FCSS - Enterprise Firewall 7.4 Administrator Questions and Answers
An administrator is extensively using VXLAN on FortiGate.
Which specialized acceleration hardware does FortiGate need to improve its performance?
Refer to the exhibit, which shows an ADVPN network
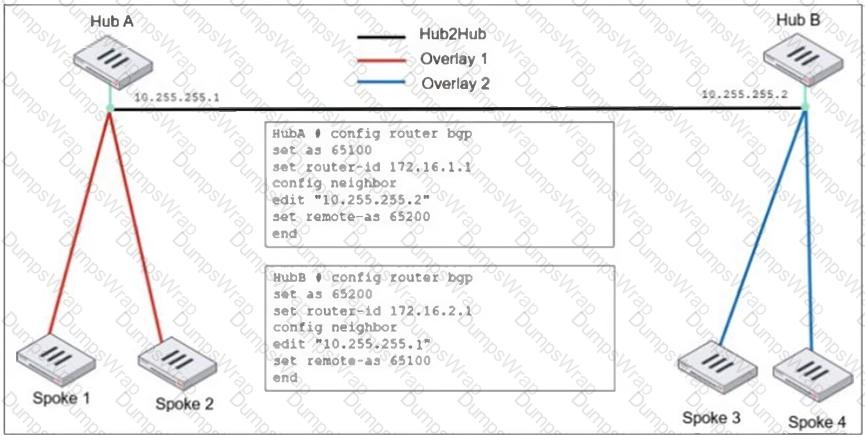
An administrator must configure an ADVPN using IBGP and EBGP to connect overlay network 1 with 2.
What two options must the administrator configure in BGP? (Choose two.)
A vulnerability scan report has revealed that a user has generated traffic to the website example.com (10.10.10.10) using a weak SSL/TLS version supported by the HTTPS web server.
What can the firewall administrator do to block all outdated SSL/TLS versions on any HTTPS web server to prevent possible attacks on user traffic?
Refer to the exhibit, which shows theADVPNIPsec interface representing the VPN IPsec phase 1 from Hub A to Spoke 1 and Spoke 2, and from Hub В to Spoke 3 and Spoke 4.
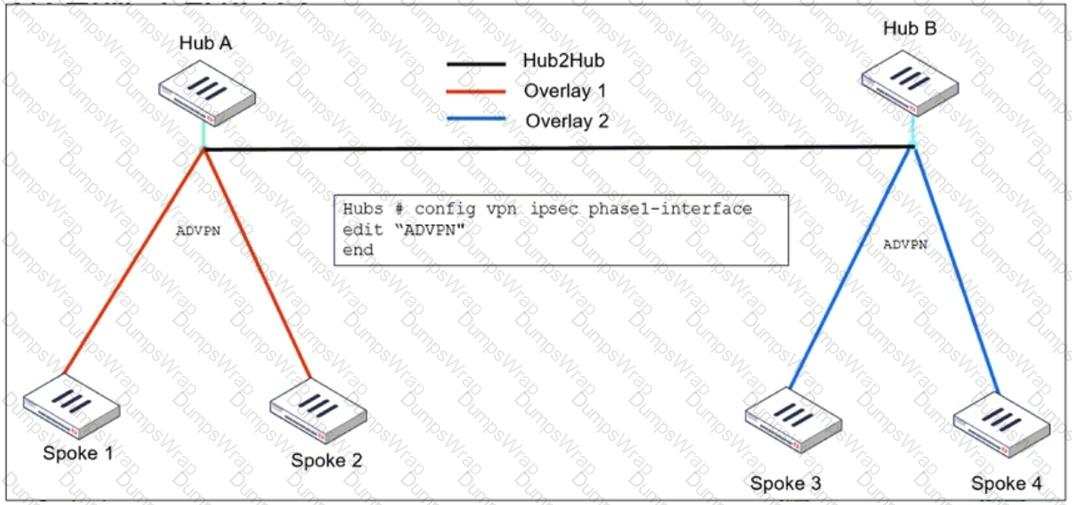
An administrator must configure an ADVPN using IBGP and EBGP to connect overlay network 1 with 2.
What must the administrator configure in the phase 1 VPN IPsec configuration of theADVPNtunnels?
Refer to the exhibit, which shows a network diagram showing the addition of site 2 with an overlapping network segment to the existing VPN IPsec connection between the hub and site 1.
