CompTIA Security+ Exam 2026 Questions and Answers
An organization is looking to optimize its environment and reduce the number of patches necessary for operating systems. Which of the following will best help to achieve this objective?
A small business uses kiosks on the sales floor to display product information for customers. A security team discovers the kiosks use end-of-life operating systems. Which of the following is the security team most likely to document as a security implication of the current architecture?
A security analyst is investigating an application server and discovers that software on the server is behaving abnormally. The software normally runs batch jobs locally and does not generate traffic, but the process is now generating outbound traffic over random high ports. Which of the following vulnerabilities has likely been exploited in this software?
A systems administrator creates a script that validates OS version, patch levels, and installed applications when users log in. Which of the following examples best describes the purpose of this script?
Which of the following best describes a common use of OSINT?
Which of the following scenarios describes a possible business email compromise attack?
A security analyst receives an alert that there was an attempt to download known malware. Which of the following actions would allow the best chance to analyze the malware?
Which of the following best represents how frequently an incident is expected to happen each year?
The help desk receives multiple calls that machines with an outdated OS version are running slowly. Several users are seeing virus detection alerts. Which of the following mitigation techniques should be reviewed first?
A security analyst receives an alert from a corporate endpoint used by employees to issue visitor badges. The alert contains the following details:
Which of the following best describes the indicator that triggered the alert?
A government worker secretly copies classified files that contain defense tactics information to an external drive. The government worker then gives the external drive to a corrupt organization. Which of the following best describes the motivation of the worker?
A systems administrator is concerned users are accessing emails through a duplicate site that is not run by the company. Which of the following is used in this scenario?
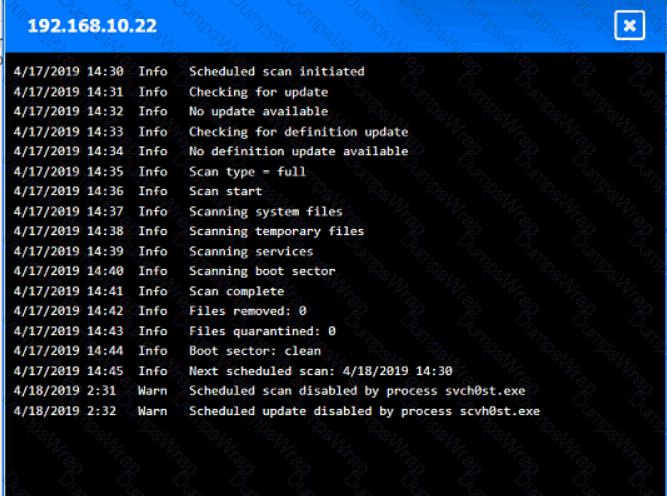
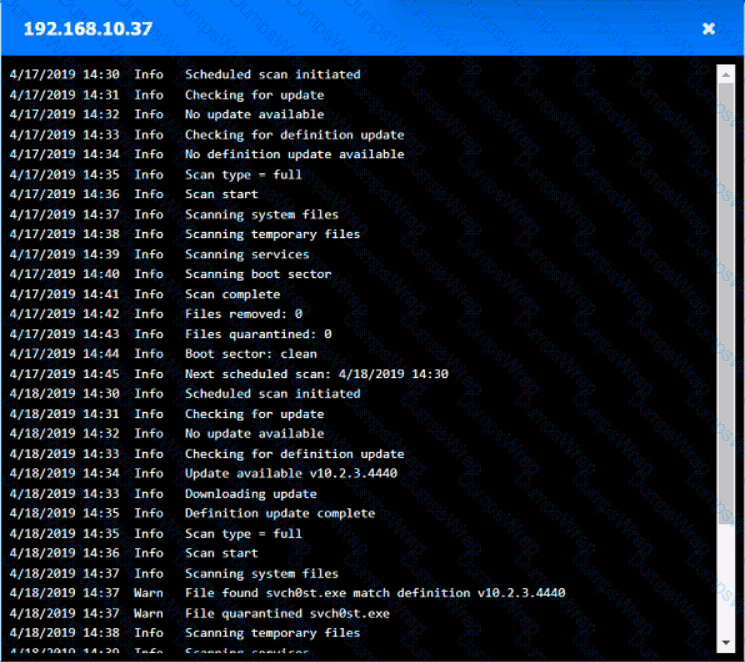
