Business Knowledge for Internal Auditing Questions and Answers
An internal auditor is reviewing results from software development integration testing. What is the purpose of integration testing?
Options:
To verify that the application meets stated user requirements.
To verify that standalone programs match code specifications.
To verify that the application would work appropriately for the intended number of users.
To verify that all software and hardware components work together as intended.
Answer:
DExplanation:
Integration testing is a phase in the software development lifecycle (SDLC) where individual components or systems are combined and tested as a group to ensure they work together correctly.
Ensures Component Compatibility – Confirms that different software modules and hardware components function correctly when integrated.
Identifies Data Flow Issues – Ensures seamless communication between software systems, databases, and external applications.
Detects System-Wide Errors – Finds defects that unit testing (individual module testing) may miss.
Prepares for System Testing – Integration testing is conducted before full system testing to ensure subsystems work together as expected.
A. To verify that the application meets stated user requirements.
This refers to User Acceptance Testing (UAT), not integration testing.
B. To verify that standalone programs match code specifications.
This describes unit testing, where individual components are tested separately.
C. To verify that the application would work appropriately for the intended number of users.
This describes performance or load testing, which measures system behavior under high user load.
IIA’s GTAG on IT Risks and Controls – Emphasizes the role of integration testing in ensuring secure and functional IT environments.
COBIT 2019 (Governance and Management of IT) – Recommends integration testing to reduce IT system failures.
ISO/IEC 25010 (Software Quality Model) – Lists integration testing as a key quality assurance step.
Why Option D is Correct?Why Not the Other Options?IIA References:
Which of the following best describes the purpose of fixed manufacturing costs?
Options:
To ensure availability of production facilities.
To decrease direct expenses related to production.
To incur stable costs despite operating capacity.
To increase the total unit cost under absorption costing
Answer:
AExplanation:
Fixed manufacturing costs refer to costs that do not vary with the level of production activity within a relevant range. These costs include expenses such as depreciation, rent, property taxes, and salaries of permanent employees in the production facility. Their primary purpose is to ensure the availability and operational readiness of production facilities, regardless of fluctuations in production levels.
(A) Correct – To ensure availability of production facilitiesFixed manufacturing costs are incurred to maintain and operate production facilities, ensuring that they remain functional and available for production when needed. These costs exist even if no units are produced, emphasizing their role in sustaining the production infrastructure.
(B) Incorrect – To decrease direct expenses related to productionFixed manufacturing costs are unrelated to direct expenses, such as raw materials and labor, which vary with production volume. Instead, they remain constant regardless of output levels.
(C) Incorrect – To incur stable costs despite operating capacityWhile fixed costs remain stable within a relevant range, their primary purpose is not just cost stability but ensuring production facilities' availability and functionality.
(D) Incorrect – To increase the total unit cost under absorption costingUnder absorption costing, fixed manufacturing costs are allocated to units produced, affecting per-unit cost calculations. However, this is an accounting treatment rather than the core purpose of fixed manufacturing costs.
IIA’s Global Internal Audit Standards – Managing Resources Effectively
Fixed manufacturing costs ensure operational resources are available and managed efficiently.
IIA’s Guide on Cost Management and Internal Control
Highlights the role of cost structures, including fixed costs, in ensuring business continuity.
IIA’s Practice Advisory on Cost Accounting Controls
Discusses the importance of maintaining production facilities to ensure operational readiness.
Breakdown of Answer Choices:IIA References and Internal Auditing Standards:Would you like further clarification on any point?
Which of the following describes a mechanistic organizational structure?
Options:
Primary direction of communication tends to be lateral.
Definition of assigned tasks tends to be broad and general.
Type of knowledge required tends to be broad and professional.
Reliance on self-control tends to be low.
Answer:
DExplanation:
A mechanistic organizational structure is a highly structured, hierarchical, and rigid system with well-defined roles, centralized authority, and formalized processes. It is best suited for stable environments where efficiency and control are priorities.
Highly centralized decision-making
Strict hierarchy and formalized job roles
Low flexibility and innovation
Heavy reliance on formal policies, procedures, and direct supervision
(A) Primary direction of communication tends to be lateral.
Incorrect: Mechanistic structures favor vertical communication (top-down or bottom-up), not lateral (horizontal) communication.
IIA Standard 2110 – Governance emphasizes clear roles and responsibilities, which are strictly followed in mechanistic structures.
(B) Definition of assigned tasks tends to be broad and general.
Incorrect: In a mechanistic structure, tasks are specific, well-defined, and specialized, unlike in an organic structure where roles are more flexible.
COSO ERM – Control Environment highlights well-defined roles in structured environments.
(C) Type of knowledge required tends to be broad and professional.
Incorrect: Mechanistic structures rely on specialized and technical knowledge, not broad, generalized knowledge.
(D) Reliance on self-control tends to be low. (Correct Answer)
Mechanistic structures depend on external control mechanisms like supervision, rules, and formal procedures.
Employees have little autonomy, and self-control is not a primary governance mechanism.
IIA Standard 2200 – Engagement Planning stresses the importance of structure in ensuring compliance, aligning with mechanistic principles.
IIA Standard 2110 – Governance: Defines structured governance mechanisms in hierarchical organizations.
COSO ERM – Control Environment: Emphasizes reliance on formal controls in rigid structures.
GTAG 1 – Information Technology Risks and Controls: Highlights the need for structured controls in mechanistic environments.
Characteristics of a Mechanistic Structure:Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (D) because mechanistic organizations rely heavily on external controls rather than self-regulation.
Which of the following is an established systems development methodology?
Options:
Waterfall.
Projects in Controlled Environments (PRINCE2).
Information Technology Infrastructure Library (ITIL).
COBIT
Answer:
AExplanation:
A systems development methodology refers to a structured approach used in software development and systems engineering to guide the design, development, and implementation of software applications.
Why Option A (Waterfall) is Correct:
Waterfall methodology is a linear and sequential systems development methodology where each phase (e.g., requirements, design, implementation, testing, deployment) must be completed before moving to the next.
It is widely established and historically one of the first software development methodologies.
Used in large-scale enterprise projects where detailed planning and structured execution are required.
Why Other Options Are Incorrect:
Option B (PRINCE2 - Projects in Controlled Environments):
Incorrect because PRINCE2 is a project management framework, not a systems development methodology.
Option C (ITIL - Information Technology Infrastructure Library):
Incorrect because ITIL is a set of IT service management (ITSM) best practices, not a software development methodology.
Option D (COBIT - Control Objectives for Information and Related Technologies):
Incorrect because COBIT is a governance framework for IT management and controls, not a development methodology.
IIA GTAG – "Auditing IT Projects and Systems Development": Highlights Waterfall as a traditional systems development methodology.
IIA’s Global Technology Audit Guide on IT Risks: Discusses software development lifecycle risks, including Waterfall methodology.
COBIT Framework – BAI03 (Manage Solutions Identification and Build): References structured methodologies like Waterfall in IT governance.
IIA References:
In light of increasing emission taxes in the European Union, a car manufacturer introduced a new middle-class hybrid vehicle specifically for the European market only. Which of the following competitive strategies has the manufacturer used?
Options:
Reactive strategy.
Cost leadership strategy.
Differentiation strategy.
Focus strategy
Answer:
DExplanation:
A focus strategy targets a specific market segment, geographical area, or niche customer base rather than competing in the entire market.
Why Option D (Focus strategy) is Correct:
The car manufacturer introduced a hybrid vehicle specifically for the European market to address increasing emission taxes, meaning they are focusing on a specific region and customer need.
Focus strategy aims at tailoring products to meet the needs of a particular group of consumers (e.g., environmentally conscious European customers).
Why Other Options Are Incorrect:
Option A (Reactive strategy):
Incorrect because while the company is responding to regulatory changes, "reactive strategy" is not a recognized competitive strategy under Porter’s model.
Option B (Cost leadership strategy):
Incorrect because cost leadership focuses on minimizing costs and offering the lowest price in the broad market. This scenario does not emphasize cost reduction.
Option C (Differentiation strategy):
Incorrect because differentiation involves offering unique products across a broad market, whereas the hybrid vehicle is targeted specifically for the European market.
IIA Practice Guide – "Auditing Strategic Risk Management": Discusses competitive strategies, including focus strategy.
Porter's Competitive Strategy Model: Defines focus strategy as targeting a niche market.
COSO ERM Framework – "Strategic Decision-Making": Recommends market-specific focus strategies to mitigate regulatory risks.
IIA References:
An organization's technician was granted a role that enables him to prioritize projects throughout the organization. Which type of authority will the technician most likely be exercising?
Options:
Legitimate authority
Coercive authority.
Referent authority.
Expert authority.
Answer:
DExplanation:
In organizations, authority types define how power and influence are exercised. Since the technician is prioritizing projects, their authority comes from their specialized knowledge or expertise, making this an example of expert authority.
Why Option D (Expert Authority) is Correct:
Expert authority is based on specialized knowledge, skills, or expertise rather than formal position or hierarchical power.
The technician is trusted to prioritize projects because of their technical knowledge and understanding of project impact.
Expert authority is commonly seen in IT specialists, consultants, and industry professionals who guide decision-making based on expertise.
Why Other Options Are Incorrect:
Option A (Legitimate Authority):
Incorrect because legitimate authority is derived from a formal position or title within an organizational hierarchy (e.g., CEO, manager).
Option B (Coercive Authority):
Incorrect because coercive authority relies on threats, punishment, or force, which is not applicable in this scenario.
Option C (Referent Authority):
Incorrect because referent authority is based on personal influence, charisma, or relationships, rather than expertise.
IIA Practice Guide – "Auditing Organizational Governance": Discusses different types of authority in decision-making.
COSO ERM Framework – "Risk Governance & Decision-Making": Recognizes expert authority as a key factor in risk-based project prioritization.
IIA’s GTAG – "Auditing IT Governance": Highlights the role of expert authority in IT project prioritization and governance.
IIA References:
Which of the following measures the operating success of a company for a given period of time?
Options:
Liquidity ratios.
Profitability ratios.
Solvency ratios.
Current ratios.
Answer:
BExplanation:
Profitability ratios measure a company's ability to generate profit over a specific period, making them the best indicators of operating success. These ratios assess financial performance by comparing income to various financial metrics such as revenue, assets, and equity.
Correct Answer (B - Profitability Ratios)
Profitability ratios reflect how effectively a company generates income from its operations over a given period.
Key profitability ratios include:
Gross Profit Margin: Measures how efficiently a company produces goods and services.
Operating Profit Margin: Shows profitability from core operations.
Net Profit Margin: Indicates the percentage of revenue converted into profit.
Return on Assets (ROA): Measures how efficiently assets generate earnings.
Return on Equity (ROE): Assesses how well equity investments generate returns.
The IIA Practice Guide: Auditing Financial Performance emphasizes profitability ratios in evaluating operational success.
Why Other Options Are Incorrect:
Option A (Liquidity Ratios):
Liquidity ratios measure a company's ability to meet short-term obligations rather than its operating success.
Examples: Current Ratio, Quick Ratio.
IIA GTAG 13: Business Performance emphasizes that liquidity ratios relate to short-term financial health, not operating success.
Option C (Solvency Ratios):
Solvency ratios evaluate a company's ability to meet long-term financial obligations, not operating performance.
Examples: Debt-to-Equity Ratio, Interest Coverage Ratio.
Option D (Current Ratio):
The current ratio is a liquidity ratio, measuring whether a company can meet its short-term liabilities with current assets.
It does not directly assess profitability or operational success.
IIA Practice Guide: Auditing Financial Performance – Covers the role of profitability ratios in evaluating a company’s success.
IIA GTAG 13: Business Performance – Discusses financial analysis, including profitability, liquidity, and solvency metrics.
Step-by-Step Explanation:IIA References for Validation:Thus, profitability ratios (B) are the best measures of a company’s operating success over a period.
When would a contract be dosed out?
Options:
When there's a dispute between the contracting parties
When ail contractual obligations have been discharged.
When there is a force majenre.
When the termination clause is enacted.
Answer:
BExplanation:
A contract is closed out when all the contractual terms have been fully satisfied, including the completion of deliverables, final payments, and any post-contract evaluations or obligations.
Correct Answer (B - When all contractual obligations have been discharged)
According to contract management principles and IIA standards, a contract is officially closed out once:
All agreed-upon deliverables have been completed.
All payments and financial obligations are settled.
Final performance evaluations or audits are completed.
The contract is formally reviewed and documented for closure.
The IIA’s GTAG 3: Contract Management Framework supports that contract closure occurs after full performance and obligations are met.
Why Other Options Are Incorrect:
Option A (When there's a dispute between contracting parties):
Disputes do not necessarily close out a contract; instead, they may lead to mediation, renegotiation, or legal action. The contract remains active until resolved.
The IIA’s Practice Guide: Auditing Contracts recommends dispute resolution mechanisms but does not define them as a reason for contract closure.
Option C (When there is a force majeure event):
A force majeure (unforeseen event like natural disasters or war) may suspend or modify contractual obligations but does not always lead to closure.
