FCSS Advanced Analytics 6.7 Architect Questions and Answers
What happens to events that the collector receives when there is a WAN link failure between the collector and the supervisor?
What are two functions of numpoints in a rule and profile database? (Choose two.)
Refer to the exhibit.
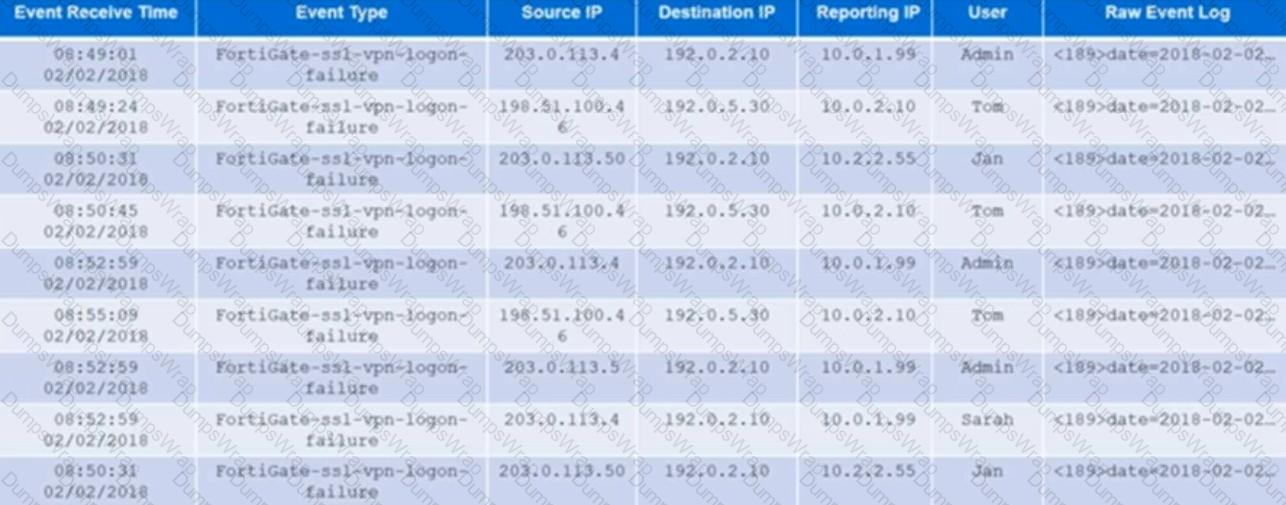
An administrator runs an analytic search for all FortiGate SSL VPN logon failures. The results are grouped by source IP, reporting IP, and user. The administrator wants to restrict the results to only those rows where the COUNT >=3.
Which user would meet that condition?
How can you invoke an integration policy on FortiSIEM rules?
What are the modes of Data Ingestion on FortiSOAR? (Choose three.)
Refer to the exhibit.

The exhibit shows the output of an SQL command that an administrator ran to view the natural_id value, after logging into the Postgres database.
What does the natural_id value identify?
Which statement accurately contrasts lookup tables with watchlists?
Refer to the exhibit.
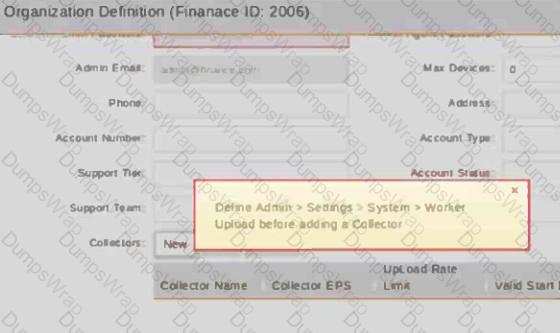
A service provider does not have a dedicated worker in the cluster, but still wants to add a collector to an organization.
What option does the administrator have?
Refer to the exhibit.