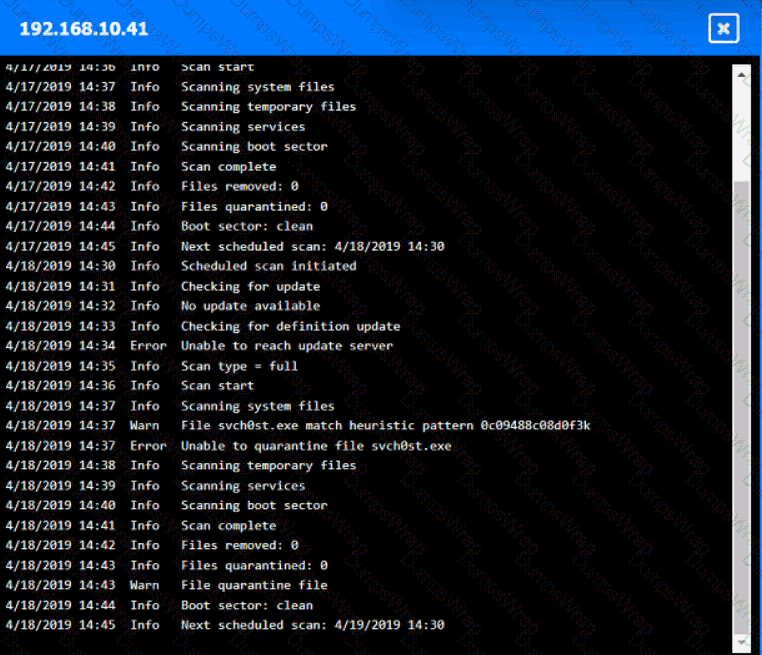
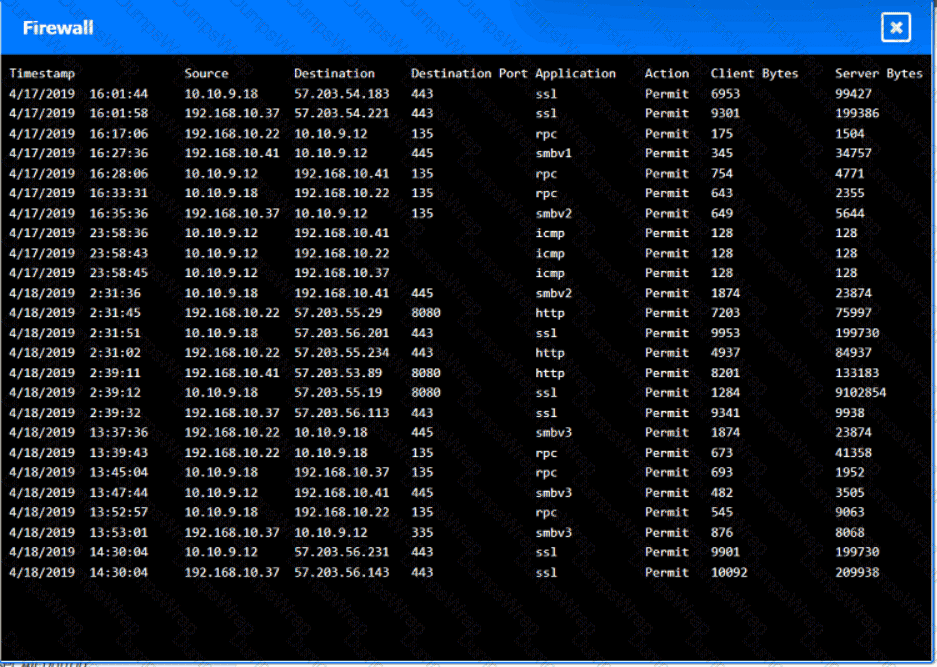
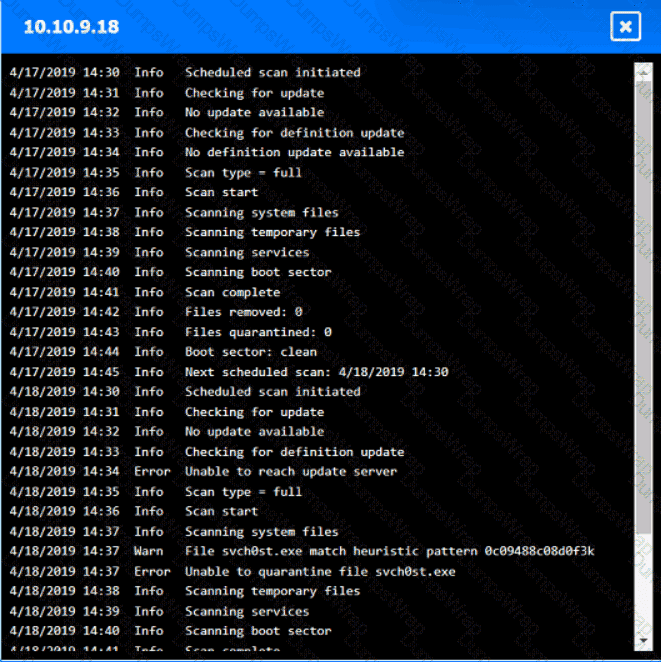
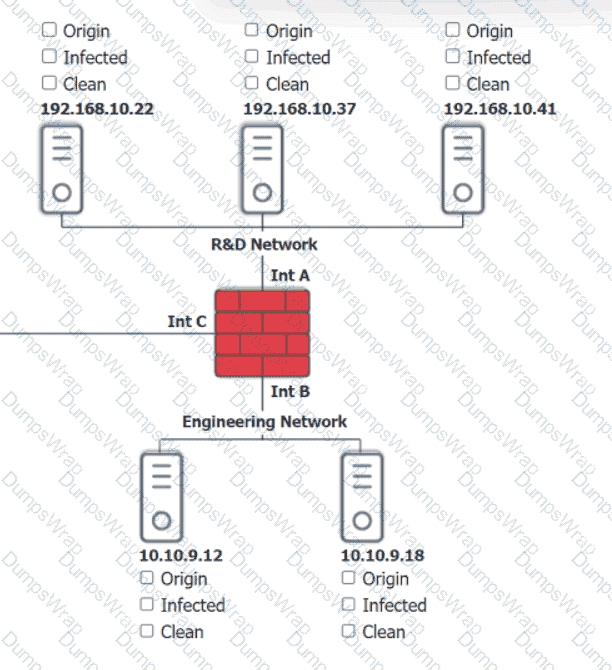
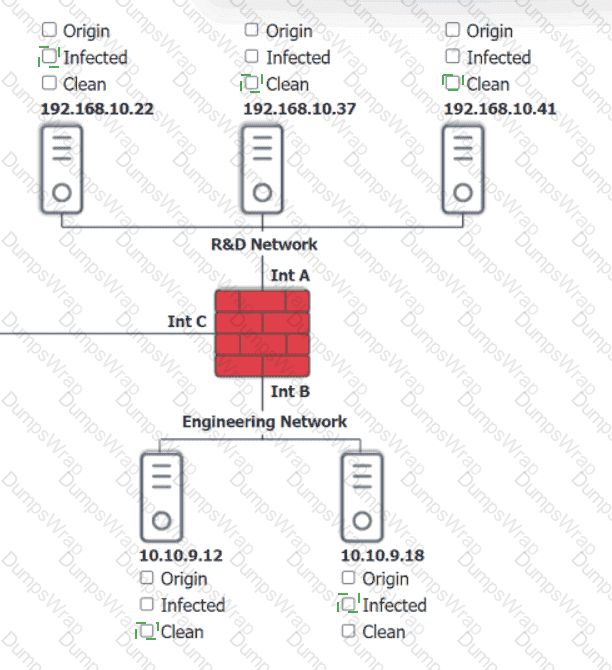
You are security administrator investigating a potential infection on a network.
Click on each host and firewall. Review all logs to determine which host originated the Infecton and then deny each remaining hosts clean or infected.

An organization ' s web servers host an online ordering system. The organization discovers that the servers are vulnerable to a malicious JavaScript injection, which could allow attackers to access customer payment information. Which of the following mitigation strategies would be most effective for preventing an attack on the organization ' s web servers? (Select two).
A Chief Information Security Officer (CISO) wants to explicitly raise awareness about the increase of ransomware-as-a-service in a report to the management team. Which of the following best describes the threat actor in the CISO ' s report?
Which of the following concepts protects sensitive information from unauthorized disclosure?
A company performs a risk assessment on the information security program each year. Which of the following best describes this risk assessment?
An employee asks a security analyst to scan a suspicious email that contains a link to a file on a file-sharing site. The analyst determines that the file is safe after downloading and scanning the file with antivirus software. When the employee opens the file, their device is infected with ransomware. Which of the following steps should the analyst have taken?
A security administrator receives multiple reports about the same suspicious email. Which of the following is the most likely reason for the malicious email ' s continued delivery?
A new security regulation was announced that will take effect in the coming year. A company must comply with it to remain in business. Which of the following activities should the company perform next?
Which of the following security control types does an acceptable use policy best represent?
Which of the following is a security benefit of an effective IT asset tracking system?
Which of the following should be used to ensure that a new software release has not been modified before reaching the user?
Which of the following should be used to aggregate log data in order to create alerts and detect anomalous activity?