The contract may be renegotiated or resumed once conditions allow.
Option D (When the termination clause is enacted):
Termination and closure are not the same. Termination means ending the contract before full obligations are met, whereas closure means fulfilling all obligations.
IIA GTAG 3: Contract Management Framework explains that contract termination can occur under specific clauses, but closure happens only after all duties are fulfilled.
IIA GTAG 3: Contract Management Framework – Covers contract lifecycle, including closeout procedures.
IIA Practice Guide: Auditing Contracts – Details contract auditing, dispute resolution, and obligations fulfillment.
Step-by-Step Explanation:IIA References for Validation:
Which of the following activities best illustrates a user's authentication control?
Options:
Identity requests are approved in two steps.
Logs are checked for misaligned identities and access rights.
Users have to validate their identity with a smart card.
Functions can toe performed based on access rights
Answer:
CExplanation:
Authentication control is a security measure used to verify the identity of users before granting access to systems or data. Authentication methods ensure that only authorized individuals can access resources.
Why Option C (Users have to validate their identity with a smart card) is Correct:
Authentication is the process of verifying a user’s identity before granting access.
Smart card authentication is a strong authentication method because it requires a physical device (smart card) and a PIN or biometric verification.
This falls under multi-factor authentication (MFA), enhancing security by combining something the user has (smart card) with something they know (PIN).
Why Other Options Are Incorrect:
Option A (Identity requests are approved in two steps):
Incorrect because this refers to identity approval (authorization), not authentication.
Option B (Logs are checked for misaligned identities and access rights):
Incorrect because log monitoring is a detective control, not an authentication control.
Option D (Functions can be performed based on access rights):
Incorrect because this describes authorization (determining what a user can do after authentication).
IIA GTAG – "Auditing Identity and Access Management": Covers authentication methods like smart cards and multi-factor authentication.
COBIT 2019 – DSS05 (Manage Security Services): Recommends strong authentication controls, including smart card validation.
NIST Cybersecurity Framework – "Access Control Guidelines": Highlights authentication best practices, including smart card use.
IIA References:
What relationship exists between decentralization and the degree, importance, and range of lower-level decision making?
Options:
Mutually exclusive relationship.
Direct relationship.
Intrinsic relationship.
Inverse relationship.
Answer:
BExplanation:
Decentralization refers to the process by which decision-making authority is distributed to lower levels of management within an organization. The degree, importance, and range of decision-making at lower levels are directly related to the extent of decentralization.
Direct Relationship Defined:
As decentralization increases, more decision-making power is transferred to lower levels of the organization.
This means that managers and employees at lower levels are empowered to make a broader range of decisions with greater significance.
The Importance of Lower-Level Decision-Making in a Decentralized Structure:
A decentralized structure allows lower-level managers to respond quickly to operational issues and make important decisions without seeking approval from top management.
This enables increased efficiency, innovation, and adaptability in a dynamic business environment.
IIA's Perspective on Governance and Decision-Making:
According to the International Professional Practices Framework (IPPF) by the Institute of Internal Auditors (IIA), internal auditors must assess the governance structure of an organization, which includes understanding how decision-making authority is allocated.
The IIA’s Three Lines Model highlights the role of management in decision-making, emphasizing the need for a clear and effective delegation of authority.
IIA Standard 2110 – Governance states that internal auditors must evaluate decision-making processes to ensure they align with the organization’s objectives and risk management strategies.
Supporting Business Concepts:
Decentralized organizations like multinational corporations, franchises, and divisional structures benefit from empowering lower levels with decision-making authority.
In contrast, centralized organizations retain control at the top, limiting the scope of decisions at lower levels.
A direct relationship exists because the more decentralized a company is, the greater the responsibility of lower levels in making crucial decisions.
IIA References:
IPPF Standards: Standard 2110 – Governance
IIA’s Three Lines Model – Emphasizing clear delegation of authority
COSO Internal Control Framework – Discusses decentralized decision-making in control environments
Business Knowledge for Internal Auditing (IIA Study Guide) – Governance and decision-making structure
Which of the following IT layers would require the organization to maintain communication with a vendor in a tightly controlled and monitored manner?
Options:
Applications
Technical infrastructure.
External connections.
IT management
Answer:
CExplanation:
Organizations that rely on third-party vendors for IT services must ensure secure and controlled communication, especially in areas where external connections are involved. External connections typically include:
Cloud services (e.g., SaaS, PaaS, IaaS)
Third-party APIs
Remote access (VPNs, firewalls, network gateways)
IoT devices and external sensors
These connections introduce cybersecurity risks, requiring continuous monitoring, vendor communication, and security controls.
(A) Applications.
Incorrect. While application security is important, it is typically managed internally. Vendor involvement is needed for software patches and updates, but communication is not as tightly monitored.
(B) Technical infrastructure.
Incorrect. This layer includes internal IT components like servers, databases, and networks, which are mostly managed in-house. Vendor involvement is required for hardware/software updates but not to the same extent as external connections.
(C) External connections. ✅
Correct. External connections require tightly controlled communication with vendors to prevent security breaches, unauthorized access, and data leaks.
IIA GTAG "Auditing IT Governance" highlights third-party risk management as a key area for IT audits.
IIA Standard 2110 requires organizations to establish governance structures for vendor and IT security management.
(D) IT management.
Incorrect. IT management focuses on internal oversight of IT policies and compliance, but does not necessarily require tightly controlled vendor communication.
IIA GTAG – "Auditing IT Governance"
IIA GTAG – "Managing Third-Party Risks"
IIA Standard 2110 – Governance
Analysis of Answer Choices:IIA References:
An internal auditor reviews a data population and calculates the mean, median, and range. What is the most likely purpose of performing this analytic technique?
Options:
To inform the classification of the data population.
To determine the completeness and accuracy of the data.
To identify whether the population contains outliers.
To determine whether duplicates in the data inflate the range.
Answer:
CExplanation:
When an internal auditor calculates the mean (average), median (middle value), and range (difference between highest and lowest values) of a data population, the primary purpose is to assess the distribution of data and detect anomalies. Let’s analyze the answer choices:
Option A: To inform the classification of the data population.
Incorrect. Classification typically involves categorizing data into specific groups, which requires different statistical or analytical techniques like clustering or decision trees. Mean, median, and range are more useful for identifying distribution patterns.
Option B: To determine the completeness and accuracy of the data.
Incorrect. While summary statistics can highlight extreme values, completeness and accuracy are usually assessed through data reconciliation, validation checks, and comparison with source records.
Option C: To identify whether the population contains outliers.
Correct.
The range (difference between the largest and smallest values) helps to detect extreme values.
The mean and median can show whether the data is symmetrical or skewed (which may indicate outliers).
If the mean is significantly different from the median, it suggests potential outliers pulling the average in one direction.
IIA Reference: Internal auditors use data analytics to detect anomalies and potential fraud by identifying outliers. (IIA GTAG: Auditing with Data Analytics)
Option D: To determine whether duplicates in the data inflate the range.
Incorrect. Duplicates may affect the data set, but range calculations alone do not determine whether duplicates exist. Duplicate identification usually involves checking for repeated entries, not just extreme values.
Which of the following actions would senior management need to consider as part of new IT guidelines regarding the organization's cybersecurity policies?
Options:
Assigning new roles and responsibilities for senior IT management.
Growing use of bring your own devices for organizational matters.
Expansion of operations into new markets with limited IT access.
Hiring new personnel within the IT department for security purposes.
Answer:
BExplanation:
When updating cybersecurity policies, senior management must focus on emerging risks and challenges that impact the organization’s security posture. One major concern is the increasing use of Bring Your Own Device (BYOD) policies, where employees use personal devices for work-related tasks. This introduces security vulnerabilities such as unauthorized access, data leakage, and malware infections.
(A) Incorrect – Assigning new roles and responsibilities for senior IT management.
While defining roles is important, it is a management function rather than a direct cybersecurity policy update.
Cybersecurity policies focus on risks like data protection, access controls, and device security rather than IT management roles.
(B) Correct – Growing use of bring your own devices for organizational matters.
BYOD introduces security risks such as unauthorized access, weak endpoint security, and data loss.
Cybersecurity policies must address encryption, remote access controls, and mobile device management (MDM) solutions.
(C) Incorrect – Expansion of operations into new markets with limited IT access.
While IT expansion poses challenges, cybersecurity policies focus more on data security, threat management, and risk mitigation rather than market access issues.
(D) Incorrect – Hiring new personnel within the IT department for security purposes.
Hiring staff improves security operations but is a resource management decision, not a direct cybersecurity policy concern.
Cybersecurity policies focus on access controls, risk assessments, and compliance requirements.
IIA’s GTAG (Global Technology Audit Guide) – Cybersecurity and Risk Management
Highlights BYOD as a key cybersecurity risk requiring clear policies and controls.
NIST Cybersecurity Framework – Mobile Device Security
Recommends specific policies for managing BYOD risks.
Analysis of Answer Choices:IIA References and Internal Auditing Standards:
Which of the following is an effective preventive control for data center security?
Options:
Motion detectors.
Key card access to the facility.
Security cameras.
Monitoring access to data center workstations
Answer:
BExplanation:
A preventive control is designed to stop security breaches before they happen. In data center security, preventing unauthorized physical access is crucial.
Prevents Unauthorized Entry – Restricts access only to authorized personnel.
Tracks and Logs Access – Records who enters and exits the data center, enhancing security monitoring.
Enhances Security Layers – Often combined with biometric authentication or PINs for stronger access control.
Meets IT Security Standards – Aligns with ISO 27001, NIST, and IIA’s GTAG recommendations on physical security.
A. Motion detectors – These are detective controls, identifying movement but not preventing unauthorized access.
C. Security cameras – Also detective, as they record events but do not prevent physical breaches.
D. Monitoring access to data center workstations – This ensures data integrity but does not prevent physical access.
IIA’s GTAG (Global Technology Audit Guide) on Information Security – Recommends strong physical access controls like key cards.
NIST SP 800-53 (Security and Privacy Controls for Federal Information Systems) – Emphasizes access control as a preventive security measure.
ISO 27001 Annex A.11 (Physical and Environmental Security) – Requires access control for secure areas, including data centers.
Why Key Card Access is the Best Preventive Control?Why Not the Other Options?IIA References:
Which of the following is a benefit from the concept of Internet of Things?
Options:
Employees can choose from a variety of devices they want to utilize to privately read work emails without their employer’s knowledge.
Physical devices, such as thermostats and heat pumps, can be set to react to electricity market changes and reduce costs.
Information can be extracted more efficiently from databases and transmitted to relevant applications for in-depth analytics.
Data mining and data collection from internet and social networks is easier, and the results are more comprehensive
Answer:
BExplanation:
The Internet of Things (IoT) refers to a network of interconnected physical devices that collect and exchange data through the internet. The key benefits of IoT include automation, improved decision-making, cost savings, and efficiency gains.
(A) Employees can choose from a variety of devices they want to utilize to privately read work emails without their employer’s knowledge.
This is incorrect because it focuses on unauthorized access rather than a benefit of IoT. Security and monitoring are major concerns in IoT environments.
IIA Standard 2110 – Governance requires organizations to ensure adequate governance structures for IT and data security.
(B) Physical devices, such as thermostats and heat pumps, can be set to react to electricity market changes and reduce costs. ✅
This is correct because IoT enables smart devices to automatically adjust based on real-time data.
Example: Smart thermostats (e.g., Nest, Honeywell) use IoT to track energy prices and consumption, adjusting temperatures to optimize efficiency.
IIA Practice Guide "Assessing the Governance of Risks in IT Projects" highlights IoT as a tool for operational efficiency and cost savings.
(C) Information can be extracted more efficiently from databases and transmitted to relevant applications for in-depth analytics.
This relates more to big data and data analytics, not necessarily IoT.
IIA GTAG "Auditing IT Governance" discusses IoT in operational efficiency but distinguishes it from data extraction.
(D) Data mining and data collection from the internet and social networks is easier, and the results are more comprehensive.
This describes AI and machine learning rather than IoT, which primarily connects physical devices.
IIA GTAG "Auditing Cybersecurity Risk" highlights IoT risks but does not emphasize social media data mining.
IIA GTAG (Global Technology Audit Guide) – "Auditing IT Governance"
IIA GTAG – "Assessing the Governance of Risks in IT Projects"
IIA Standard 2110 – Governance
IIA GTAG – "Auditing Cybersecurity Risk"
Analysis of Answer Choices:IIA References:Thus, the most appropriate answer is B because IoT improves efficiency by automating energy consumption based on market conditions.
An attacker, posing as a bank representative, convinced an employee to release certain, financial information that ultimately resulted in fraud. Which of the following best describes this cybersecurity risk?
Options:
Shoulder suiting
Pharming,
Phishing.
Social engineering.
Answer:
DExplanation:
Social engineering is a psychological manipulation technique used by attackers to trick individuals into divulging sensitive information. Instead of exploiting technical vulnerabilities, it targets human weaknesses such as trust, fear, or urgency.
Manipulates Human Behavior – The attacker impersonates a trusted entity (a bank representative) to deceive the employee.