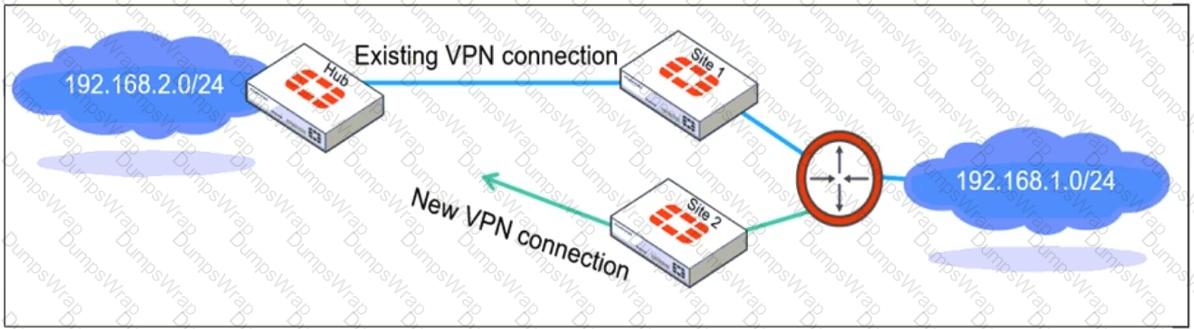
Which IPsec phase 2 configuration must an administrator make on the FortiGate hub to enable equal-cost multi-path (ECMP) routing when multiple remote sites connect with overlapping subnets?
An administrator is setting up an ADVPN configuration and wants to ensure that peer IDs are not exposed during VPN establishment.
Which protocol can the administrator use to enhance security?
Refer to the exhibit.
A pre-run CLI template that is used in zero-touch provisioning (ZTP) and low-touch provisioning (LTP) with FortiManager is shown.
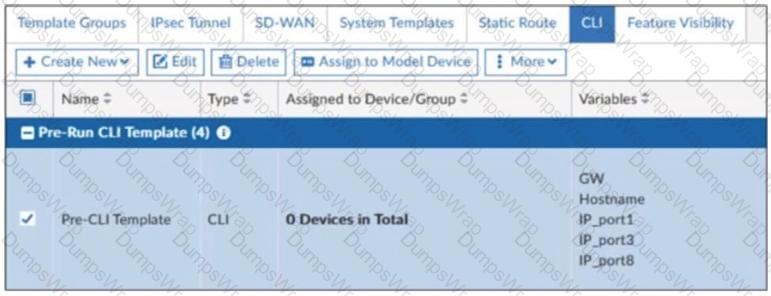
The template is not assigned even though the configuration has already been installed on FortiGate.
What is true about this scenario?
How will configuring set tcp-mss-sender and set tcp-mss-receiver in a firewall policy affect the size and handling of TCP packets in the network?
Which two statements about IKEv2 are true if an administrator decides to implement IKEv2 in the VPN topology? (Choose two.)
Why does the ISDB block layers 3 and 4 of the OSI model when applying content filtering? (Choose two.)
Refer to the exhibit, which contains the partial output of an OSPF command.
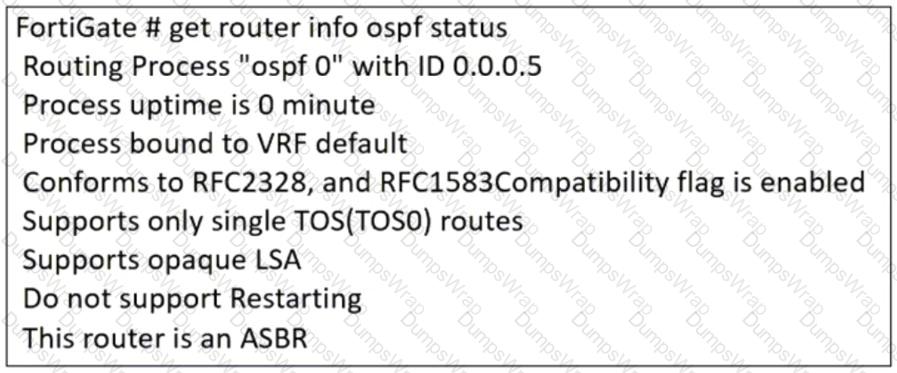
An administrator is checking the OSPF status of a FortiGate device and receives the output shown in the exhibit.