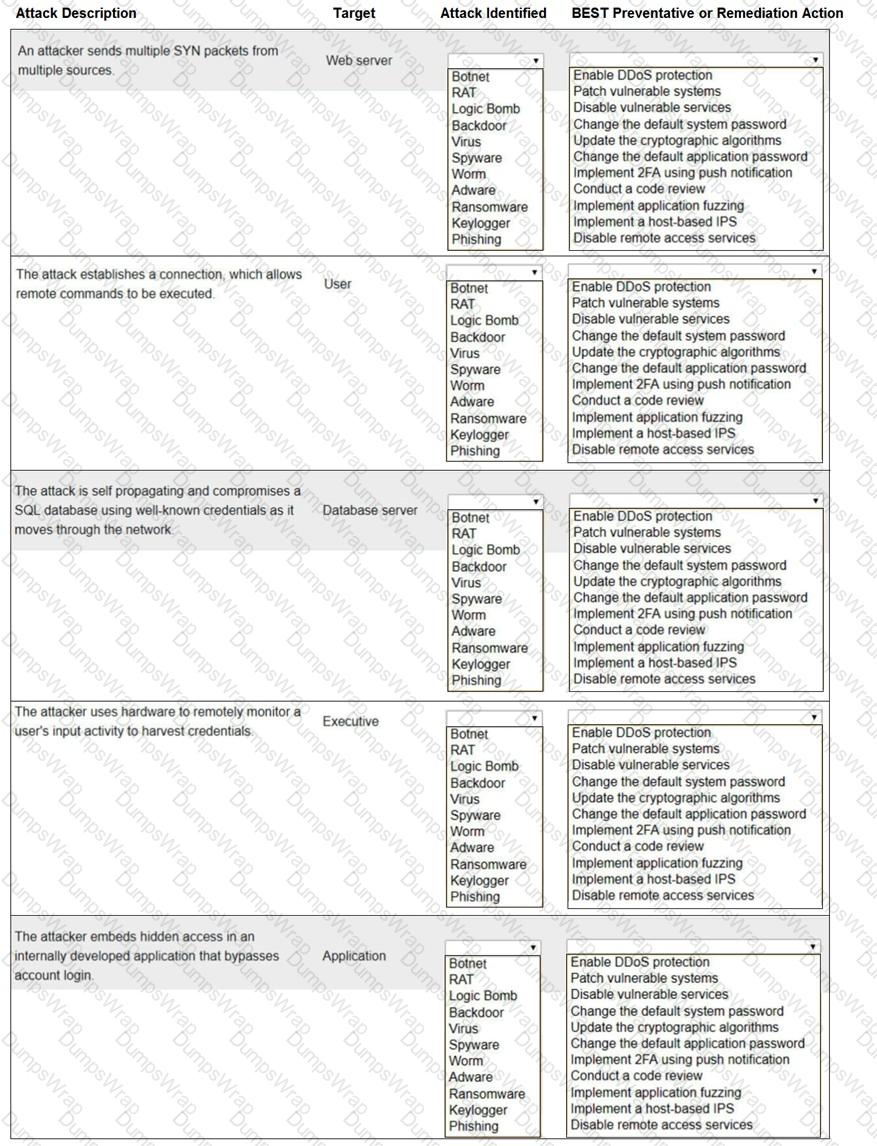
Select the appropriate attack and remediation from each drop-down list to label the corresponding attack with its remediation.
INSTRUCTIONS
Not all attacks and remediation actions will be used.
If at any time you would like to bring back the initial state of the simu-lation, please click the Reset All button.
Which of the following would most likely be deployed to obtain and analyze attacker activity and techniques?
A company performs risk analysis on its equipment and estimates it will experience about ten incidents over a five-year period. Which of the following is the correct ARO for the equipment?
Which of the following is the most important element when defining effective security governance?
While investigating a possible incident, a security analyst discovers the following log entries:
67.118.34.157 ----- [28/Jul/2022:10:26:59 -0300] " GET /query.php?q-wireless%20headphones / HTTP/1.0 " 200 12737
132.18.222.103 ----[28/Jul/2022:10:27:10 -0300] " GET /query.php?q=123 INSERT INTO users VALUES( ' temp ' , ' pass123 ' )# / HTTP/1.0 " 200 935
12.45.101.121 ----- [28/Jul/2022:10:27:22 -0300] " GET /query.php?q=mp3%20players I HTTP/1.0 " 200 14650
Which of the following should the analyst do first?
An organization recently started hosting a new service that customers access through a web portal. A security engineer needs to add to the existing security devices a new solution to protect this new service. Which of the following is the engineer most likely to deploy?
A network administrator deploys an FDE solution on all end user workstations. Which of the following data protection strategies does this describe?
Which of the following can best protect against an employee inadvertently installing malware on a company system?
Which of the following techniques would identify whether data has been modified in transit?
Which of the following is a benefit of launching a bug bounty program? (Select two)
An organization wants a third-party vendor to do a penetration test that targets a specific device. The organization has provided basic information about the device. Which of the following best describes this kind of penetration test?
A Chief Security Officer signs off on a request to allow inbound SMB and RDP from the internet to a single VLAN. Which of the following is the most likely explanation for this activity?
Which of the following considerations is the most important for an organization to evaluate as it establishes and maintains a data privacy program?
A systems administrator is auditing all company servers to ensure. They meet the minimum security baseline While auditing a Linux server, the systems administrator observes the /etc/shadow file has permissions beyond the baseline recommendation. Which of the following commands should the systems administrator use to resolve this issue?
A client demands at least 99.99% uptime from a service provider ' s hosted security services. Which of the following documents includes the information the service provider should return to the client?
As part of new compliance audit requirements, multiple servers need to be segmented on different networks and should be reachable only from authorized internal systems. Which of the following would meet the requirements?
Which of the following roles, according to the shared responsibility model, is responsible for securing the company’s database in an IaaS model for a cloud environment?
Which of the following architectures is most suitable to provide redundancy for critical business processes?
An unknown source has attacked an organization’s network multiple times. The organization has a firewall but no other source of protection against these attacks. Which of the following is the best security item to add?
Which of the following activities is the first stage in the incident response process?
A new corporate policy requires all staff to use multifactor authentication to access company resources. Which of the following can be utilized to set up this form of identity and access management? (Select two)
A company evaluates several options that would allow employees to have remote access to the network. The security team wants to ensure the solution includes AAA to comply with internal security policies. Which of the following should the security team recommend?
An organization is implementing a COPE mobile device management policy. Which of the following should the organization include in the COPE policy? (Select two).
Which of the following control types describes an alert from a SIEM tool?
A Chief Information Security Officer (CISO) has developed information security policies that relate to the software development methodology. Which of the following would the CISO most likely include in the organization ' s documentation?
Which of the following best explains a core principle of a Zero Trust security model?
Which of the following is a benefit of an RTO when conducting a business impact analysis?
The management team wants to assess the cybersecurity team ' s readiness to respond to a threat scenario. Which of the following will adequately assess and formalize a response within a short time?
While a school district is performing state testing, a security analyst notices all internet services are unavailable. The analyst discovers that ARP poisoning is occurring on the network and then terminates access for the host. Which of the following is most likely responsible for this malicious activity?
Which of the following describes the process of concealing code or text inside a graphical image?
Which of the following methods to secure data is most often used to protect data in transit?
Which of the following best describe a penetration test that resembles an actual external attach?
Which of the following is the primary purpose of a service that tracks log-ins and time spent using the service?
