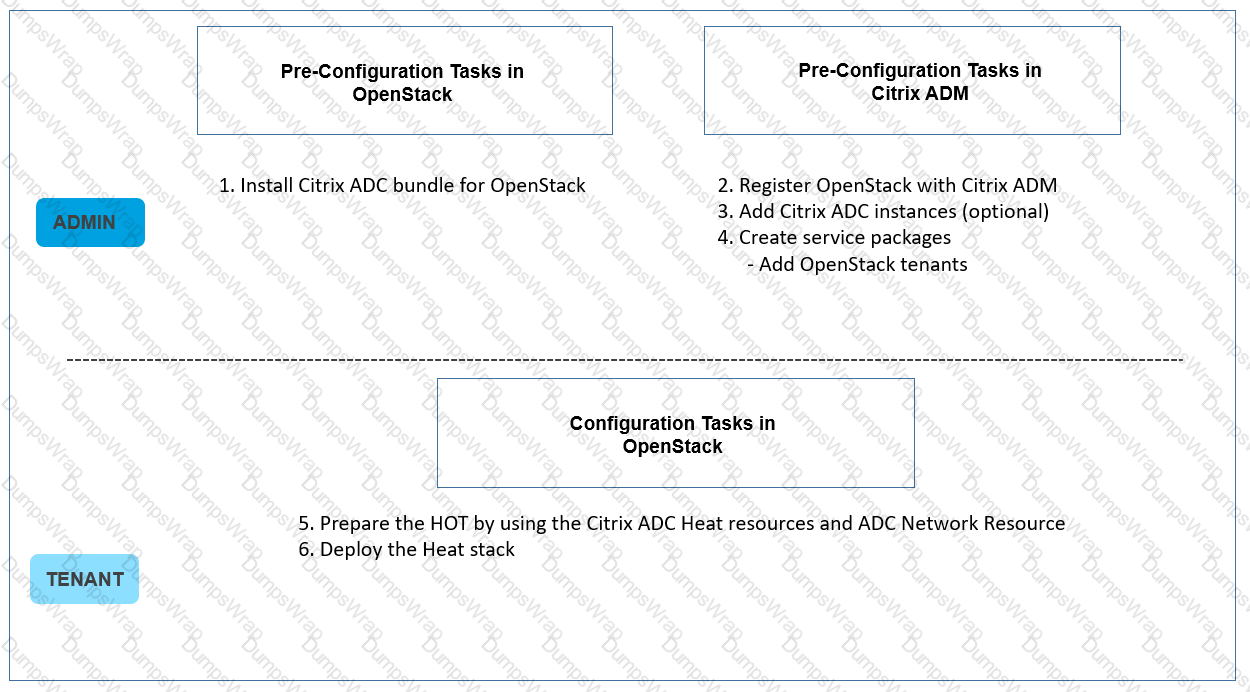 Workflow to configure ADC instances using Heat
Workflow to configure ADC instances using Heat