HCIA-Security V4.0 Exam Questions and Answers
Which of the following statements is incorrect about information transmission through the heartbeat link between two firewalls that work in hot standby mode?
Which of the following types of packets cannot be filtered by a packet filtering firewall?
SSL VPN is a VPN technology that realizes remote secure access through SSL protocol. Which of the following software must be installed when using SSL VPN?
Which of the following statements are correct about SYN flood attack defense technologies on Huawei firewalls?
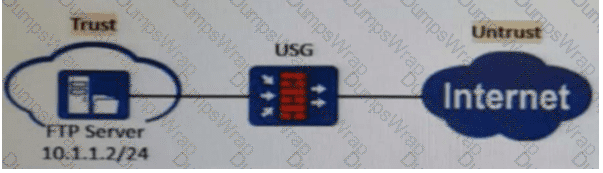
As shown in the figure, nat server global202.106.1.1 inside10.10.1.1 is configured on the firewall. Which of the following is the correct configuration for interzone rules?
Which of the following statements is incorrect about L2TP?
Which of the following attack methods is to construct special SQL statements and submit sensitive information to exploit program vulnerabilities
Which of the following problems cannot be solved using PKI?
When IKEv1 negotiation phase 1 uses the aggressive mode, only three messages are used. Which of the following is the function of message 3?
Which of the following is not an encryption algorithm in a VPN?
Which of the following types of malicious code on your computer includes?
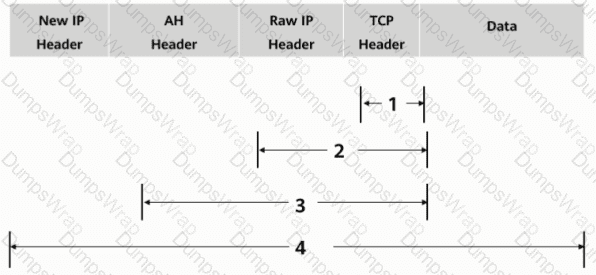
As shown in the figure, what is the authentication range of the AH protocol in tunnel mode?
Which of the following statements are incorrect about the differences between routers and Layer 2 switches?
A three-way handshake is required to establish a TCP connection, and a four-way handshake is required to end a TCP connection.
The RADIUS protocol specifies how to pass user information, billing information, authentication and billing results between the NAS and the RADIUS server, and the RADIUS server is responsible for receiving the user's connection request, completing the authentication, and returning the result to the NAS.
As shown in the figure, the administrator needs to test the network quality of the 20.0.0/24 CIDR block to the 40.0.0/24 CIDR block on Device B, and the device needs to send large packets for a long time to test the network connectivity and stability.

Which of the following packets is controlled by a firewall's security policy by default?
Which of the following protocols are transport layer protocols?
Which of the following is not included in the Business Impact Analysis (BIA).
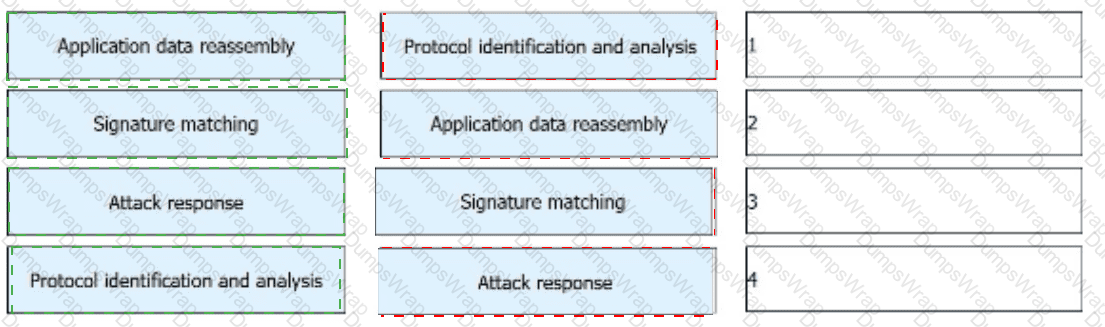
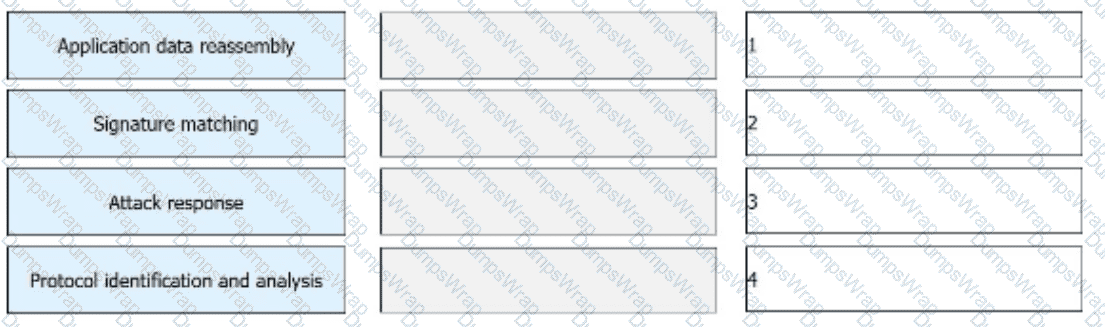
The IPS detects and analyzes all packets passing through a device and determines whether to permit or block the packets in real time based on the comprehensive detection mechanism. Sort the following steps into the correct order based on the basic implementation mechanism of the IPS.