A vendor salesperson is a personal friend of a company’s Chief Financial Officer (CFO). The company recently made a large purchase from the vendor, which was directly approved by the CFO. Which of the following best describes this situation?
A company hired a consultant to perform an offensive security assessment covering penetration testing and social engineering.
Which of the following teams will conduct this assessment activity?
A systems administrator wants to use a technical solution to explicitly define file permissions for the entire team. Which of the following should the administrator implement?
Which of the following should be used to ensure an attacker is unable to read the contents of a mobile device ' s drive if the device is lost?
A network security analyst monitors the network’s IDS, which has flagged unusual activity. The IDS has detected multiple login attempts to a database server within a short period. These attempts come from various IP addresses that are not normally recognized by the network’s usual traffic patterns. Each attempt uses the same username and password. Based on the following log output (corrected formatting for readability):
2025-04-10 14:22:01.4532 — Source IP: 192.168.15.101 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:02.1122 — Source IP: 192.168.15.102 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:02.7835 — Source IP: 192.168.15.103 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:03.5637 — Source IP: 192.168.15.104 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:04.9474 — Source IP: 192.168.15.105 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:05.5673 — Source IP: 192.168.15.106 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:06.1573 — Source IP: 192.168.15.107 — Status: Failed — User: JDoe — Action: Login Attempt
2025-04-10 14:22:07.7462 — Source IP: 192.168.15.108 — Status: Failed — User: JDoe — Action: Login Attempt
Which of the following types of network attacks is most likely occurring?
Which of the following would help ensure a security analyst is able to accurately measure the overall risk to an organization when a new vulnerability is disclosed?
A systems administrator notices that one of the systems critical for processing customer transactions is running an end-of-life operating system. Which of the following techniques would increase enterprise security?
Which of the following would be the most appropriate way to protect data in transit?
Which of the following vulnerabilities is exploited when an attacker overwrites a register with a malicious address?
A network manager wants to protect the company ' s VPN by implementing multifactor authentication that uses:
. Something you know
. Something you have
. Something you are
Which of the following would accomplish the manager ' s goal?
An administrator must implement a solution that provides security and network connectivity between two companies. Which of the following infrastructure solutions is the best for this purpose?
Which of the following metrics impacts the backup schedule as part of the BIA?
A systems administrator receives the following alert from a file integrity monitoring tool:
The hash of the cmd.exe file has changed.
The systems administrator checks the OS logs and notices that no patches were applied in the last two months. Which of the following most likely occurred?
A customer reports that software the customer downloaded from a public website has malware in it. However, the company that created the software denies any malware in its software at delivery time. Which of the following techniques will address this concern?
Which of the following techniques would attract the attention of a malicious attacker in an insider threat scenario?
Which of the following security controls would best guard a payroll system against insider manipulation threats?
Which of the following is the first step to take when creating an anomaly detection process?
A company decided to reduce the cost of its annual cyber insurance policy by removing the coverage for ransomware attacks.
Which of the following analysis elements did the company most likely use in making this decision?
Which of the following can be used to identify potential attacker activities without affecting production servers?
A bank set up a new server that contains customers ' Pll. Which of the following should the bank use to make sure the sensitive data is not modified?
Which of the following technologies can achieve microsegmentation?
Which of the following would best prepare a security team for a specific incident response scenario?
Which of the following is the most relevant reason a DPO would develop a data inventory?
An organization plans to expand its operations internationally and needs to keep data at the new location secure. The organization wants to use the most secure architecture model possible. Which of the following models offers the highest level of security?
A security administrator is reissuing a former employee ' s laptop. Which of the following is the best combination of data handling activities for the administrator to perform? (Select two).
A security analyst finds a rogue device during a monthly audit of current endpoint assets that are connected to the network. The corporate network utilizes 002.1X for access control. To be allowed on the network, a device must have a Known hardware address, and a valid user name and password must be entered in a captive portal. The following is the audit report:
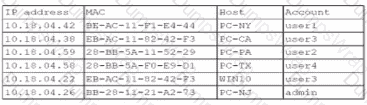
Which of the following is the most likely way a rogue device was allowed to connect?
In which of the following will unencrypted PLC management traffic most likely be found?
An organization would like to store customer data on a separate part of the network that is not accessible to users on the main corporate network. Which of the following should the administrator use to accomplish this goal?
A security company informs its customers of a new vulnerability that affects web applications. The vulnerability does not have an available patch at the moment. Which of the following best describes this vulnerability?
Which of the following are the best methods for hardening end user devices? (Select two)
Which of the following is the best way to consistently determine on a daily basis whether security settings on servers have been modified?
Which of the following would be the greatest concern for a company that is aware of the consequences of non-compliance with government regulations?
After a company was compromised, customers initiated a lawsuit. The company ' s attorneys have requested that the security team initiate a legal hold in response to the lawsuit. Which of the following describes the action the security team will most likely be required to take?
Which of the following actors attacking an organization is the most likely to be motivated by personal beliefs?
A company needs to provide administrative access to internal resources while minimizing the traffic allowed through the security boundary. Which of the following methods is most secure?
A remote employee navigates to a shopping website on their company-owned computer. The employee clicks a link that contains a malicious file. Which of the following would prevent this file from downloading?
A data administrator is configuring authentication for a SaaS application and would like to reduce the number of credentials employees need to maintain. The company prefers to use domain credentials to access new SaaS applications. Which of the following methods would allow this functionality?
A penetration tester begins an engagement by performing port and service scans against the client environment according to the rules of engagement. Which of the following reconnaissance types is the tester performing?
Which of the following consequences would a retail chain most likely face from customers in the event the retailer is non-compliant with PCI DSS?
Which of the following is best used to detect fraud by assigning employees to different roles?
An unexpected and out-of-character email message from a Chief Executive Officer’s corporate account asked an employee to provide financial information and to change the recipient ' s contact number. Which of the following attack vectors is most likely being used?
An organization is developing a security program that conveys the responsibilities associated with the general operation of systems and software within the organization. Which of the following documents would most likely communicate these expectations?
Which of the following activities would involve members of the incident response team and other stakeholders simul-ating an event?
A few weeks after deploying additional email servers, employees complain that messages are being marked as spam. Which needs to be updated?
A company prepares for an upcoming regulatory audit. The company wants to perform a gap analysis in the most cost-effective way. Which of the following will help the company achieve this goal?
After a security awareness training session, a user called the IT help desk and reported a suspicious call. The suspicious caller stated that the Chief Financial Officer wanted credit card information in order to close an invoice. Which of the following topics did the user recognize from the training?
A security team wants to work with the development team to ensure WAF policies are automatically created when applications are deployed. Which concept describes this capability?
A company’s web filter is configured to scan the URL for strings and deny access when matches are found. Which of the following search strings should an analyst employ to prohibit access to non-encrypted websites?
A security analyst must prevent remote users from accessing malicious URLs. The sites need to be checked inline for reputation, content, or categorization. Which of the following technologies will help secure the enterprise?
Which of the following security controls are a company implementing by deploying HIPS? (Select two).