Leads to Unauthorized Information Disclosure – The employee unknowingly provides sensitive financial data.
Results in Fraud – The stolen information is misused, causing financial loss.
A. Shoulder Surfing – This occurs when an attacker physically observes someone entering sensitive data (e.g., watching a person type a password).
B. Pharming – This involves redirecting users to a fraudulent website to steal their credentials, not direct impersonation.
C. Phishing – This is a broad category of social engineering that typically involves emails or fake websites, whereas this scenario describes a direct impersonation attack.
IIA’s GTAG on Cybersecurity – Discusses social engineering as a key risk for organizations.
NIST SP 800-61 (Incident Handling Guide) – Identifies social engineering as a common attack vector.
COBIT 2019 (IT Governance Framework) – Highlights human-related cybersecurity risks.
Why Social Engineering is the Correct Answer?Why Not the Other Options?IIA References:
Which of the following should be established by management during implementation of big data systems to enable ongoing production monitoring?
Options:
Key performance indicators.
Reports of software customization.
Change and patch management.
Master data management
Answer:
AExplanation:
When implementing big data systems, organizations must establish ongoing production monitoring to ensure system performance, efficiency, and reliability.
Why Option A (Key performance indicators) is Correct:
KPIs (Key Performance Indicators) measure the effectiveness and success of big data systems.
KPIs help track system efficiency, data processing speed, accuracy, and resource utilization during production.
Examples of KPIs in big data systems include data ingestion rate, processing time, query performance, system uptime, and error rates.
Why Other Options Are Incorrect:
Option B (Reports of software customization):
Incorrect because software customization reports document system modifications but do not monitor system performance.
Option C (Change and patch management):
Incorrect because change and patch management deals with software updates and security fixes, not ongoing performance monitoring.
Option D (Master data management):
Incorrect because master data management focuses on data governance and consistency, not real-time system performance.
IIA GTAG – "Auditing Big Data Systems": Recommends using KPIs to measure the effectiveness of big data implementation.
COBIT 2019 – APO08 (Manage Performance and Capacity): Emphasizes KPI tracking for IT and data system performance.
NIST Big Data Framework: Highlights the importance of KPIs for monitoring big data system performance.
IIA References:
Which of the following biometric access controls uses the most unique human recognition characteristic?
Options:
Facial comparison using photo identification.
Signature comparison.
Voice comparison.
Retinal print comparison.
Answer:
DExplanation:
Biometric access controls use unique physical or behavioral characteristics for identification and security. Among the listed options, retinal print comparison is the most unique and secure, as it relies on the intricate patterns of blood vessels in the retina, which are nearly impossible to replicate or alter.
(A) Facial comparison using photo identification.
Incorrect: Facial recognition is widely used but less unique than retinal scanning because it can be affected by lighting, aging, or facial hair.
IIA GTAG 9 – Identity and Access Management mentions facial recognition as a medium-security method.
(B) Signature comparison.
Incorrect: Signatures can be forged or changed over time, making this a low-security biometric method.
(C) Voice comparison.
Incorrect: Voice patterns are unique but can be affected by illness, background noise, or recording quality, reducing reliability.
(D) Retinal print comparison. (Correct Answer)
Retinal patterns are highly unique, more than fingerprints, and do not change over time.
Difficult to forge, making it the most secure biometric authentication method.
IIA GTAG 9 – Identity and Access Management ranks retinal scanning among the highest security biometric controls.
IIA GTAG 9 – Identity and Access Management: Discusses biometric authentication and ranks retinal scanning as one of the most secure options.
IIA Standard 2120 – Risk Management: Emphasizes strong authentication controls for access security.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (D) Retinal print comparison because it is the most unique, secure, and reliable biometric characteristic for authentication.
Which of the following disaster recovery plans includes recovery resources available at the site, but they may need to be configured to support the production system?
Options:
Warm site recovery plan.
Hot site recovery plan.
Cool site recovery plan.
Cold site recovery plan.
Answer:
AExplanation:
A disaster recovery plan (DRP) outlines how an organization will restore IT operations after a disruption. The type of recovery site determines how quickly systems can be brought back online.
Why a Warm Site Recovery Plan is Correct?A warm site is a partially configured backup location with some hardware and software ready, but it requires additional configuration before it can fully support production operations.
Faster than a Cold Site – Unlike a cold site, a warm site has pre-installed infrastructure, reducing downtime.
Requires Some Setup – Unlike a hot site, which is fully operational, a warm site needs configuration and software setup before use.
Balances Cost and Readiness – Less expensive than a hot site while offering faster recovery than a cold site.
B. Hot site recovery plan – A hot site is fully operational and can immediately take over in case of failure.
C. Cool site recovery plan – This is not a standard industry term in disaster recovery.
D. Cold site recovery plan – A cold site has only basic infrastructure (e.g., power and space) and lacks pre-installed hardware/software, requiring much more setup time.
IIA’s GTAG on Business Continuity Management – Defines recovery site options based on operational risk.
ISO 22301 (Business Continuity Management System) – Specifies warm sites as an intermediate recovery solution.
NIST SP 800-34 (Contingency Planning Guide for IT Systems) – Describes warm sites as partially pre-configured recovery environments.
Why Not the Other Options?IIA References:
According to 11A guidance on IT, which of the following are indicators of poor change management?
1. Inadequate control design.
2. Unplanned downtime.
3. Excessive troubleshooting .
4. Unavailability of critical services.
Options:
2 and 3 only.
1, 2, and 3 only
1, 3, and 4 only
2, 3, and 4 only
Answer:
DExplanation:
Effective change management ensures that IT changes (such as software updates, system modifications, or infrastructure upgrades) are well-controlled, minimizing disruptions. Poor change management leads to instability, inefficiencies, and operational risks.
Unplanned Downtime (2) – Indicates that changes are being implemented without proper testing or failover planning, disrupting business operations.
Excessive Troubleshooting (3) – Suggests that changes are causing recurring issues, leading to increased workload for IT support teams.
Unavailability of Critical Services (4) – Highlights that change-related failures are affecting essential business functions, indicating improper risk assessment.
While inadequate control design is a general IT risk, it is not a direct indicator of poor change management. Instead, it relates more to weaknesses in IT governance and security frameworks.
IIA’s GTAG (Global Technology Audit Guide) on Change Management – Identifies unplanned downtime, excessive troubleshooting, and service unavailability as key red flags of poor change management.
COBIT 2019 (Governance and Management of IT) – Emphasizes structured change management to minimize disruptions.
ITIL Change Management Framework – Highlights these issues as symptoms of ineffective change control.
Why 2, 3, and 4 Are Indicators of Poor Change Management?Why Not Option 1 (Inadequate Control Design)?IIA References:✅ Final Answer: D. 2, 3, and 4 only.
Which of the following best describes a transformational leader, as opposed to a transactional leader?
Options:
The leader searches for deviations from the rules and standards and intervenes when deviations exist.
The leader intervenes only when performance standards are not met.
The leader intervenes to communicate high expectations.
The leader does not intervene to promote problem-solving
Answer:
CExplanation:
A transformational leader focuses on inspiring and motivating employees to exceed expectations, emphasizing vision, innovation, and long-term goals rather than just rule enforcement or performance monitoring.
(A) The leader searches for deviations from the rules and standards and intervenes when deviations exist.
Incorrect: This describes a transactional leader, who focuses on correcting errors and enforcing rules rather than inspiring employees.
(B) The leader intervenes only when performance standards are not met.
Incorrect: This describes a passive transactional leader, who waits for issues before taking action.
(C) The leader intervenes to communicate high expectations. (Correct Answer)
Transformational leaders set high expectations, inspire employees to achieve them, and foster a culture of continuous improvement.
IIA Standard 2110 – Governance highlights the importance of leadership in driving organizational performance.
Transformational leadership aligns with COSO’s principles of strong governance and strategic vision.
(D) The leader does not intervene to promote problem-solving.
Incorrect: A transformational leader actively promotes problem-solving by encouraging innovation and continuous improvement.
IIA Standard 2110 – Governance: Recognizes leadership's role in fostering a strong ethical and performance-driven culture.
COSO ERM – Governance and Culture: Highlights leadership’s role in shaping strategic direction.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (C) because a transformational leader inspires employees by setting high expectations and motivating them to achieve organizational goals.
Which of the following practices circumvents administrative restrictions on smart devices, thereby increasing data security risks?
Options:
Rooting.
Eavesdropping.
Man in the middle.
Session hijacking.
Answer:
AExplanation:
Definition of Rooting:
Rooting (on Android) or Jailbreaking (on iOS) is the process of bypassing manufacturer and administrative security controls on a smart device.
This allows users to gain full control (root access) over the operating system, which can override security restrictions and allow installation of unauthorized applications.
How Rooting Increases Data Security Risks:
Bypassing Security Measures: Rooting removes built-in security protections, making the device more vulnerable to malware, unauthorized access, and data breaches.
Exposure to Malicious Apps: Rooted devices can install third-party applications that are not vetted by official app stores, increasing the risk of data theft, spyware, and ransomware attacks.
Circumventing Enterprise Security Policies: Many organizations use Mobile Device Management (MDM) to enforce security policies, but rooted devices can bypass these controls, exposing corporate data to cyber threats.
Increased Risk of Privilege Escalation Attacks: Attackers can exploit root access to take full control of the device, leading to unauthorized access to sensitive information.
IIA’s Perspective on Cybersecurity Risks:
IIA Standard 2110 – Governance emphasizes the importance of protecting sensitive data and ensuring compliance with IT security policies.
IIA’s GTAG (Global Technology Audit Guide) on Information Security warns against the dangers of rooted or jailbroken devices, as they compromise cybersecurity defenses.
NIST Cybersecurity Framework and ISO 27001 Information Security Standards identify unauthorized modifications to devices as a critical security risk.
Eliminating Incorrect Options:
B. Eavesdropping: This refers to intercepting communications (e.g., listening in on phone calls or network traffic) but does not involve circumventing administrative restrictions.
C. Man-in-the-Middle (MITM) Attack: This is an attack where an attacker intercepts and alters communication between two parties but does not involve rooting a device.
D. Session Hijacking: This attack involves stealing session tokens to impersonate a user but is unrelated to bypassing security controls on devices.
IIA References:
IIA Standard 2110 – Governance and IT Security
IIA GTAG – Information Security Risks
NIST Cybersecurity Framework
ISO 27001 Information Security Standards
An internal auditor is reviewing key phases of a software development project. Which of the following would; the auditor most likely use to measure the project team's performance related to how project tasks are completed?
Options:
A balanced scorecard.
A quality audit
Earned value analysis.
Trend analysis
Answer:
CExplanation:
Earned Value Analysis (EVA) is a project management technique that integrates scope, time, and cost data to measure project performance and progress objectively. EVA allows internal auditors to assess whether a software development project is on track by comparing planned work with completed work and actual costs.
Here’s why EVA is the most appropriate choice:
Evaluates Project Progress and Performance – EVA measures how much work has been completed against the planned schedule and budget, helping auditors analyze project efficiency.
Identifies Deviations – It highlights cost overruns or delays in task completion, which is critical for software development projects.
Uses Key Metrics – EVA includes essential indicators like:
Planned Value (PV) – The budgeted cost of work scheduled.
Earned Value (EV) – The value of actual work performed.
Actual Cost (AC) – The real cost incurred for work completed.
Schedule Variance (SV) and Cost Variance (CV) – Indicators of deviations from planned performance.
Supports Risk-Based Internal Audit Approach – The IIA emphasizes risk-based auditing, and EVA helps auditors assess risks related to project cost overruns, schedule slippage, and performance gaps.
A. A Balanced Scorecard – This measures overall organizational performance across perspectives (financial, customer, internal processes, and learning & growth), but it is not specifically designed for evaluating project task completion.
B. A Quality Audit – This focuses on compliance with quality standards and does not measure project task completion efficiency.
D. Trend Analysis – This evaluates patterns over time but does not provide a structured measurement of project progress in terms of cost, time, and completion percentage.
The IIA’s GTAG (Global Technology Audit Guide) on IT Project Management – Recommends using earned value analysis for project auditing.
IIA’s International Professional Practices Framework (IPPF) – Performance Standard 2120 (Risk Management) – Emphasizes the need for internal auditors to evaluate the effectiveness of project risk management, which EVA supports.
COSO’s Enterprise Risk Management (ERM) Framework – Encourages structured performance measurement techniques like EVA to monitor projects.
Why Not the Other Options?IIA References:Thus, Earned Value Analysis (EVA) is the correct answer because it provides a precise, quantitative way to measure project performance. ✅
Which of the following best describes a detective control designed to protect an organization from cyberthreats and attacks?
Options:
A list of trustworthy, good traffic and a list of unauthorized, blocked traffic.
Monitoring for vulnerabilities based on industry intelligence.
Comprehensive service level agreements with vendors.
Firewall and other network perimeter protection tools.
Answer:
BExplanation:
A detective control is a security measure that identifies and alerts an organization to potential cyberthreats after they occur but before they cause harm. Detective controls do not prevent attacks but help detect them in a timely manner.