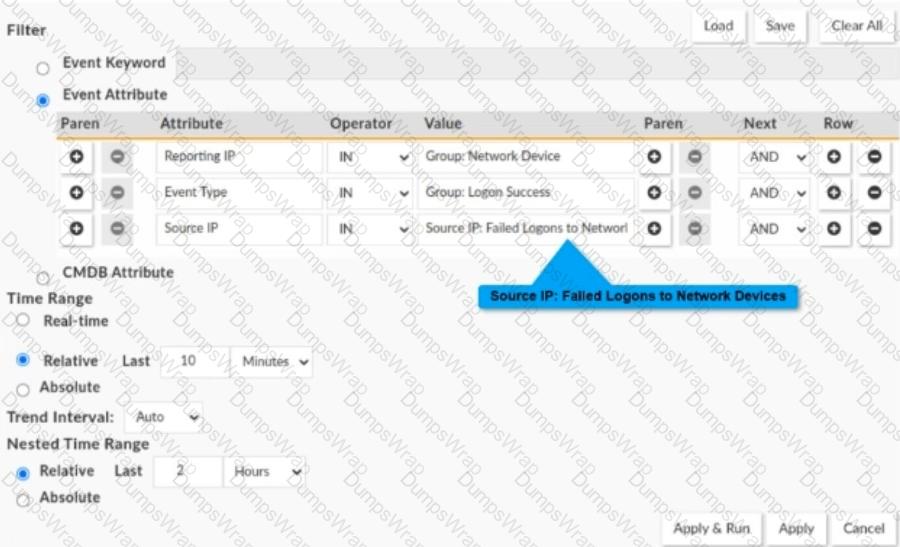
Consider a nested event query where both inner and outer queries are event queries.
Reporting IPis selected from the CMDB groupNetwork Device, Event Typeis selected from the CMDB groupLogon Success,andSource IPis selected from the reportFailed Logons to Network Devices.
An administrator is about to execute the nested query. The report time ranges must be set before execution. TheNested Time Rangewill be applied to which attributes?
Refer to the exhibit.
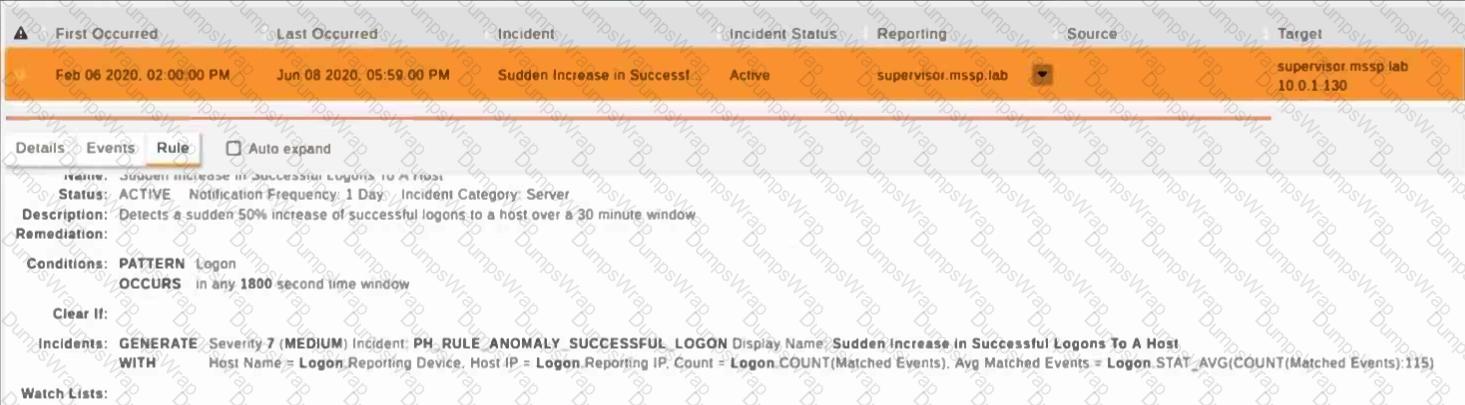
Within what time window is the incident auto cleared?
Refer to the exhibit.
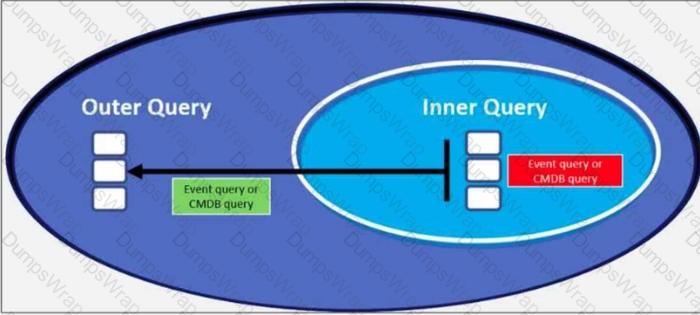
Which scenario is not a supported nested query scenario?
Which three statements about collector communication with the FortiSIEM cluster are true? (Choose three.)