A network administrator wants to ensure that network traffic is highly secure while in transit. Which of the following actions best describes the actions the network administrator should take?
An organization has been experiencing issues with deleted network share data and improperly assigned permissions. Which of the following would best help track and remediate these issues?
Which of the following should an organization use to protect its environment from external attacks conducted by an unauthorized hacker?
An IT manager is putting together a documented plan describing how the organization will keep operating in the event of a global incident. Which of the following plans is the IT manager creating?
Which of the following describes the maximum allowance of accepted risk?
An administrator is creating a secure method for a contractor to access a test environment. Which of the following would provide the contractor with the best access to the test environment?
A technician wants to improve the situational and environmental awareness of existing users as they transition from remote to in-office work. Which of the following is the best option?
A business needs a recovery site but does not require immediate failover. The business also wants to reduce the workload required to recover from an outage. Which of the following recovery sites is the best option?
A company wants to improve the availability of its application with a solution that requires minimal effort in the event a server needs to be replaced or added. Which of the following would be the best solution to meet these objectives?
Which of the following most securely protects data at rest?
Which of the following explains how organizations benefit from SCAP?
Which of the following practices would be best to prevent an insider from introducing malicious code into a company ' s development process?
Which of the following strategies most effectively protects sensitive data at rest in a database?
A systems administrator wants to prevent users from being able to access data based on their responsibilities. The administrator also wants to apply the required access structure via a simplified format. Which of the following should the administrator apply to the site recovery resource group?
Users at a company are reporting they are unable to access the URL for a new retail website because it is flagged as gambling and is being blocked.
Which of the following changes would allow users to access the site?
A security analyst discovers that a large number of employee credentials had been stolen and were being sold on the dark web. The analyst investigates and discovers that some hourly employee credentials were compromised, but salaried employee credentials were not affected.
Most employees clocked in and out while they were Inside the building using one of the kiosks connected to the network. However, some clocked out and recorded their time after leaving to go home. Only those who clocked in and out while Inside the building had credentials stolen. Each of the kiosks are on different floors, and there are multiple routers, since the business segments environments for certain business functions.
Hourly employees are required to use a website called acmetimekeeping.com to clock in and out. This website is accessible from the internet. Which of the following Is the most likely reason for this compromise?
An organization experiences a compromise in a cloud-hosted solution that contains customer information. Which of the following strategies will help determine the sensitivity level of the breach?
Which of the following aspects of the data management life cycle is most directly impacted by local and international regulations?
Which of the following would be the best way to block unknown programs from executing?
A security analyst is reviewing logs to identify the destination of command-and-control traffic originating from a compromised device within the on-premises network. Which of the following is the best log to review?
Which of the following best explains a concern with OS-based vulnerabilities?
Which of the following data protection strategies can be used to confirm file integrity?
Which of the following best represents an application that does not have an on-premises requirement and is accessible from anywhere?
A group of developers has a shared backup account to access the source code repository. Which of the following is the best way to secure the backup account if there is an SSO failure?
An administrator has configured a quarantine subnet for all guest devices that connect to the network. Which of the following would be best for the security team to configure on the MDM before allowing access to corporate resources?
An administrator installs an SSL certificate on a new system. During testing, errors indicate that the certificate is not trusted. The administrator has verified with the issuing CA and has validated the private key. Which of the following should the administrator check for next?
In order to strengthen a password and prevent a hacker from cracking it, a random string of 36 characters was added to the password. Which of the following best describes this technique?
Which of the following best explains how tokenization helps protect sensitive data?
Which of the following security principles most likely requires validation before allowing traffic between systems?
Employees in the research and development business unit receive extensive training to ensure they understand how to best protect company data. Which of the following is the type of data these employees are most likely to use in day-to-day work activities?
A security analyst needs to improve the company’s authentication policy following a password audit. Which of the following should be included in the policy? (Select two).
A security technician determines that no additional patches can be applied to an application and the risks of operating as such must be accepted. Additionally, only a limited number of network services should utilize the application. Which of the following best describes this type of mitigation?
Which of the following enables the use of an input field to run commands that can view or manipulate data?
Which of the following describes a situation where a user is authorized before being authenticated?
A company is required to use certified hardware when building networks. Which of the following best addresses the risks associated with procuring counterfeit hardware?
Which of the following would most likely be used by attackers to perform credential harvesting?
Which of the following is a preventive physical security control?
During a security incident, the security operations team identified sustained network traffic from a malicious IP address:
10.1.4.9. A security analyst is creating an inbound firewall rule to block the IP address from accessing the organization’s network. Which of the following fulfills this request?
A systems administrator is working on a solution with the following requirements:
Provide a secure zone.
Enforce a company-wide access control policy.
Reduce the scope of threats.
Which of the following is the systems administrator setting up?
A company is utilizing an offshore team to help support the finance department. The company wants to keep the data secure by keeping it on a company device but does not want to provide equipment to the offshore team. Which of the following should the company implement to meet this requirement?
An organization recently updated its security policy to include the following statement:
Regular expressions are included in source code to remove special characters such as $, |, ;. & , `, and ? from variables set by forms in a web application.
Which of the following best explains the security technique the organization adopted by making this addition to the policy?
A company wants to minimize the chance of its outgoing marketing emails getting flagged as spam. The company decides to list the email servers on the proper DNS record. Which of the following protocols should the company apply next?
A vendor needs to remotely and securely transfer files from one server to another using the command line. Which of the following protocols should be Implemented to allow for this type of access? (Select two).
Which of the following methods will most likely be used to identify legacy systems?
An administrator discovers that some files on a database server were recently encrypted. The administrator sees from the security logs that the data was last accessed by a domain user. Which of the following best describes the type of attack that occurred?
Which of the following control types involves restricting IP connectivity to a router ' s web management interface to protect it from being exploited by a vulnerability?
A security officer observes that a software development team is not complying with its corporate security policy on encrypting confidential data. Which of the following categories refers to this type of non-compliance?
An IT administrator needs to ensure data retention standards are implemented on an enterprise application. Which of the following describes the administrator ' s role?
Which of the following most accurately describes the order in which a security engineer should implement secure baselines?
A user sends an email that includes a digital signature for validation. Which of the following security concepts would ensure that a user cannot deny that they sent the email?
A company requires hard drives to be securely wiped before sending decommissioned systems to recycling. Which of the following best describes this policy?
A network engineer is increasing the overall security of network devices and needs to harden the devices. Which of the following will best accomplish this task?
A penetration test identifies that an SMBvl Is enabled on multiple servers across an organization. The organization wants to remediate this vulnerability in the most efficient way possible. Which of the following should the organization use for this purpose?
A company processes and stores sensitive data on its own systems. Which of the following steps should the company take first to ensure compliance with privacy regulations?
Which of the following is the greatest advantage that network segmentation provides?
An administrator is installing an SSL certificate on a new system. During testing, errors indicate that the certificate is not trusted. The administrator has verified with the issuing CA and has validated the private key. Which of the following should the administrator check for next?
A company installed cameras and added signs to alert visitors that they are being recorded. Which of the following controls did the company implement? (Select two).