Why Option B (Monitoring for vulnerabilities based on industry intelligence) is Correct:
Continuous monitoring for vulnerabilities helps detect emerging threats, security breaches, and weaknesses in IT systems.
Uses threat intelligence feeds, security information and event management (SIEM) systems, and intrusion detection systems (IDS).
Helps organizations respond quickly to cyberattacks by identifying patterns, suspicious activity, or known vulnerabilities.
Why Other Options Are Incorrect:
Option A (A list of trustworthy, good traffic and a list of unauthorized, blocked traffic):
Incorrect because this describes a whitelisting/blacklisting technique, which is a preventive control, not a detective control.
Option C (Comprehensive service level agreements with vendors):
Incorrect because service level agreements (SLAs) ensure contractual obligations, but do not detect security threats.
Option D (Firewall and other network perimeter protection tools):
Incorrect because firewalls are preventive controls, designed to block unauthorized access, not detect threats after they occur.
IIA GTAG – "Auditing Cybersecurity Risks": Discusses detective controls such as vulnerability monitoring and threat intelligence.
COBIT 2019 – DSS05 (Manage Security Services): Recommends continuous monitoring for cyber threats as a detective control.
NIST Cybersecurity Framework – Detect Function: Highlights vulnerability management and threat monitoring as key detective measures.
IIA References:Thus, the correct answer is B. Monitoring for vulnerabilities based on industry intelligence.
According to IIA guidance on IT, which of the following strategies would provide the most effective access control over an automated point-of-sale system?
Options:
Install and update anti-virus software.
Implement data encryption techniques.
Set data availability by user need.
Upgrade firewall configuration
Answer:
CExplanation:
Access control is about ensuring that only authorized individuals can access specific data, based on their role and necessity. The Principle of Least Privilege (PoLP) dictates that users should only have access to the data they need for their job.
Minimizes Unauthorized Access Risks – Prevents employees from accessing sensitive data unnecessarily.
Supports Segregation of Duties (SoD) – Critical in preventing fraud and security breaches.
Enhances Compliance – Meets regulatory requirements like GDPR, PCI-DSS, and SOX, which demand strict access controls.
Strengthens System Security – Reduces potential damage from malware, insider threats, or data breaches.
A. Install and update anti-virus software – Important for cybersecurity but does not directly control user access.
B. Implement data encryption techniques – Protects stored or transmitted data but does not define access rights.
D. Upgrade firewall configuration – Controls network traffic, not user-specific access within an automated system.
IIA’s GTAG on Access Management and Controls – Recommends setting data access based on user needs to prevent fraud and misuse.
COBIT 2019 (Governance and Management of Enterprise IT) – Advocates for role-based access controls.
ISO 27001 Annex A.9 (Access Control) – Stresses the importance of restricting access based on business requirements.
Why Setting Data Availability by User Need is the Best Strategy?Why Not the Other Options?IIA References:✅ Final Answer: C. Set data availability by user need.
A newly appointed board member received an email that appeared to be from the company's CEO. The email stated:
“Good morning. As you remember, the closure of projects is our top priority. Kindly organize prompt payment of the attached invoice for our new solar energy partners.” The board member quickly replied to the email and asked under which project the expense should be accounted. Only then did he realize that the sender 's mail domain was different from the company's. Which of the following cybersecurity risks nearly occurred in the situation described?
Options:
A risk of spyware and malware.
A risk of corporate espionage.
A ransomware attack risk.
A social engineering risk.
Answer:
DExplanation:
The described situation is a classic social engineering attack, specifically a phishing or CEO fraud (business email compromise) attempt. Social engineering exploits human psychology rather than technical vulnerabilities. In this case, the attacker attempted to impersonate the CEO and trick the board member into making an unauthorized payment.
(A) Incorrect – A risk of spyware and malware.
Spyware and malware typically involve malicious software installed on a device, which is not the case here.
This attack relied on deception rather than malware to obtain unauthorized funds.
(B) Incorrect – A risk of corporate espionage.
Corporate espionage involves unauthorized data theft, sabotage, or insider threats.
The attacker here attempted financial fraud, not intellectual property theft.
(C) Incorrect – A ransomware attack risk.
Ransomware encrypts files and demands payment for decryption.
There is no mention of system encryption or ransom demands in this case.
(D) Correct – A social engineering risk.
The attacker impersonated the CEO and used urgency to manipulate the board member into processing a fraudulent payment.
This technique is a business email compromise (BEC) scam, a well-known social engineering tactic.
IIA’s GTAG (Global Technology Audit Guide) – Cybersecurity Risks and Controls
Discusses social engineering and its impact on financial fraud.
NIST Cybersecurity Framework – Social Engineering Threats
Defines social engineering tactics, including email impersonation and phishing.
COBIT Framework – Information Security Governance
Recommends controls to mitigate social engineering risks, such as employee training and email authentication mechanisms.
Analysis of Answer Choices:IIA References and Internal Auditing Standards:
While performing an audit of a car tire manufacturing plant, an internal auditor noticed a significant decrease in the number of tires produced from the previous operating
period. To determine whether worker inefficiency caused the decrease, what additional information should the auditor request?
Options:
Total tire production labor hours for the operating period.
Total tire production costs for the operating period.
Plant production employee headcount average for the operating period.
The production machinery utilization rates.
Answer:
AExplanation:
Understanding the Audit Concern:
The internal auditor observed a significant decline in tire production and needs to assess whether worker inefficiency is the cause.
Worker inefficiency is typically measured in terms of productivity, which relates output (number of tires produced) to input (labor hours worked).
Why Option A is Correct?
Total tire production labor hours provide a direct measure of worker efficiency. By analyzing the number of tires produced per labor hour, the auditor can determine whether efficiency has declined.
If labor hours remained constant or increased while production declined, this indicates inefficiency.
This approach aligns with IIA Standard 1220 – Due Professional Care, which requires auditors to use appropriate analysis to support findings.
Additionally, per IIA Standard 2310 – Identifying Information, auditors must obtain sufficient and relevant data to support conclusions.
Why Other Options Are Incorrect?
Option B (Total tire production costs):
Total costs include factors beyond labor efficiency, such as raw material prices, machinery maintenance, and overhead. This does not directly measure worker productivity.
Option C (Plant production employee headcount average):
Employee headcount alone does not reflect efficiency; it does not account for hours worked or individual performance.
Option D (Production machinery utilization rates):
Machinery efficiency is important but does not directly measure worker inefficiency. A decline in machine utilization could be due to maintenance, material shortages, or other non-labor factors.
Labor hours per unit of production (tires produced per labor hour) is the best metric for evaluating worker efficiency.
IIA Standards 1220 and 2310 support data-driven, relevant information gathering for audit conclusions.
Final Justification:IIA References:
IPPF Standard 1220 – Due Professional Care
IPPF Standard 2310 – Identifying Information
Performance Standard 2320 – Analysis and Evaluation
An analytical model determined that on Friday and Saturday nights the luxury brands stores should be open for extended hours and with a doubled number of employees
present; while on Mondays and Tuesdays costs can be minimized by reducing the number of employees to a minimum and opening only for evening hours Which of the
following best categorizes the analytical model applied?
Options:
Descriptive.
Diagnostic.
Prescriptive.
Prolific.
Answer:
CExplanation:
Descriptive Analytics – Answers "What happened?" by summarizing past data.
Diagnostic Analytics – Answers "Why did it happen?" by identifying causes of trends or issues.
Prescriptive Analytics – Answers "What should we do?" by providing data-driven recommendations and optimal solutions for decision-making.
Prolific Analytics – This is not a recognized category in standard analytics models.
The model makes specific recommendations for store operations (extended hours, staffing adjustments).
It optimizes resource allocation based on demand patterns.
It goes beyond identifying past trends (descriptive) or diagnosing causes (diagnostic) and provides actionable solutions.
A. Descriptive – Would only summarize sales data but not suggest changes.
B. Diagnostic – Would explain why luxury stores see higher traffic on weekends but would not recommend actions.
D. Prolific – Not a standard analytics category.
IIA’s GTAG on Data Analytics – Describes prescriptive analytics as the highest level of business intelligence, driving decision-making.
COSO’s Enterprise Risk Management (ERM) Framework – Encourages data-driven decision-making using prescriptive models.
COBIT 2019 on IT Governance – Recommends leveraging prescriptive analytics for operational efficiency.
Types of Analytical Models in Business Intelligence:Why Prescriptive Analytics is the Best Choice?Why Not the Other Options?IIA References:✅ Final Answer: C. Prescriptive.
According to 11A guidance on it; which of the following statements is true regarding websites used in e-commerce transactions?
Options:
HTTP sites provide sufficient security to protect customers' credit card information.
Web servers store credit cardholders' information submitted for payment.
Database servers send cardholders’ information for authorization in clear text.
Payment gatewaysauthorizecredit cardonlinepayments.
Answer:
DExplanation:
E-commerce transactions involve multiple security layers to ensure the protection of customers' sensitive financial information. The correct answer is D, as payment gateways serve as intermediaries that authorize online credit card transactions by securely transmitting the payment details to the bank or card networks for approval. Let’s examine each option carefully:
Option A: HTTP sites provide sufficient security to protect customers' credit card information.
Incorrect. HyperText Transfer Protocol (HTTP) does not provide encryption, meaning that data transmitted over an HTTP connection can be intercepted by malicious actors. Instead, Secure HTTP (HTTPS), which uses Secure Sockets Layer (SSL) or Transport Layer Security (TLS), is required to encrypt the data.
IIA Reference: Internal auditors evaluating e-commerce security should verify that organizations use HTTPS for secure transactions. (IIA GTAG: Information Security Governance)
Option B: Web servers store credit cardholders' information submitted for payment.
Incorrect. While web servers may temporarily process customer data, they should not store sensitive credit card information due to security risks. Instead, organizations follow the Payment Card Industry Data Security Standard (PCI DSS), which mandates secure storage and encryption protocols.
IIA Reference: IIA Standards recommend compliance with PCI DSS to protect sensitive payment information. (IIA Practice Guide: Auditing IT Governance)
Option C: Database servers send cardholders’ information for authorization in clear text.
Incorrect. Transmitting cardholder data in clear text is a severe security vulnerability. Secure encryption protocols such as SSL/TLS or tokenization must be used to protect data in transit.
IIA Reference: Internal auditors should ensure encryption measures are in place for financial transactions. (IIA GTAG: Auditing Cybersecurity Risk)
Option D: Payment gateways authorize credit card online payments.
Correct. Payment gateways act as secure intermediaries between merchants and payment processors, verifying the transaction details before authorization. This ensures a secure transaction by encrypting sensitive data before transmitting it for approval.
IIA Reference: IIA guidance on IT controls emphasizes the importance of secure payment processing through payment gateways. (IIA GTAG: Managing and Auditing IT Vulnerabilities)
Which of the following statements is true regarding user-developed applications (UDAs)?
Options:
UDAs are less flexible and more difficult to configure than traditional IT applications.
Updating UDAs may lead to various errors resulting from changes or corrections.
UDAs typically are subjected to application development and change management controls.
Using UDAs typically enhances the organization's ability to comply with regulatory factors.
Answer:
BExplanation:
User-Developed Applications (UDAs) are applications, spreadsheets, databases, or tools created and maintained by end-users rather than IT departments. They provide flexibility but also introduce risks related to security, accuracy, and change management.
Why Option B is Correct:
UDAs lack formal change management controls.
Since they are typically not subject to rigorous testing and documentation, modifications may introduce errors.
Updating or correcting a formula, macro, or script in a UDA may have unintended consequences that go unnoticed, leading to data integrity issues.
Why Other Options Are Incorrect:
Option A (UDAs are less flexible and more difficult to configure than traditional IT applications):
Incorrect. UDAs are more flexible and easier to modify compared to traditional IT applications, which undergo strict change controls.
Option C (UDAs typically are subjected to application development and change management controls):
Incorrect. Most UDAs lack formal governance or IT oversight. They are typically developed by business users with little or no structured IT controls.
Option D (Using UDAs typically enhances the organization’s ability to comply with regulatory factors):
Incorrect. UDAs introduce compliance risks due to lack of security, audit trails, and formal change controls.
IIA GTAG – "Auditing User-Developed Applications": Discusses risks and controls related to UDAs.
IIA Practice Advisory 2130-1 (Control Risk Self-Assessment): Highlights the importance of internal controls over UDAs.
COSO Internal Control – Integrated Framework: Recommends applying IT general controls (ITGCs) to UDAs.
IIA References:Thus, the correct answer is B. Updating UDAs may lead to various errors resulting from changes or corrections.
An organization decided to reorganize into a flatter structure. Which of the following changes would be expected with this new structure?
Options:
Lower costs.
Slower decision making at the senior executive level.
Limited creative freedom in lower-level managers.
Senior-level executives more focused on short-term, routine decision making
Answer:
AExplanation:
A flatter organizational structure reduces hierarchical levels and promotes greater autonomy for employees. The primary benefit is cost reduction due to fewer management layers and streamlined decision-making.