Which statement on this FortiGate device is correct?
Refer to the exhibit, which shows an enterprise network connected to an internet service provider.
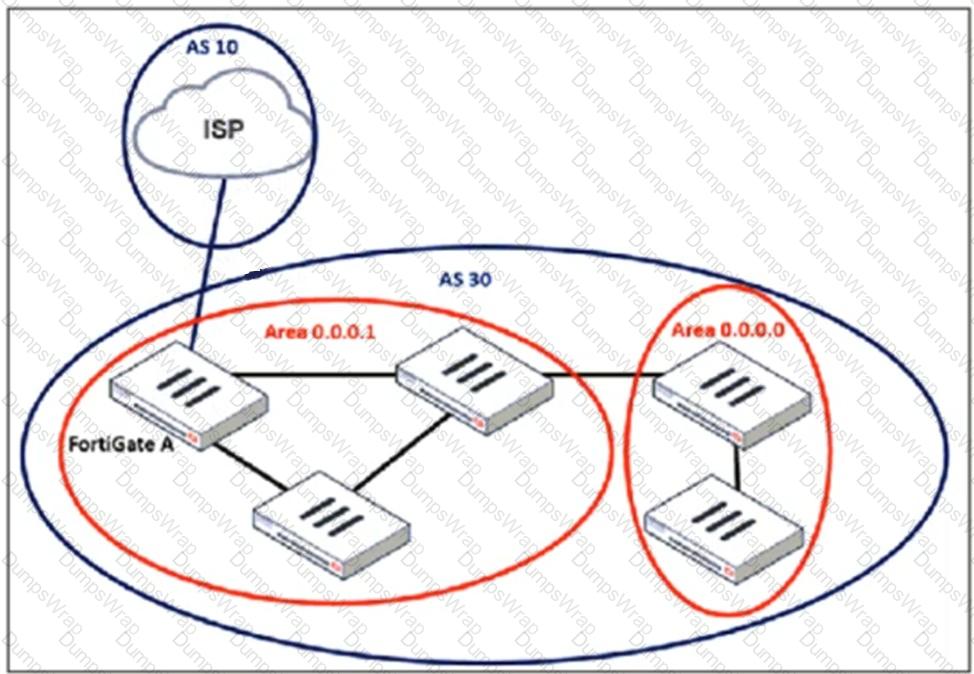
An administrator must configure a loopback as a BGP source to connect to the ISP.
Which two commands are required to establish the connection? (Choose two.)
Refer to the exhibit, which shows a network diagram.
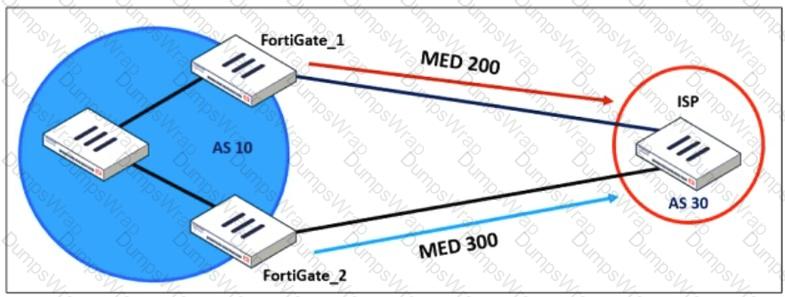
An administrator would like to modify the MED value advertised from FortiGate_1 to a BGP neighbor in the autonomous system 30.
What must the administrator configure on FortiGate_1 to implement this?
A FortiGate device with UTM profiles is reaching the resource limits, and the administrator expects the traffic in the enterprise network to increase.
The administrator has received an additional FortiGate of the same model.
Which two protocols should the administrator use to integrate the additional FortiGate device into this enterprise network? (Choose two.)
An administrator is checking an enterprise network and sees a suspicious packet with the MAC address e0:23:ff:fc:00:86.
What two conclusions can the administrator draw? (Choose two.)
Refer to the exhibits.