A security operations center determines that the malicious activity detected on a server is normal. Which of the following activities describes the act of ignoring detected activity in the future?
Which of the following is the best way to validate the integrity and availability of a disaster recovery site?
Which of the following is most likely associated with introducing vulnerabilities on a corporate network by the deployment of unapproved software?
Cadets speaking a foreign language are using company phone numbers to make unsolicited phone calls lo a partner organization. A security analyst validates through phone system logs that the calls are occurring and the numbers are not being spoofed. Which of the following is the most likely explanation?
A few weeks after deploying additional email servers, a company begins to receive complaints that messages are going into recipients’ spam folders. Which of the following needs to be updated?
An organization wants to limit potential impact to its log-in database in the event of a breach. Which of the following options is the security team most likely to recommend?
Which of the following cryptographic methods is preferred for securing communications with limited computing resources?
Which of the following threat actors is the most likely to be hired by a foreign government to attack critical systems located in other countries?
Which of the following is a feature of a next-generation SIEM system?
An MSSP manages firewalls for hundreds of clients. Which of the following tools would be most helpful to create a standard configuration template in order to improve the efficiency of firewall changes?
Several employees received a fraudulent text message from someone claiming to be the Chief Executive Officer (CEO). The message stated:
“I’m in an airport right now with no access to email. I need you to buy gift cards for employee recognition awards. Please send the gift cards to following email address.”
Which of the following are the best responses to this situation? (Choose two).
Which of the following should a technician perform to verify the integrity of a file transferred from one device to another?
Which of the following is a possible consequence of a VM escape?
A company wants to track modifications to the code that is used to build new virtual servers. Which of the following will the company most likely deploy?
A company prevented direct access from the database administrators’ workstations to the network segment that contains database servers. Which of the following should a database administrator use to access the database servers?
Which of the following actions best addresses a vulnerability found on a company ' s web server?
During a recent log review, an analyst discovers evidence of successful injection attacks. Which of the following will best address this issue?
A staff member finds a USB drive in the office ' s parking lot. Which of the following should the staff member do?
A software developer released a new application and is distributing application files via the developer’s website. Which of the following should the developer post on the website to allow users to verify the integrity of the downloaded files?
A security administrator needs to reduce the attack surface in the company ' s data centers. Which of the following should the security administrator do to complete this task?
An attacker submits a request containing unexpected characters in an attempt to gain unauthorized access to information within the underlying systems. Which of the following best describes this attack?
A security engineer configured a remote access VPN. The remote access VPN allows end users to connect to the network by using an agent that is installed on the endpoint, which establishes an encrypted tunnel. Which of the following protocols did the engineer most likely implement?
Alerts from email protection systems and MSSPs must be entered into an IT service management system and assigned to the security team. Which of the following should an organization implement to enable this functionality?
Which of the following risk management strategies should an enterprise adopt first if a legacy application is critical to business operations and there are preventative controls that are not yet implemented?
A security analyst receives alerts about an internal system sending a large amount of unusual DNS queries to systems on the internet over short periods of time during non-business hours. Which of the following is most likely occurring?
While reviewing logs, a security administrator identifies the following code:
< script > function(send_info) < /script >
Which of the following best describes the vulnerability being exploited?
Which of the following types of identification methods can be performed on a deployed application during runtime?
A security administrator wants to determine if the company ' s social engineering training is effective. Which of the following should the administrator do to complete this task?
An administrator wants to perform a risk assessment without using proprietary company information. Which of the following methods should the administrator use to gather information?
Which vulnerability is most likely mitigated by setting up an MDM platform?
During a SQL update of a database, a temporary field that was created was replaced by an attacker in order to allow access to the system. Which of the following best describes this type of vulnerability?
A growing company would like to enhance the ability of its security operations center to detect threats but reduce the amount of manual work required tor the security analysts. Which of the following would best enable the reduction in manual work?
Which of the following security concepts is being followed when implementing a product that offers protection against DDoS attacks?
A newly identified network access vulnerability has been found in the OS of legacy loT devices. Which of the following would best mitigate this vulnerability quickly?
An organization wants to donate its aging network hardware. Which of the following should the organization perform to prevent any network details from leaking?
A company is in the process of cutting jobs to manage costs. The Chief Information Security Officer is concerned about the increased risk of an insider threat. Which of the following would most likely help the security awareness team address this potential threat?
Which of the following provides the best protection against unwanted or insecure communications to and from a device?
Which of the following can automate vulnerability management?
Which of the following must be considered when designing a high-availability network? (Select two).
Malware spread across a company ' s network after an employee visited a compromised industry blog. Which of the following best describes this type of attack?
While a user reviews their email, a host gets infected by malware from an external hard drive plugged into the host. The malware steals all the user ' s credentials stored in the browser. Which of the following training topics should the user review to prevent this situation from reoccurring?
A security analyst is reviewing the following logs:
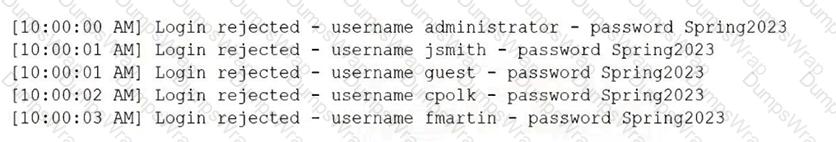
Which of the following attacks is most likely occurring?
A security manager created new documentation to use in response to various types of security incidents. Which of the following is the next step the manager should take?
Which of the following best describe why a process would require a two-person integrity security control?
An enterprise is trying to limit outbound DNS traffic originating from its internal network. Outbound DNS requests will only be allowed from one device with the IP address 10.50.10.25. Which of the following firewall ACLs will accomplish this goal?
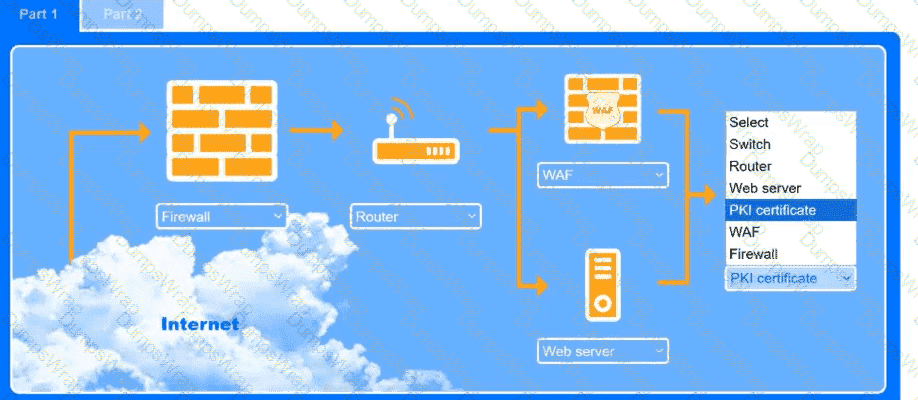
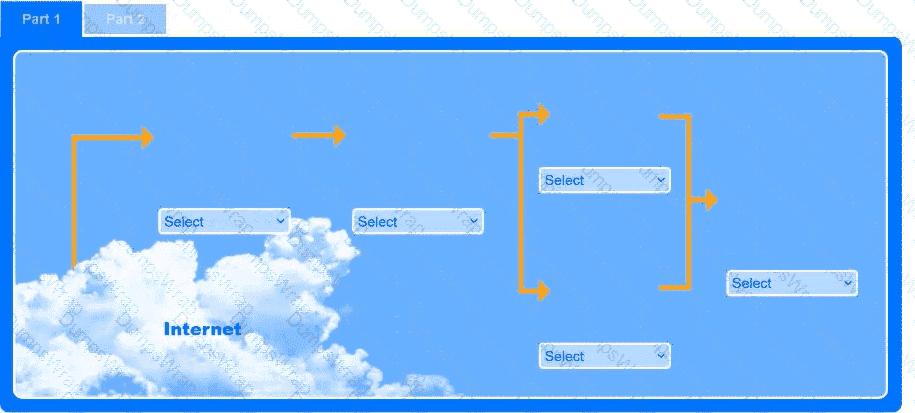
A recent black-box penetration test of discovered that external
website vulnerabilities exist, such as directory traversals, cross-site scripting, cross-site forgery, and insecure protocols.