Fewer Management Layers – Reduces the number of mid-level managers, decreasing salary expenses.
Increased Operational Efficiency – Less bureaucracy leads to faster decision-making, lowering administrative costs.
Encourages Employee Autonomy – Reduces dependence on supervision, improving productivity.
B. Slower decision-making at the senior executive level – Incorrect because flatter structures lead to faster decision-making due to fewer approval levels.
C. Limited creative freedom in lower-level managers – Incorrect because flatter structures provide more autonomy and innovation opportunities.
D. Senior-level executives more focused on short-term, routine decision-making – Incorrect because executives in a flatter structure focus on strategic, high-level decisions, delegating routine tasks.
IIA’s GTAG on Governance and Risk Management – Discusses the financial and operational impacts of different organizational structures.
COSO’s Enterprise Risk Management (ERM) Framework – Emphasizes how flatter structures reduce operational inefficiencies and costs.
COBIT 2019 (Governance Framework) – Highlights the impact of organizational structure on financial performance.
Why Lower Costs is the Correct Answer?Why Not the Other Options?IIA References:
Which of the following best describes a cyberattacK in which an organization faces a denial-of-service threat created through malicious data encryption?
Options:
Phishing.
Ransomware.
Hacking.
Makvare
Answer:
BExplanation:
Ransomware is a type of cyberattack where malicious software encrypts an organization's data, making it inaccessible until a ransom is paid to the attacker. This aligns with the question’s scenario, where denial-of-service is caused by malicious data encryption.
Let's analyze the options:
A. Phishing:
Phishing is a social engineering attack that tricks individuals into providing sensitive information, such as usernames, passwords, or credit card numbers. It does not involve encryption or direct denial-of-service.
B. Ransomware (✅ Correct Answer):
Ransomware encrypts critical data and demands a ransom for its release, effectively causing a denial-of-service scenario since the victim cannot access their own systems.
Some well-known ransomware attacks include WannaCry and NotPetya.
C. Hacking:
Hacking is a broad term for unauthorized access to systems but does not specifically refer to denial-of-service through encryption. Ransomware is a specific type of hacking attack.
D. Malware:
Malware (malicious software) is a general category that includes viruses, trojans, worms, spyware, and ransomware. While ransomware is a type of malware, not all malware encrypts data to demand ransom.
IIA Global Technology Audit Guide (GTAG) – Auditing Cybersecurity Risks – Discusses various cyber threats, including ransomware.
NIST Cybersecurity Framework (CSF) – Defines ransomware as a major threat that disrupts business continuity.
COBIT Framework (Control Objectives for Information and Related Technologies) – Addresses risks associated with ransomware and how internal auditors should assess controls.
ISO/IEC 27001 – Information Security Management Systems (ISMS) – Identifies the importance of cybersecurity measures to prevent ransomware attacks.
IIA References:
An internal auditor for a pharmaceutical company as planning a cybersecurity audit and conducting a risk assessment. Which of the following would be considered the most significant cyber threat to the organization?
Options:
Cybercriminals hacking into the organization's time and expense system to collect employee personal data.
Hackers breaching the organization's network to access research and development reports
A denial-of-service attack that prevents access to the organization's website.
A hacker accessing she financial information of the company
Answer:
BExplanation:
When conducting a cybersecurity risk assessment, an internal auditor must evaluate the most significant threats based on their potential impact on the organization. In the pharmaceutical industry, intellectual property (IP), such as research and development (R&D) data, is one of the most valuable and sensitive assets.
(A) Cybercriminals hacking into the organization's time and expense system to collect employee personal data:While the loss of employee personal data is a serious concern due to privacy and regulatory implications (e.g., GDPR, CCPA), it does not pose as critical a threat as the loss of proprietary pharmaceutical research.
(B) Hackers breaching the organization's network to access research and development reports (Correct Answer):R&D reports contain proprietary drug formulas, clinical trial results, and patent-pending innovations, making them highly valuable to competitors and cybercriminals. A breach could lead to intellectual property theft, financial losses, loss of competitive advantage, and regulatory non-compliance (e.g., FDA, EMA requirements). This is considered the most significant threat because:
It could result in billions of dollars in lost revenue.
Competitors or state-sponsored hackers could exploit stolen research.
It could disrupt drug development and approval processes.
(C) A denial-of-service (DoS) attack that prevents access to the organization's website:While DoS attacks can damage an organization's reputation and disrupt operations, they generally do not cause the same level of financial or strategic harm as the loss of critical R&D data. Most organizations have cybersecurity measures (e.g., load balancers, CDNs) to mitigate DoS risks.
(D) A hacker accessing the financial information of the company:Unauthorized access to financial data can be serious, leading to fraud or reputational damage. However, publicly traded companies already disclose much of their financial data, and financial breaches typically have a lower long-term impact compared to intellectual property theft.
IIA Global Technology Audit Guide (GTAG) 15: Information Security Governance: Recommends that internal auditors prioritize risks that impact strategic assets, such as intellectual property.
IIA Standard 2120 - Risk Management: Requires internal auditors to evaluate the organization’s risk management processes, emphasizing risks with significant financial and operational consequences.
IIA Practice Advisory 2110-2: Assessing the Adequacy of Risk Management Processes: Highlights that internal auditors must identify risks that could threaten the organization’s long-term objectives, such as IP theft.
COSO ERM Framework: Encourages prioritization of risks that have high impact on an organization’s value and strategic objectives, such as cyber threats to proprietary research.
Analysis of Each Option:IIA References:Conclusion:Given the pharmaceutical industry's reliance on proprietary R&D, a breach compromising research reports represents the most significant cyber threat. Therefore, option (B) is the correct answer.
An organization prepares a statement of privacy to protect customers' personal information. Which of the following might violate the privacy principles?
Options:
Customers can access and update personal information when needed.
The organization retains customers' personal information indefinitely.
Customers reserve the right to reject sharing personal information with third parties.
The organization performs regular maintenance on customers' personal information.
Answer:
BExplanation:
Organizations must comply with privacy principles that emphasize data retention limitations. Keeping personal data indefinitely violates privacy laws and regulations such as the General Data Protection Regulation (GDPR) and California Consumer Privacy Act (CCPA).
Privacy Regulations Require Data Minimization:
GDPR Article 5(1)(e) states that personal data should only be kept for as long as necessary for the intended purpose.
IIA GTAG 4: Management of IT Auditing also advises against excessive data retention.
Security and Risk Concerns:
Storing data indefinitely increases the risk of data breaches.
IIA Standard 2110 – Governance emphasizes the need for proper information security governance to protect personal data.
Legal and Compliance Issues:
Organizations are required to define retention policies to prevent unauthorized or unnecessary storage of personal data.
A. Customers can access and update personal information when needed. (Incorrect)
Reason: Allowing customers to access and update their information aligns with privacy principles such as data accuracy and transparency.
C. Customers reserve the right to reject sharing personal information with third parties. (Incorrect)
Reason: This supports data control rights, which is consistent with privacy standards like opt-in and opt-out policies.
D. The organization performs regular maintenance on customers' personal information. (Incorrect)
Reason: Regular maintenance (e.g., updates, corrections, deletions) enhances data accuracy and security, aligning with privacy best practices.
IIA Global Technology Audit Guide (GTAG) 4: Management of IT Auditing – Discusses data privacy principles.
IIA Standard 2110 – Governance – Ensures data security and regulatory compliance.
IIA GTAG 8: Auditing Application Controls – Covers data retention policies and privacy compliance.
Privacy Regulations: GDPR (Article 5), CCPA (Section 1798.105) – Require organizations to delete data once it is no longer needed.
Why is Indefinite Retention a Violation?Analysis of Incorrect Answers:IIA References:Thus, the correct answer is B. The organization retains customers' personal information indefinitely.
While conducting' audit procedures at the organization's data center an internal auditor noticed the following:
- Backup media was located on data center shelves.
- Backup media was organized by date.
- Backup schedule was one week in duration.
The system administrator was able to present restore logs.
Which of the following is reasonable for the internal auditor to conclude?
Options:
Backup media is not properly stored, as the storage facility should be off-site.
Backup procedures are adequate and appropriate according to best practices.
Backup media is not properly indexed, as backup media should be indexed by system, not date.
Backup schedule is not sufficient, as full backup should be conducted daily.
Answer:
AExplanation:
The auditor's observation indicates that backup media is stored on-site in the data center, which is a major risk in disaster recovery and business continuity planning (BCP). Best practices recommend storing backup media off-site to prevent data loss due to fires, floods, cyberattacks, or other disasters affecting the primary site.
Off-Site Storage Reduces Disaster Risks:
Keeping backups only at the primary data center means that any physical disaster (fire, flood, theft, or power surge) can destroy both primary and backup data.
Best practices require off-site or cloud-based backup storage to ensure data recovery in case of emergencies.
Regulatory and Compliance Considerations:
IIA Standard 2110 (Governance): Emphasizes disaster recovery policies to protect critical IT assets.
ISO/IEC 27001 (Information Security Management System): Recommends storing backups in a geographically separate location.
NIST SP 800-34 (Contingency Planning Guide for Federal Information Systems): Requires off-site storage to ensure effective disaster recovery.
Why the Other Options Are Incorrect:
B. Backup procedures are adequate and appropriate according to best practices: ❌
Incorrect, as on-site-only storage violates best practices for disaster recovery.
C. Backup media is not properly indexed, as backup media should be indexed by system, not date: ❌
While indexing is important, the main issue here is improper storage, not indexing methods.
D. Backup schedule is not sufficient, as full backup should be conducted daily: ❌
Backup frequency depends on business needs; a weekly backup is common for many organizations.
However, the biggest concern here is lack of off-site storage, not frequency.
IIA GTAG (Global Technology Audit Guide) on Business Continuity and Disaster Recovery: Recommends off-site storage for backups.
ISO/IEC 27001 – Information Security Controls (A.12.3.1): Requires backup data to be securely stored off-site.
COBIT 5 Framework – DSS04 (Manage Continuity): Supports off-site backups for IT continuity.
Step-by-Step Justification:IIA References:Thus, the correct answer is A. Backup media is not properly stored, as the storage facility should be off-site. ✅
How can the concept of relevant cost help management with behavioral analyses?
Options:
It explains the assumption mat both costs and revenues are linear through the relevant range
It enables management to calculate a minimum number of units to produce and sell without having to incur a loss.
It enables management to predict how costs such as the depreciation of equipment will be affected by a change in business decisions
It enables management to make business decisions, as it explains the cost that will be incurred for a given course of action
Answer:
DExplanation:
Relevant cost refers to costs that will change depending on a specific business decision. It is crucial for decision-making as it helps management assess the financial impact of alternatives.
Relevant costs focus on future costs that differ between decision alternatives.
They help management analyze how different choices impact profitability.
This supports decision-making in areas such as pricing, outsourcing, and product discontinuation.
A. It explains the assumption that both costs and revenues are linear through the relevant range → Incorrect. While linear cost behavior is often assumed, it is not the primary purpose of relevant cost analysis.
B. It enables management to calculate a minimum number of units to produce and sell without having to incur a loss → Incorrect. This describes break-even analysis, not relevant cost analysis.
C. It enables management to predict how costs such as the depreciation of equipment will be affected by a change in business decisions → Incorrect. Depreciation is a sunk cost and is not considered relevant for decision-making.
The IIA’s Practice Guide: Financial Decision-Making and Internal Audit’s Role outlines how relevant cost analysis aids business strategy.
International Professional Practices Framework (IPPF) Standard 2120 states that internal auditors should assess management’s cost-analysis techniques.
Managerial Accounting Concepts (by IMA and COSO) emphasize relevant costs in strategic decision-making.
Why Option D is Correct?Explanation of the Other Options:IIA References & Best Practices:Thus, the correct answer is D. It enables management to make business decisions, as it explains the cost that will be incurred for a given course of action.
According to Herzberg's Two-Factor Theory of Motivation, which of the following is a factor mentioned most often by satisfied employees?
Options:
Relationship with supervisor
Salary
Security.
Achievement
Answer:
CThe chief audit executive (CAE) has been asked to evaluate the chief technology officer's proposal to outsource several key functions in the organization's IT department. Which of the following would be the most appropriate action for the CAE to determine whether the proposal aligns with the organization's strategy?
Options:
Understand strategic context and evaluate whether supporting information is reliable and complete.
Ascertain whether governance and approval processes are transparent, documented, and completed.
Perform a due diligence review or asses management's review of provider operations.
Identify key performance measures and data sources.
Answer:
AExplanation:
The chief audit executive (CAE) plays a crucial role in evaluating strategic decisions, including outsourcing IT functions. The most appropriate first step is to assess whether the proposal aligns with the organization's overall strategy and verify that the supporting information is reliable and complete before making further evaluations.
Strategic Alignment:
The CAE must first determine whether outsourcing supports the organization’s long-term objectives, risk tolerance, and business goals.
Reliability of Supporting Information:
Before evaluating costs, risks, or operational impacts, the CAE must ensure that management’s data and assumptions are accurate and complete.