During the process of establishing IPSec VPN between peers FW_A and FW_B, two types of security associations need to be established in two stages. In the first stage, _____ is established to verify the identity of the peers.[fill in the blank]*
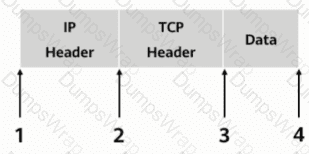
As shown, in transmission mode, which of the following locations should the AH header be inserted in?
The keys used by the IPSec encryption and authentication algorithms can be configured manually or dynamically negotiated via the ____ protocol. (abbreviation, all uppercase).
The following description of digital certificates, which one is wrong
Which of the following is not an application scenario for PKI?
Which of the following characteristics does a denial-of-service attack include?
In cases where some configurations alter existing session table entries and want them to take effect immediately, you can regenerate the session table by clearing the session table information. All session table information can be cleared by executing the _____firewall session table command.
Which security zone can be deleted and its priority can be reconfigured?
Sub-interfaces can be created on GE0/0/1 of a firewall. The sub-interfaces can be added to different VLANs, but cannot be added to security zones.
According to the level protection requirements, which of the following behaviors belong to the scope of information security operation and maintenance management? ( )*
Which of the following statements is correct about SSO?
Which of the following is not an advantage of symmetric encryption algorithms?
Which layer of the protocol stack does SSL provide end-to-end encrypted transmission services?
WAF can accurately control and manage users' online behavior and user traffic.
When the Layer 2 switch receives a unicast frame and the MAC address table entry of the switch is empty, the switch discards the unicast frame.
IPSec VPN uses an asymmetric algorithm to calculate the ___ key to encrypt data packets.[fill in the blank]
A VRRP group has three states: Initialize, Master, and Backup.
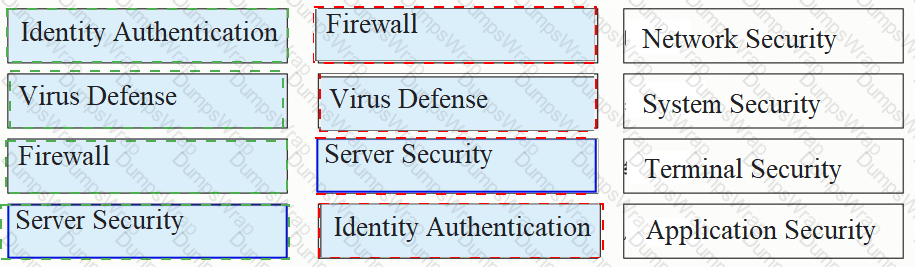
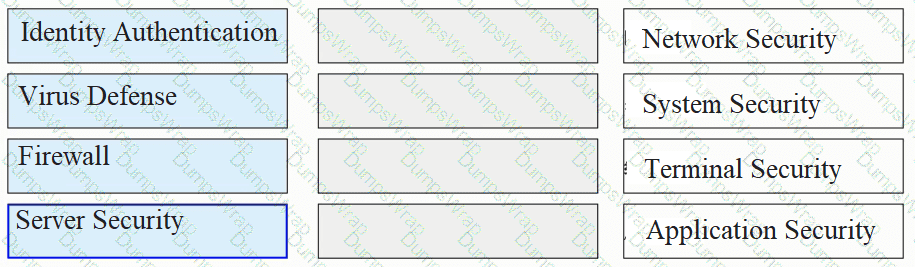
Please classify the following security defenses into the correct classification.
Social engineering is a means of harm such as deception, harm, etc. through psychological traps such as psychological weaknesses, instinctive reactions, curiosity, trust, and greed of victims ( )
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.
Compared with the software architecture of C/S, B/S does not need to install a browser, and users are more flexible and convenient to use.
An engineer needs to back up the firewall configuration. Now he wants to use a command to view all the current configurations of the firewall. May I ask the command he uses is ____[fill in the blank]*
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
In the authentication policy of the firewall, _____ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
A Web server is deployed in an enterprise intranet to provide Web access services to Internet users, and in order to protect the access security of the server, it should be divided into the _____ area of the firewall.