What is the hourly bucket used in baselining?
Refer to the exhibit.

This is an example of a baseline profile that is configured in the backend of FortiSIEM.
Which two Group By attributes are configured for this profile? (Choose two.)
A service provider purchases a licensed EPS of 520. The guaranteed EPS allocated to three customers is 50, 100, and 150 respectively. At the end of every three-minute interval, incoming EPS is calculated at every collector and the value is sent to the central decision-making engine on the supervisor node.
The incoming EPS for the first collector is 25. the incoming EPS for the second collector is 50, and the incoming EPS for the third collector is 75.
Based on the information provided, what is the unused events total calculated by the supervisor?
How can you empower SOC by deploying FortiSOAR? (Choose three.)
Refer to the exhibit.
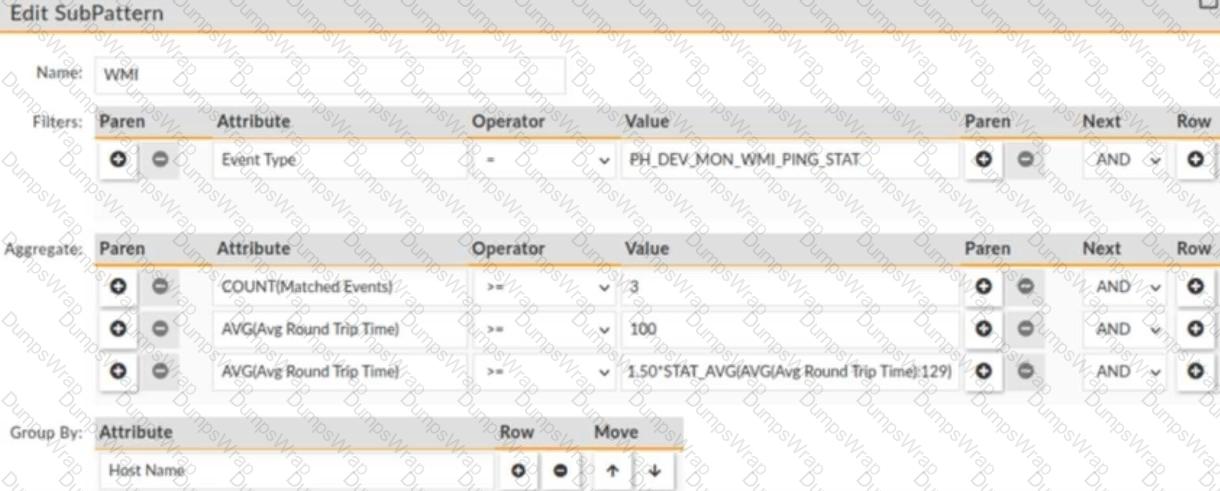
The window for this rule is 30 minutes.
What is this rule tracking?

 numPoints ensures that a rule does not trigger until a sufficient number of data points are collectedfor the baseline.
numPoints ensures that a rule does not trigger until a sufficient number of data points are collectedfor the baseline. Without enough data, the system may generatefalse positivesdue to the lack of a stable historical pattern.
Without enough data, the system may generatefalse positivesdue to the lack of a stable historical pattern. When querying theprofile database, numPoints acts as afilterto ensure that onlydata points meeting a minimum thresholdare considered for analysis.
When querying theprofile database, numPoints acts as afilterto ensure that onlydata points meeting a minimum thresholdare considered for analysis. This prevents unreliable or insufficient historical data from affecting anomaly detection.
This prevents unreliable or insufficient historical data from affecting anomaly detection. FortiSOAR ingests data when specific rules are triggered based on defined conditions.
FortiSOAR ingests data when specific rules are triggered based on defined conditions. This enables automation and intelligence-driven event ingestion.
This enables automation and intelligence-driven event ingestion. External applications canpushdata into FortiSOAR usingAPIs and integrations.
External applications canpushdata into FortiSOAR usingAPIs and integrations. This is useful forreal-time ingestionfrom external tools like SIEMs, ticketing systems, and threat intelligence platforms.
This is useful forreal-time ingestionfrom external tools like SIEMs, ticketing systems, and threat intelligence platforms. Data is ingested based onpredefined schedules.
Data is ingested based onpredefined schedules. This is useful for periodic polling of external systems, fetching logs, and running automated tasks at set intervals.
This is useful for periodic polling of external systems, fetching logs, and running automated tasks at set intervals.