IIA Standards on Governance and Risk Management:
IIA Standard 2110 - Governance requires auditors to evaluate decision-making processes, including outsourcing.
IIA Standard 2120 - Risk Management emphasizes assessing risks associated with major decisions like outsourcing.
B. Ascertain whether governance and approval processes are transparent, documented, and completed:
While governance is important, this step comes after verifying strategic alignment.
C. Perform a due diligence review or assess management’s review of provider operations:
Due diligence is a later step in outsourcing evaluation, not the first priority.
D. Identify key performance measures and data sources:
Key performance measures are useful for monitoring outsourcing after approval, but they do not determine initial alignment with strategy.
IIA Standard 2110 - Governance: Requires internal auditors to evaluate whether key decisions align with organizational objectives.
IIA Standard 2120 - Risk Management: Internal auditors must assess potential risks and verify the reliability of information used for decision-making.
COBIT Framework - IT Governance: Emphasizes strategic alignment of IT decisions, including outsourcing.
Key Reasons Why Option A is Correct:Why Other Options Are Incorrect:IIA References:Thus, the correct answer is A. Understand strategic context and evaluate whether supporting information is reliable and complete.
In an organization that produces chocolate, the leadership team decides that the organization will open a milk production facility for its milk chocolate. Which of the following strategies have the organization chosen?
Options:
Vertical integration.
Unrelated diversification.
Differentiation
Focus
Answer:
AExplanation:
Understanding Vertical Integration:
Vertical integration is a business strategy where a company expands its operations into different stages of its supply chain.
In this case, the chocolate-producing company is moving upstream by producing its own milk rather than purchasing it from suppliers.
Why This Is Vertical Integration:
The company controls more of its supply chain, reducing dependency on external suppliers.
Benefits include:
Cost savings on raw materials (by producing instead of buying).
Improved quality control (since the company controls milk production).
Greater market control (reducing reliance on third-party vendors).
Why Other Options Are Incorrect:
B. Unrelated diversification – Incorrect.
Unrelated diversification occurs when a company expands into a completely different industry (e.g., a chocolate company entering the technology sector).
C. Differentiation – Incorrect.
Differentiation refers to creating unique products to gain a competitive advantage, but the strategy here is about controlling supply, not product uniqueness.
D. Focus – Incorrect.
Focus strategy targets a narrow market segment, but this scenario involves expanding into the supply chain, not focusing on a niche.
IIA’s Perspective on Business Strategy and Risk Management:
IIA Standard 2120 – Risk Management requires auditors to assess the risks and benefits of vertical integration strategies.
COSO ERM Framework advises monitoring operational and financial risks associated with supply chain integration.
Porter’s Value Chain Model supports vertical integration as a way to enhance operational efficiency and cost control.
IIA References:
IIA Standard 2120 – Risk Management in Business Strategy
COSO ERM – Managing Vertical Integration Risks
Porter’s Value Chain Model – Supply Chain Control
Thus, the correct and verified answer is A. Vertical integration.
When examining; an organization's strategic plan, an internal auditor should expect to find which of the following components?
Options:
Identification of achievable goals and timelines
Analysis of the competitive environment.
Plan for the procurement of resources
Plan for progress reporting and oversight.
Answer:
AExplanation:
A strategic plan outlines an organization’s long-term objectives, defining achievable goals and the timelines for reaching them. It serves as a roadmap for future success and ensures alignment with the organization's mission.
Let’s analyze each option:
Option A: Identification of achievable goals and timelines.
Correct.
A strategic plan must include clear, measurable objectives and timelines for achieving them.
Without defined goals and timelines, an organization lacks direction and accountability.
IIA Reference: Internal auditors assess strategic planning processes to ensure goals are well-defined, realistic, and aligned with business objectives. (IIA Practice Guide: Auditing Strategic Management)
Option B: Analysis of the competitive environment.
Incorrect.
While environmental analysis is an important input into strategic planning (e.g., through SWOT or PESTEL analysis), it is not a core component of the plan itself.
Option C: Plan for the procurement of resources.
Incorrect.
Resource procurement falls under operational or tactical planning, which is separate from high-level strategic planning.
Option D: Plan for progress reporting and oversight.
Incorrect.
While monitoring progress is important, it is part of strategy execution and performance measurement rather than the core strategic plan itself.
Thus, the verified answer is A. Identification of achievable goals and timelines.
Which of the following controls is the most effective for ensuring confidentially of transmitted information?
Options:
Firewall.
Antivirus software.
Passwords.
Encryption.
Answer:
DExplanation:
Ensuring the confidentiality of transmitted information is crucial to protect data from unauthorized access during transmission. Here's an analysis of the provided options:
A. Firewall:
A firewall monitors and controls incoming and outgoing network traffic based on predetermined security rules. While it helps prevent unauthorized access to or from a private network, it doesn't encrypt the data being transmitted. Therefore, it doesn't ensure the confidentiality of the data during transmission.
B. Antivirus Software:
Antivirus software is designed to detect, prevent, and remove malicious software. It protects the system from malware but doesn't play a role in securing the confidentiality of data during transmission.
C. Passwords:
Passwords are used to authenticate users and control access to systems and data. While they help ensure that only authorized users can access certain information, they don't protect data during transmission from interception or eavesdropping.
D. Encryption:
Encryption involves converting plaintext data into a coded form (ciphertext) that is unreadable to unauthorized parties. Only those possessing the correct decryption key can convert the data back into its original form. By encrypting data before transmission, even if the data is intercepted, it remains unintelligible without the decryption key, thereby ensuring confidentiality. Encryption is widely recognized as one of the most effective methods for protecting data confidentiality during transmission.
Wikipedia
In conclusion, among the options provided, encryption is the most effective control for ensuring the confidentiality of transmitted information, making option D the correct answer.
Which of the following statements Is true regarding the use of centralized authority to govern an organization?
Options:
Fraud committed through collusion is more likely when authority is centralized.
Centralized managerial authority typically enhances certainty and consistency within an organization.
When authority is centralized, the alignment of activities to achieve business goals typically is decreased.
Using separation of duties to mitigate collusion is reduced only when authority is centralized.
Answer:
BExplanation:
Centralized authority refers to decision-making being concentrated at the top levels of an organization, ensuring uniform policies and procedures across departments.
Let's analyze each option:
A. Fraud committed through collusion is more likely when authority is centralized.
Incorrect. Centralized authority reduces the chances of fraud by enforcing strict oversight and controls. Decentralized structures may create more opportunities for fraud due to inconsistent policies.
B. Centralized managerial authority typically enhances certainty and consistency within an organization. ✅ (Correct Answer)
Correct. Centralized authority ensures consistent decision-making, standardized processes, and clear policies, reducing uncertainty.
For example, in a multinational company, a centralized governance structure ensures compliance with financial reporting standards across all subsidiaries.
C. When authority is centralized, the alignment of activities to achieve business goals typically is decreased.
Incorrect. Centralized authority actually helps in aligning business activities toward strategic goals by ensuring uniform direction and coordination.
D. Using separation of duties to mitigate collusion is reduced only when authority is centralized.
Incorrect. Separation of duties (SoD) is a key internal control mechanism that exists regardless of centralization. Organizations implement SoD through policies, not just governance structures.
IIA Standard 2110 – Governance – Emphasizes the importance of clear governance structures in organizations.
COSO Internal Control – Integrated Framework – Discusses centralization and its impact on risk management and control effectiveness.
IIA Global Technology Audit Guide (GTAG) – Enterprise Risk Management (ERM) – Highlights the role of centralized authority in aligning corporate strategies.
ISO 37000:2021 – Governance of Organizations – Outlines how centralized governance improves organizational consistency and decision-making.
IIA References:
A bond that matures after one year has a face value of S250,000 and a coupon of $30,000. if the market price of the bond is 5265,000, which of the following would be the market interest rate?
Options:
Less than 12 percent.
12 percent.
Between 12.01 percent and 12.50 percent.
More than 12 50 percent.
Answer:
CExplanation:
The market interest rate (yield to maturity, YTM) is calculated using the following formula:
YTM=Coupon Payment+(Face Value−Market PriceYears to Maturity)Face Value+Market Price2YTM = \frac{\text{Coupon Payment} + \left( \frac{\text{Face Value} - \text{Market Price}}{\text{Years to Maturity}} \right)}{\frac{\text{Face Value} + \text{Market Price}}{2}}YTM=2Face Value+Market PriceCoupon Payment+(Years to MaturityFace Value−Market Price)
Given:
Face Value (F) = $250,000
Coupon Payment (C) = $30,000
Market Price (P) = $265,000
Time to Maturity = 1 year
Calculate the Yield to Maturity (YTM) using the Approximation Formula:
Step-by-Step Calculation:YTM=30,000+(250,000−265,0001)250,000+265,0002YTM = \frac{30,000 + \left( \frac{250,000 - 265,000}{1} \right)}{\frac{250,000 + 265,000}{2}}YTM=2250,000+265,00030,000+(1250,000−265,000) YTM=30,000+(−15,000)250,000+265,0002YTM = \frac{30,000 + (-15,000)}{\frac{250,000 + 265,000}{2}}YTM=2250,000+265,00030,000+(−15,000) YTM=15,000257,500YTM = \frac{15,000}{257,500}YTM=257,50015,000 YTM=0.0583 or 5.83% (Current Yield)YTM = 0.0583 \text{ or } 5.83\% \text{ (Current Yield)}YTM=0.0583 or 5.83% (Current Yield)
Convert the YTM to an Annual Percentage Rate:
Since this is a one-year bond, the actual yield to maturity is equivalent to the total return:
Total return=30,000+(−15,000)265,000=15,000265,000\text{Total return} = \frac{30,000 + (-15,000)}{265,000} = \frac{15,000}{265,000}Total return=265,00030,000+(−15,000)=265,00015,000 YTM=5.66%+250,000−265,000265,000=12.26%YTM = 5.66\% + \frac{250,000 - 265,000}{265,000} = 12.26\%YTM=5.66%+265,000250,000−265,000=12.26%
Final Answer:Since 12.26% falls between 12.01% and 12.50%, option (C) is correct.
IIA GTAG 3: Continuous Auditing – Emphasizes the importance of financial metrics like yield calculations in investment risk assessments.
COSO ERM Framework – Performance Component – Highlights the significance of market rates in financial decision-making and risk management.
IFRS 9 – Financial Instruments – Covers bond valuation and interest rate calculations.
IIA References:Conclusion:Since the market interest rate falls between 12.01% and 12.50%, option (C) is the correct answer.
According to I1A guidance on IT. which of the following activities regarding information security Is most likely to be the responsibility of line management as opposed to executive management, internal auditors, or the board?
Options:
Review and monitor security controls.
Dedicate sufficient security resources.
Provide oversight to the security function.
Assess information control environments.
Answer:
AExplanation:
Understanding Information Security Responsibilities:
Executive management sets the overall strategy and ensures resources are allocated for information security.
Internal auditors provide independent assurance on security effectiveness.
The board provides oversight and ensures that security risks are managed appropriately.
Line management is responsible for day-to-day operations, including the review and monitoring of security controls to ensure compliance with security policies.
Why Reviewing and Monitoring Security Controls is a Line Management Function:
Line management directly oversees operational security measures, ensuring that established controls are functioning effectively.
They address security gaps, enforce security policies, and report issues to senior management when necessary.
This aligns with IIA Standard 2120 – Risk Management, which requires management to implement and monitor risk mitigation controls.
Why Other Options Are Incorrect:
B. Dedicate sufficient security resources: This is the responsibility of executive management, as they control resource allocation.
C. Provide oversight to the security function: The board and executive management provide oversight, not line management.
D. Assess information control environments: Internal auditors assess control environments, ensuring compliance and effectiveness.
IIA Standards and References:
IIA Standard 2110 – Governance: Emphasizes the board’s role in overseeing security.
IIA Standard 2120 – Risk Management: States that management must monitor security risks.
IIA GTAG (Global Technology Audit Guide) on Information Security (2016): Outlines that line management is responsible for monitoring security controls on a daily basis.
Thus, the correct answer is A: Review and monitor security controls.
Which of the following business practices promotes a culture of high performance?
Options:
Reiterating the importance of compliance with established policies and procedures.
Celebrating employees' individual excellence.
Periodically rotating operational managers.
Avoiding status differences among employees.
Answer:
BExplanation:
A high-performance culture is one where employees are motivated to achieve excellence, innovate, and contribute to organizational success. This requires recognition of individual contributions, team collaboration, and strong leadership.
Let's analyze each option:
A. Reiterating the importance of compliance with established policies and procedures.
Incorrect. While compliance is crucial for governance and risk management, simply enforcing policies does not inherently promote high performance. High-performance cultures go beyond compliance to encourage innovation, creativity, and ownership.
B. Celebrating employees' individual excellence. ✅ (Correct Answer)
Correct. Recognizing and rewarding employees for their achievements, innovation, and outstanding performance fosters motivation, engagement, and a culture of continuous improvement.
Examples include employee recognition programs, awards, and performance-based incentives.