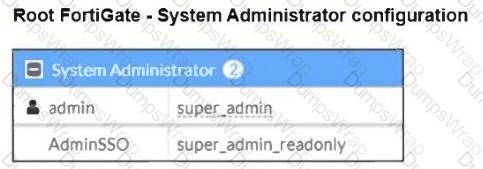
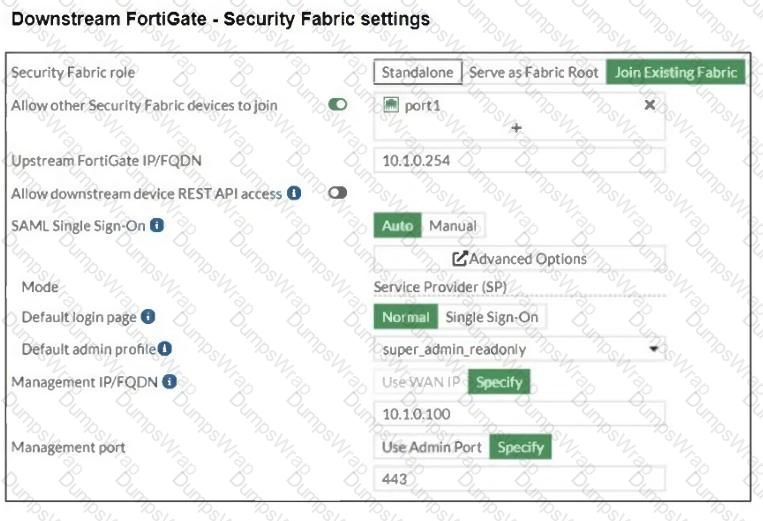
The Administrators section of a root FortiGate device and the Security Fabric Settings section of a downstream FortiGate device are shown.
When prompted to sign in with Security Fabric in the downstream FortiGate device, a user enters the AdminSSO credentials.
What is the next status for the user?
An administrator must minimize CPU and RAM use on a FortiGate firewall while also enabling essential security features, such as web filtering and application control for HTTPS traffic.
Which SSL inspection setting helps reduce system load while also enabling security features, such as web filtering and application control for encrypted HTTPS traffic?

 BGP normally expects directly connected neighbors, but since the ISP and FortiGate A are usingloopback interfaces,packets will not be sent directly between their physical interfaces.
BGP normally expects directly connected neighbors, but since the ISP and FortiGate A are usingloopback interfaces,packets will not be sent directly between their physical interfaces. Theebgp-enforce-multihopcommandallows BGP to form an eBGP peering over multiple hops.
Theebgp-enforce-multihopcommandallows BGP to form an eBGP peering over multiple hops. Since FortiGate is using aloopback interface as the source, theupdate-sourcecommand ensures thatBGP updates originate from the loopback interfacerather than a physical interface.
Since FortiGate is using aloopback interface as the source, theupdate-sourcecommand ensures thatBGP updates originate from the loopback interfacerather than a physical interface. This is essential becauseBGP peers must match the source IP with the configured neighbor address.
This is essential becauseBGP peers must match the source IP with the configured neighbor address. FGSP allowssession-aware load balancingbetween multiple FortiGate units without requiring them to be in an HA (High Availability) cluster.
FGSP allowssession-aware load balancingbetween multiple FortiGate units without requiring them to be in an HA (High Availability) cluster. Withexternal load balancers, incoming traffic isevenly distributedacross multiple FortiGate devices.
Withexternal load balancers, incoming traffic isevenly distributedacross multiple FortiGate devices. This approach is useful forscaling outtraffic handling capacity while ensuring that sessions remainsynchronizedbetween firewalls.
This approach is useful forscaling outtraffic handling capacity while ensuring that sessions remainsynchronizedbetween firewalls. FGSP is effectivewhen stateful failover is requiredbut without the constraints of traditional HA.
FGSP is effectivewhen stateful failover is requiredbut without the constraints of traditional HA. FGCPactive-active modeenables multiple FortiGate devices toshare traffic loads, increasing throughput and efficiency.
FGCPactive-active modeenables multiple FortiGate devices toshare traffic loads, increasing throughput and efficiency. Active-active mode is suitable forbalancing UTM processingacross multiple FortiGates, making it ideal whenresource limits are a concern.
Active-active mode is suitable forbalancing UTM processingacross multiple FortiGates, making it ideal whenresource limits are a concern. Usingswitchesensures redundancy and avoids single points of failure in the network.
Usingswitchesensures redundancy and avoids single points of failure in the network. This mode is commonly used inenterprise networkswhere bothscalability and redundancyare required.
This mode is commonly used inenterprise networkswhere bothscalability and redundancyare required.