You are tasked with reducing the attack space and enabling secure protocols.
INSTRUCTIONS
Part 1
Use the drop-down menus to select the appropriate technologies for each location to implement a secure and resilient web architecture. Not all technologies will be used, and technologies may be used multiple times.
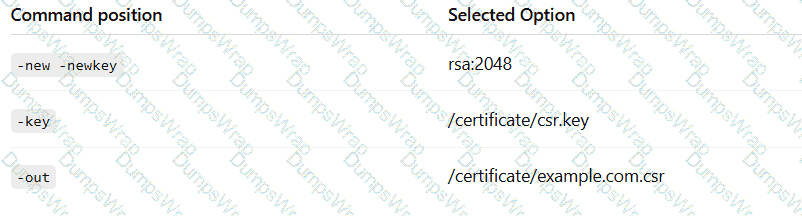
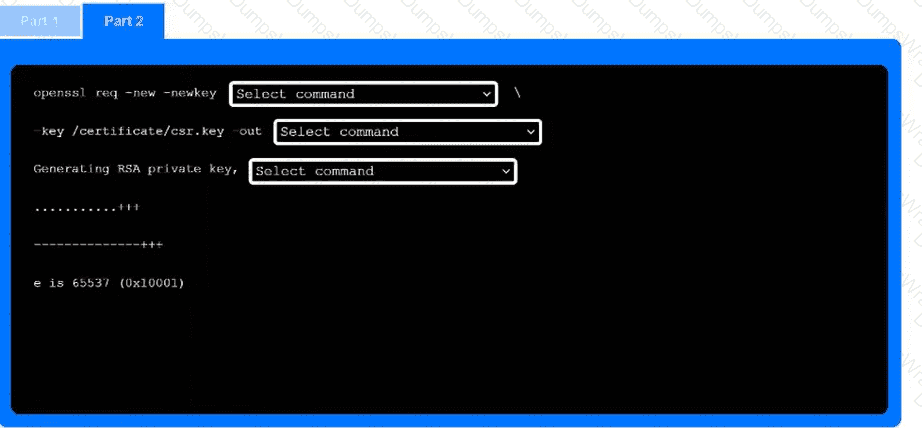
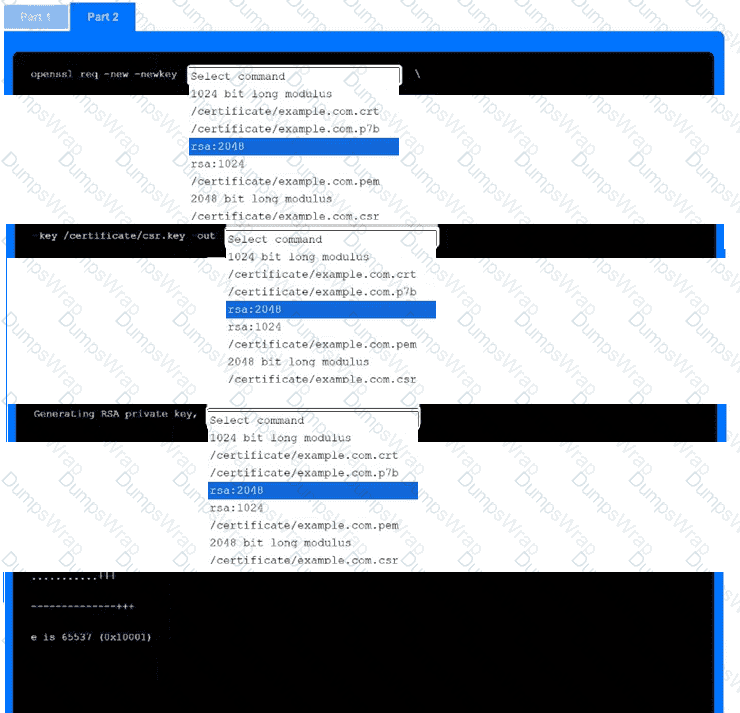
Part 2
Use the drop-down menus to select the appropriate command snippets from the drop-down menus. Each command section must be filled.

A security analyst must select a metric to determine the required investment in technology based on past availability incidents. Which of the following is the most relevant value to help select technology that mitigates risk and considers reliability?
Which of the following is an example of a false negative vulnerability detection in a scan report?
A company relies on open-source software libraries to build the software used by its customers. Which of the following vulnerability types would be the most difficult to remediate due to the company ' s reliance on open-source libraries?
A security engineer at a large company needs to enhance IAM to ensure that employees can only access corporate systems during their shifts. Which of the following access controls should the security engineer implement?
After a recent ransomware attack on a company ' s system, an administrator reviewed the log files. Which of the following control types did the administrator use?
A healthcare organization wants to provide a web application that allows individuals to digitally report health emergencies.
Which of the following is the most important consideration during development?
A new employee logs in to the email system for the first time and notices a message from human resources about onboarding. The employee hovers over a few of the links within the email and discovers that the links do not correspond to links associated with the company. Which of the following attack vectors is most likely being used?
A client asked a security company to provide a document outlining the project, the cost, and the completion time frame. Which of the following documents should the company provide to the client?
A security analyst and the management team are reviewing the organizational performance of a recent phishing campaign. The user click-through rate exceeded the acceptable risk threshold, and the management team wants to reduce the impact when a user clicks on a link in a phishing message. Which of the following should the analyst do?
A security administrator is deploying a DLP solution to prevent the exfiltration of sensitive customer data. Which of the following should the administrator do first?
An organization is struggling with scaling issues on its VPN concentrator and internet circuit due to remote work. The organization is looking for a software solution that will allow it to reduce traffic on the VPN and internet circuit, while still providing encrypted tunnel access to the data center and monitoring of remote employee internet traffic. Which of the following will help achieve these objectives?