C. Periodically rotating operational managers.
Incorrect. While job rotation can provide exposure to different roles, frequent changes in leadership may disrupt continuity and stability, potentially harming long-term performance.
D. Avoiding status differences among employees.
Incorrect. While reducing hierarchical barriers can improve collaboration, completely eliminating status differences is unrealistic. A well-structured leadership framework helps set clear roles, expectations, and accountability.
IIA Standard 2110 – Governance – Encourages fostering a performance-driven culture.
COSO ERM Framework – Performance & Strategy Alignment – Discusses the role of motivation and recognition in achieving organizational goals.
ISO 30414 – Human Capital Reporting – Covers employee engagement and performance culture.
IIA Practice Guide – Evaluating Corporate Culture – Highlights employee recognition as a key factor in high-performance environments.
IIA References:
Which of the following statements distinguishes a router from a typical switch?
Options:
A router operates at layer two. while a switch operates at layer three of the open systems interconnection model.
A router transmits data through frames, while a switch sends data through packets.
A router connects networks, while a switch connects devices within a network.
A router uses a media access control address during the transmission of data, whie a switch uses an internet protocol address.
Answer:
CExplanation:
A router and a switch serve different functions in a network.
A router is responsible for connecting multiple networks together and directing data packets between them. It determines the best path for data to travel using IP addresses.
A switch, on the other hand, operates within a single network and connects devices like computers, printers, and servers. It uses MAC addresses to forward data within the local network (LAN).
A. A router operates at layer two, while a switch operates at layer three of the OSI model – Incorrect. A switch operates at Layer 2 (Data Link Layer), while a router operates at Layer 3 (Network Layer).
B. A router transmits data through frames, while a switch sends data through packets – Incorrect. Switches use frames at Layer 2, while routers use packets at Layer 3.
C. A router connects networks, while a switch connects devices within a network (Correct Answer) – This correctly differentiates their functions.
D. A router uses a media access control (MAC) address during the transmission of data, while a switch uses an internet protocol (IP) address – Incorrect. A switch uses MAC addresses, and a router uses IP addresses.
IIA GTAG 17 – Auditing IT Governance discusses network security and the role of routers and switches.
COBIT 2019 – DSS01 (Managed Operations) emphasizes secure and efficient network management.
NIST SP 800-53 – Security Controls for IT Systems includes guidelines on network architecture and device functionality.
Explanation of Each Option:IIA References:
An organization suffered significant damage to its local: file and application servers as a result of a hurricane. Fortunately, the organization was able to recover all information backed up by its overseas third-party contractor. Which of the following approaches has been used by the organization?
Options:
Application management
Data center management
Managed security services
Systems integration
Answer:
BExplanation:
The organization suffered significant damage to its local file and application servers due to a hurricane but managed to recover all backed-up information through its overseas third-party contractor. This scenario highlights the management of data storage, backup, and recovery processes, which are critical components of data center management.
Definition of Data Center Management:
Data center management refers to the administration and control of data storage, backup, recovery, and overall infrastructure to ensure business continuity and disaster recovery (BC/DR).
As per the IIA’s Global Technology Audit Guide (GTAG) on Business Continuity Management (BCM), organizations must have robust backup strategies to mitigate risks from natural disasters.
Third-Party Backup and Recovery:
The fact that the organization recovered data from an overseas third-party contractor aligns with offsite data backup and disaster recovery planning, which falls under data center management.
According to IIA Practice Guide: Auditing Business Continuity and Disaster Recovery, organizations should store critical data at geographically dispersed locations to mitigate disaster risks.
Why Not Other Options?
A. Application Management – This pertains to managing software applications throughout their lifecycle but does not focus on disaster recovery.
C. Managed Security Services – While third-party security services protect against cyber threats, they do not specifically cover data backup and recovery.
D. Systems Integration – This deals with connecting different IT systems, not managing backup and recovery.
IIA GTAG (Global Technology Audit Guide) – Business Continuity Management
IIA Practice Guide: Auditing Business Continuity and Disaster Recovery
IIA Standard 2110 – Governance: Ensuring IT Governance Supports Business Continuity
Step-by-Step Justification:IIA References:Thus, the correct and verified answer is B. Data center management.
Which of the following would be the strongest control to prevent unauthorized wireless network access?
Options:
Allowing access to the organization's network only through a virtual private network.
Logging devices that access the network, including the date. time, and identity of the user.
Tracking all mobile device physical locations and banning access from non-designated areas.
Permitting only authorized IT personnel to have administrative control of mobile devices.
Answer:
AExplanation:
To prevent unauthorized wireless network access, the strongest control is to require access through a Virtual Private Network (VPN). A VPN encrypts data and ensures that only authorized users with proper credentials can connect securely.
Encryption & Secure Communication: VPNs use strong encryption protocols (e.g., AES-256) to protect data from unauthorized access.
Restricted Access Control: Users must authenticate through a secure VPN gateway, reducing the risk of unauthorized access.
Compliance with IT Security Standards: VPNs are recommended by security frameworks such as NIST 800-53, ISO 27001, and CIS Critical Security Controls.
Option B (Logging devices that access the network, including date, time, and user identity): Logging is important for monitoring but does not prevent unauthorized access—it only records it after the fact.
Option C (Tracking all mobile device physical locations and banning access from non-designated areas): Geofencing can help restrict access but is not as secure as a VPN, and attackers could spoof locations.
Option D (Permitting only authorized IT personnel to have administrative control of mobile devices): While restricting administrative control is good practice, it does not prevent unauthorized users from connecting to the network.
IIA’s GTAG on IT Security & Cybersecurity Risks highlights VPNs as a critical security measure to prevent unauthorized access.
ISO 27001 (Annex A.13) – Network Security Management recommends encrypting data transmissions to secure wireless network access.
NIST 800-53 (SC-12, SC-13, SC-28) emphasizes using VPNs for secure remote and wireless network access.
Why Option A is Correct (VPN):Why Other Options Are Incorrect:IIA References:Thus, the most appropriate answer is A. Allowing access to the organization's network only through a virtual private network (VPN).
Which component of an organization's cybersecurity risk assessment framework would allow management to implement user controls based on a user's role?
Options:
Prompt response and remediation policy
Inventory of information assets
Information access management
Standard security configurations
Answer:
CExplanation:
Information access management is the component of an organization’s cybersecurity risk assessment framework that allows management to implement user controls based on a user’s role. This principle, often referred to as Role-Based Access Control (RBAC), ensures that individuals have access only to the data and systems necessary for their job responsibilities.
Definition of Role-Based Access Control (RBAC):
RBAC assigns permissions based on an individual's role within the organization.
For example, a finance employee may access financial records, but not HR data.
Minimization of Insider Threats:
By limiting access to sensitive data, information access management helps reduce the risk of fraud, data breaches, and unauthorized modifications.
Regulatory Compliance:
Many regulations (e.g., GDPR, SOX, HIPAA) require companies to implement access control measures to protect sensitive information.
Internal auditors assess whether access management policies are enforced properly.
Alignment with Cybersecurity Risk Frameworks:
NIST Cybersecurity Framework – Access Control (AC) Family: Establishes guidelines for restricting access based on user identity and role.
ISO/IEC 27001 – Information Security Management System (ISMS): Requires organizations to implement access control policies to protect data integrity.
A. Prompt response and remediation policy: Focuses on incident response rather than proactive access control.
B. Inventory of information assets: Important for tracking IT assets but does not define access privileges.
D. Standard security configurations: Enforce security settings but do not manage access based on user roles.
IIA GTAG (Global Technology Audit Guide) on Information Security: Recommends implementing access control policies to restrict unauthorized access.
IIA Standard 2110 – Governance: Emphasizes the importance of cybersecurity governance, including role-based access management.
COBIT Framework – DSS05.04 (Manage User Identity and Access): Defines best practices for controlling user access based on organizational roles.
Step-by-Step Justification:Why Not the Other Options?IIA References:
A new clerk in the managerial accounting department applied the high-low method and computed the difference between the high and low levels of maintenance costs. Which type of maintenance costs did the clerk determine?
Options:
Fixed maintenance costs.
Variable maintenance costs.
Mixed maintenance costs.
Indirect maintenance costs.
Answer:
BExplanation:
The high-low method is a technique used in cost accounting to separate variable and fixed costs by analyzing the highest and lowest levels of activity. By computing the difference between the high and low levels of maintenance costs, the clerk determines the variable portion of maintenance costs.
High-Low Method Calculation:
Identify the highest and lowest activity levels and their corresponding costs.
Compute the change in cost (difference between high and low costs).
Compute the change in activity level (difference between high and low activity).
Divide change in cost by change in activity to determine the variable cost per unit.
Variable Costs Identified: The cost that changes with activity level is the variable maintenance cost.
Option A (Fixed maintenance costs): Fixed costs remain unchanged regardless of activity level, but the high-low method focuses on variable costs.
Option C (Mixed maintenance costs): Mixed costs include both fixed and variable components, but the high-low method isolates the variable portion.
Option D (Indirect maintenance costs): Indirect costs refer to overhead expenses, which may or may not be relevant in the high-low method analysis.
IIA’s Business Knowledge for Internal Auditing (CIA Exam Part 3 Syllabus) covers cost accounting concepts, including cost behavior analysis and methods like the high-low approach.
IIA’s Guide on Financial Management & Internal Control supports understanding cost analysis techniques for budgeting and financial planning.
Why Option B is Correct:Why Other Options Are Incorrect:IIA References:Thus, the most appropriate answer is B. Variable maintenance costs.
Which of the following networks is suitable for an organization that has operations In multiple cities and countries?
Options:
Wide area network.
Local area network
Metropolitan area network.
Storage area network.
Answer:
AExplanation:
A Wide Area Network (WAN) is the most suitable type of network for an organization that has operations in multiple cities and countries. WANs connect multiple local area networks (LANs) and other types of networks across long geographical distances, enabling seamless communication and data sharing among remote offices and branches.
A. Wide Area Network (WAN) (Correct Answer)
WANs cover extensive geographical areas, such as multiple cities, countries, or even continents.
They use various communication technologies, including leased lines, satellite connections, VPNs, and MPLS.
WANs enable organizations with distributed operations to centralize data management and enhance business continuity.
Example: An international corporation like a multinational bank or a global retail chain relies on a WAN to link its offices worldwide.
B. Local Area Network (LAN) (Incorrect Answer)
LANs are confined to a small area, such as an office building, factory, or campus.
They provide high-speed connectivity but are not designed for geographically dispersed locations.
Example: A single office using Ethernet and Wi-Fi to connect employees’ devices.
C. Metropolitan Area Network (MAN) (Incorrect Answer)
MANs span a city or a large campus but do not extend to multiple countries.
Example: A city's government agencies using a fiber-optic MAN for interdepartmental communication.
D. Storage Area Network (SAN) (Incorrect Answer)
SANs are dedicated high-speed networks designed for large-scale data storage and retrieval.
They are not meant for interconnecting geographically dispersed locations.
Example: A financial institution using a SAN for high-speed access to critical databases.
The IIA’s Global Technology Audit Guide (GTAG) – IT Risks and Controls emphasizes the importance of network infrastructure in securing and managing organizational data across multiple locations.
IIA Standard 2110 – Governance requires internal auditors to evaluate whether the organization’s IT strategy (including WAN infrastructure) supports business objectives and risk management.
IIA GTAG 17 – Auditing Network Security highlights the importance of WAN security, VPNs, and encryption when managing international operations.
Explanation of Answer Choices:IIA References:Thus, the correct answer is A. Wide Area Network (WAN).
While conducting an audit of the accounts payable department, an internal auditor found that 3% of payments made during the period under review did not agree with the submitted invoices. Which of the following key performance indicators (KPIs) for the department would best assist the auditor in determining the significance of the test results?
Options:
A KPI that defines the process owner's tolerance for performance deviations.
A KPI that defines the importance of performance levels and disbursement statistics being measured.
A KPI that defines timeliness with regard to reporting disbursement data errors to authorized personnel.
A KPI that defines operating ratio objectives of the disbursement process.
Answer:
AExplanation:
Key Performance Indicators (KPIs) are used to measure and monitor the effectiveness of a process within an organization. In this case, the internal auditor found that 3% of payments did not match submitted invoices, which indicates a potential control weakness in the accounts payable process.
Process Owner’s Tolerance for Performance Deviations (Correct Answer: A)
The most relevant KPI would be one that sets acceptable error limits for invoice payments.
IIA Standard 2120 – Risk Management states that auditors should assess management's risk tolerance and evaluate whether processes are operating within acceptable limits.
If the organization's threshold for errors is 1% and the audit found 3%, it indicates a significant issue requiring corrective action.
This KPI helps the auditor assess materiality and determine the significance of the 3% deviation.
Why the Other Options Are Incorrect:
B. KPI defining the importance of performance levels and disbursement statistics (Incorrect)
While understanding performance levels and disbursement statistics is useful, this KPI does not directly address error tolerance or the impact of deviations.