Which of the following would enable a data center to remain operational through a multiday power outage?
Which of the following is used to add extra complexity before using a one-way data transformation algorithm?
An employee from the accounting department logs in to the website used for processing the company ' s payments. After logging in, a new desktop application automatically downloads on the employee ' s computer and causes the computer to restart. Which of the following attacks has occurred?
After a security incident, a systems administrator asks the company to buy a NAC platform. Which of the following attack surfaces is the systems administrator trying to protect?
A company plans to secure its systems by:
Preventing users from sending sensitive data over corporate email
Restricting access to potentially harmful websites
Which of the following features should the company set up? (Select two).
A security analyst is investigating an alert that was produced by endpoint protection software. The analyst determines this event was a false positive triggered by an employee who attempted to download a file. Which of the following is the most likely reason the download was blocked?
A company is redesigning its infrastructure and wants to reduce the number of physical servers in use. Which of the following architectures is best suited for this goal?
A security analyst finds a rogue device during a monthly audit of current endpoint assets that are connected to the network. The corporate network utilizes 002.1X for access control. To be allowed on the network, a device must have a Known hardware address, and a valid user name and password must be entered in a captive portal. The following is the audit report:
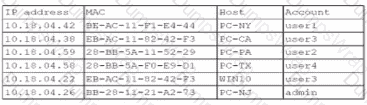
Which of the following is the most likely way a rogue device was allowed to connect?
A systems administrator needs to provide traveling employees with a tool that will protect company devices regardless of where they are working. Which of the following should the administrator implement?
Which of the following technologies assists in passively verifying the expired status of a digital certificate?
After completing an annual external penetration test, a company receives the following guidance:
Decommission two unused web servers currently exposed to the internet.
Close 18 open and unused ports found on their existing production web servers.
Remove company email addresses and contact info from public domain registration records.
Which of the following does this represent?
In which of the following scenarios is tokenization the best privacy technique 10 use?
Which of the following explains why an attacker cannot easily decrypt passwords using a rainbow table attack?
A security analyst receives an alert from a web server that contains the following logs:
GET /image?filename=../../../etc/passwd
Host: AcmeInc.web.net
useragent: python-request/2.27.1
GET /image?filename=../../../etc/shadow
Host: AcmeInc.web.net
useragent: python-request/2.27.1
Which of the following attacks is being attempted?
Which of the following is a common data removal option for companies that want to wipe sensitive data from hard drives in a repeatable manner but allow the hard drives to be reused?
A small business initially plans to open common communications ports (21, 22, 25, 80, 443) on its firewall to allow broad access to its screened subnet. However, their security consultant advises against this action. Which of the following security principles is the consultant addressing?
A systems administrator uses deception techniques to help detect and study attacks within a network. The administrator deploys a document filled with fake passwords and customer payment information. Which of the following techniques is the administrator using?
Which of the following should a security administrator adhere to when setting up a new set of firewall rules?
While troubleshooting a firewall configuration, a technician determines that a “deny any” policy should be added to the bottom of the ACL. The technician updates the policy, but the new policy causes several company servers to become unreachable.
Which of the following actions would prevent this issue?
Which of the following has been implemented when a host-based firewall on a legacy Linux system allows connections from only specific internal IP addresses?
Which of the following are the best security controls for controlling on-premises access? (Select two.)
An employee who was working remotely lost a mobile device containing company data. Which of the following provides the best solution to prevent future data loss?
Which of the following actions must an organization take to comply with a person ' s request for the right to be forgotten?
A cybersecurity incident response team at a large company receives notification that malware is present on several corporate desktops No known Indicators of compromise have been found on the network. Which of the following should the team do first to secure the environment?
Which of the following is a qualitative approach to risk analysis?

 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.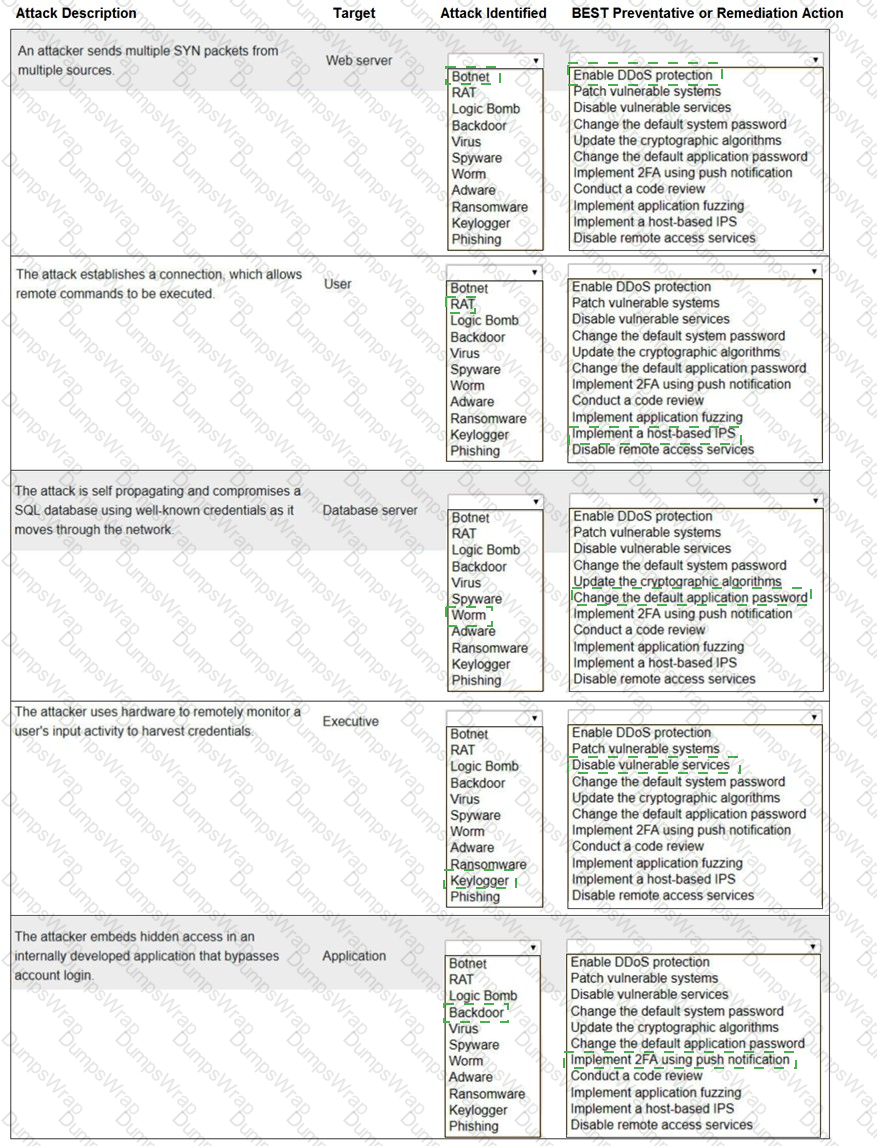
 A screenshot of a computer program Description automatically generated with low confidence
A screenshot of a computer program Description automatically generated with low confidence