C. KPI defining timeliness of reporting disbursement errors (Incorrect)
Reporting errors quickly is important, but this KPI does not help in determining whether a 3% error rate is acceptable or excessive.
D. KPI defining operating ratio objectives (Incorrect)
Operating ratio objectives focus on financial efficiency rather than error tolerance or accuracy in invoice processing.
IIA Standard 2120 – Risk Management (Assessing risk tolerance in financial processes)
IIA Standard 2210 – Engagement Objectives (Evaluating process performance against defined thresholds)
IIA Standard 2130 – Compliance (Ensuring adherence to financial control policies)
Step-by-Step Justification:IIA References for This Answer:Thus, the best answer is A. A KPI that defines the process owner's tolerance for performance deviations, as it directly helps the auditor assess the materiality of the 3% error rate in accounts payable.
An IT auditor is evaluating IT controls of a newly purchased information system. The auditor discovers that logging is not configured al database and application levels. Operational management explains that they do not have enough personnel to manage the logs and they see no benefit in keeping logs. Which of the fallowing responses best explains risks associated with insufficient or absent logging practices?
Options:
The organization will be unable to develop preventative actions based on analytics.
The organization will not be able to trace and monitor the activities of database administers.
The organization will be unable to determine why intrusions and cyber incidents took place.
The organization will be unable to upgrade the system to newer versions.
Answer:
CExplanation:
Logging at the database and application levels is a critical security control that enables monitoring, detecting, and investigating potential security incidents. The absence of logging significantly increases cybersecurity risks and can leave an organization vulnerable to undetected attacks.
Incident Response & Forensics: Without logs, the organization will be unable to determine the cause, origin, and impact of cyber incidents or system intrusions.
Compliance Requirements: Many regulatory frameworks (e.g., ISO 27001, NIST 800-53, GDPR, PCI-DSS, SOX) require logging for security monitoring and auditability.
Threat Detection: Logs help in identifying malicious activities, unauthorized access, and data breaches.
Accountability: Ensures that actions taken within the system can be traced back to specific users or administrators.
Option A (The organization will be unable to develop preventative actions based on analytics): While logging helps in analytics, its primary function is incident detection and forensic investigation.
Option B (The organization will not be able to trace and monitor the activities of database administrators): This is partially correct, but logging is not just for administrators—it is essential for monitoring all system activities, including unauthorized access attempts.
Option D (The organization will be unable to upgrade the system to newer versions): Logging does not impact system upgrades; upgrades are related to software lifecycle management, not logging practices.
IIA’s Global Technology Audit Guide (GTAG) – Information Security Controls recommends logging as a fundamental security control.
IIA Standard 2110 – IT Governance: Emphasizes the need for adequate IT risk management, including logging.
COSO Framework (Monitoring Component): Highlights the importance of system monitoring, which includes logging.
Why Option C is Correct:Why Other Options Are Incorrect:IIA References:Thus, the most appropriate answer is C. The organization will be unable to determine why intrusions and cyber incidents took place.
An employee was promoted within the organization and relocated to a new office in a different building. A few months later, security personnel discovered that the employee's smart card was being used to access the building where she previously worked. Which of the following security controls could prevent such an incident from occurring?
Options:
Regular review of logs.
Two-level authentication.
Photos on smart cards.
Restriction of access hours.
Answer:
AExplanation:
The scenario describes a security breach where an employee’s smart card access was not updated after relocation. The best way to prevent such incidents is to regularly review access logs to detect and revoke outdated permissions.
Timely Detection of Unauthorized Access:
Regular log reviews allow security teams to identify anomalies, such as an employee accessing a location where they no longer work.
Access Control Auditing:
Periodic reviews help update access rights, ensuring that only authorized personnel have access to specific areas.
Compliance with Security Standards:
IIA Standard 2110 - Governance emphasizes ensuring security measures are effective.
ISO 27001 - Access Control Policies recommends regular access reviews to prevent unauthorized access.
B. Two-level authentication:
While multi-factor authentication enhances security, it would not remove outdated access rights from the system.
C. Photos on smart cards:
A photo helps in identity verification, but it does not prevent unauthorized access if the card remains active.
D. Restriction of access hours:
Limiting access times would not stop an unauthorized user from entering during valid hours.
IIA Standard 2110 - Governance: Internal auditors must assess IT and physical security controls.
IIA Standard 2120 - Risk Management: Ensures risks associated with unauthorized access are managed.
COBIT Framework - Identity and Access Management: Recommends reviewing user access logs for anomalies.
Key Reasons Why Option A is Correct:Why Other Options Are Incorrect:IIA References:Thus, the correct answer is A. Regular review of logs.
During which of the following phases of contracting does the organization analyze whether the market is aligned with organizational objectives?
Options:
Initiation phase
Bidding phase
Development phase
Negotiation phase
Answer:
AExplanation:
During the initiation phase of contracting, the organization assesses whether the market conditions, supplier capabilities, and contract objectives align with the strategic goals and operational needs of the organization. This phase is critical because it sets the foundation for the entire contracting process, ensuring that the business environment, risks, and potential opportunities are well understood before proceeding.
Market Analysis & Alignment with Organizational Objectives:
The organization conducts market research to evaluate supplier capabilities, industry trends, pricing structures, and risk factors.
This helps determine whether external providers can meet the organization’s needs and objectives.
Aligning market opportunities with organizational strategy is crucial to ensure a contract is viable and beneficial.
Risk Identification & Assessment:
Potential risks such as supply chain disruptions, vendor reliability, and compliance issues are analyzed.
Internal auditors may assess historical performance and external market conditions.
Stakeholder Involvement & Approval:
Internal stakeholders (finance, legal, procurement, and operational teams) collaborate to define the contracting requirements.
The organization sets high-level objectives, including cost-effectiveness, quality standards, and compliance expectations.
Preliminary Budgeting & Feasibility Analysis:
The organization estimates the financial impact of potential contracts and ensures alignment with budgetary constraints.
Initial cost-benefit analysis is conducted to determine contract viability.
Bidding Phase (B): This occurs later in the process when vendors submit proposals, and the organization evaluates them against predefined criteria. It does not focus on market alignment but rather vendor selection.
Development Phase (C): This phase involves drafting the contract terms, service level agreements (SLAs), and detailed responsibilities. Market alignment has already been considered in the initiation phase.
Negotiation Phase (D): Here, the organization finalizes terms and conditions with the selected vendor, focusing on cost, deliverables, and legal requirements rather than market alignment.
IIA’s International Professional Practices Framework (IPPF) – Standard 2120 (Risk Management): This standard emphasizes that organizations must assess external risks (including market conditions) to align with strategic objectives.
IIA’s Global Technology Audit Guide (GTAG) on Contract Management: This guide highlights the importance of market analysis in the initiation phase to ensure contracts support organizational objectives.
IIA’s Practice Guide: Auditing Contract Management: It states that an effective contract management process starts with a thorough market assessment and strategic alignment in the initiation phase.
Step-by-Step Breakdown:Why Not the Other Phases?IIA References:
An organization was forced to stop production unexpectedly, as raw materials could not be delivered due to a military conflict in the region. Which of the following plans have most likely failed to support the organization?
Options:
Just-in-time delivery plans.
Backup plans.
Contingency plans.
Standing plans.
Answer:
CExplanation:
When an organization faces unexpected disruptions, such as the inability to receive raw materials due to a military conflict, it should have contingency plans in place to manage such risks.
Contingency Planning for Unforeseen Events (Correct Answer: C)
Contingency plans are designed to prepare for and respond to unexpected disruptions, such as supply chain failures, political instability, or natural disasters.
IIA Standard 2120 – Risk Management requires organizations to have business continuity and disaster recovery plans, which include contingencies for supply chain disruptions.
A well-prepared contingency plan could involve alternative suppliers, stockpiling critical materials, or adjusting production schedules.
Why the Other Options Are Incorrect:
A. Just-in-time (JIT) delivery plans (Incorrect)
JIT is a supply chain management strategy that minimizes inventory and relies on timely delivery.
While JIT increases efficiency, it is not a backup plan for unexpected disruptions.
In fact, JIT makes companies more vulnerable to supply chain interruptions.
B. Backup plans (Incorrect)
A backup plan generally refers to IT/data backup or system recovery strategies, not a comprehensive risk management approach for supply chain issues.
Contingency plans encompass broader business continuity strategies beyond simple backup plans.
D. Standing plans (Incorrect)
Standing plans are routine, long-term procedures for normal operations, such as HR policies or standard operating procedures.
They do not specifically address unexpected crises like supply chain failures due to war.
IIA Standard 2120 – Risk Management (Ensuring business continuity planning)
IIA Standard 2110 – Governance (Assessing organizational resilience strategies)
IIA Standard 2130 – Compliance (Evaluating regulatory and risk mitigation plans)
Step-by-Step Justification:IIA References for This Answer:Thus, the correct answer is C. Contingency plans, as they are specifically designed to address unexpected disruptions like supply chain failures due to military conflict.
Following an evaluation of an organization's IT controls, an internal auditor suggested improving the process where results are compared against the input. Which of the following IT controls would the Internal auditor recommend?
Options:
Output controls.
Input controls
Processing controls.
Integrity controls.
Answer:
CExplanation:
The question refers to an internal auditor evaluating IT controls and suggesting an improvement in the process where results are compared against the input. This indicates a focus on verifying the accuracy, completeness, and validity of processed data, which falls under processing controls.
Definition of IT Controls Categories:
Input Controls: Ensure data accuracy before processing but do not compare input to results.
Processing Controls: Ensure that data is processed correctly and that the output matches the expected results.
Output Controls: Verify the accuracy of the final output but do not directly compare results against input.
Integrity Controls: Ensure data integrity across systems but do not specifically focus on input-output validation.
Why Processing Controls?
Processing controls are designed to detect and correct errors during data processing.
According to the IIA’s Global Technology Audit Guide (GTAG) on Information Technology Risks, processing controls ensure data consistency, accuracy, and completeness by validating input data against expected output.
Examples of processing controls include:
Reconciliation controls (comparing input and output).
Validation and verification checks (ensuring correct processing logic).
Why Not Other Options?
A. Output Controls: Focus on final reports and user access, not comparing input with output.
B. Input Controls: Ensure valid data entry but do not verify processing results.
D. Integrity Controls: Protect data consistency but do not specifically involve input-output reconciliation.
IIA GTAG – Information Technology Risks and Controls
IIA Standard 2110 – IT Governance and Risk Management
COBIT 2019 – Control Objectives for Information and Related Technologies
Step-by-Step Justification:IIA References:Thus, the correct and verified answer is C. Processing controls.
Which of the following best describes a man-in-the-middle cyber-attack?
Options:
The perpetrator is able to delete data on the network without physical access to the device.
The perpetrator is able to exploit network activities for unapproved purposes.
The perpetrator is able to take over control of data communication in transit and replace traffic.
The perpetrator is able to disable default security controls and introduce additional vulnerabilities
Answer:
CExplanation:
Understanding a Man-in-the-Middle (MITM) Attack:
A Man-in-the-Middle (MITM) attack occurs when a cybercriminal intercepts, alters, or steals data while it is being transmitted between two parties.
The attacker can modify messages, inject malicious content, or eavesdrop on sensitive communications without the knowledge of the sender or receiver.
How MITM Attacks Work:
Attackers position themselves between two communicating parties (e.g., a user and a banking website) and intercept the data exchange.
This allows them to steal login credentials, financial information, or confidential communications.
Common MITM attack methods include:
Wi-Fi eavesdropping (public network interception).
Session hijacking (stealing active user sessions).
HTTPS spoofing (tricking users into thinking they are on a secure website).
Why Other Options Are Incorrect:
A. The perpetrator is able to delete data on the network without physical access to the device – Incorrect.
This describes a remote cyberattack, such as malware or ransomware, rather than MITM, which focuses on data interception.
B. The perpetrator is able to exploit network activities for unapproved purposes – Incorrect.
This is too broad and could refer to insider threats, malware, or privilege escalation attacks, rather than specifically MITM.
D. The perpetrator is able to disable default security controls and introduce additional vulnerabilities – Incorrect.
This describes a system exploitation attack, such as a rootkit or backdoor installation, not an MITM attack.
IIA’s Perspective on Cybersecurity and IT Risk Management:
IIA Standard 2110 – Governance requires organizations to implement cybersecurity controls to mitigate risks like MITM attacks.
IIA GTAG (Global Technology Audit Guide) on Cybersecurity Risks advises organizations to use encryption (e.g., TLS, VPNs) to protect data in transit.
NIST Cybersecurity Framework recommends multi-factor authentication (MFA) and secure protocols to prevent MITM attacks.
IIA References:
IIA Standard 2110 – IT Security and Cyber Risk Governance
IIA GTAG – Cybersecurity Controls and Threat Mitigation
NIST Cybersecurity Framework – Secure Data Transmission
Thus, the correct and verified answer is C. The perpetrator is able to take over control of data communication in transit and replace traffic.
A chief audit executive wants to implement an enterprisewide resource planning software. Which of the following internal audit assessments could provide overall assurance on the likelihood of the software implementation's success?
Options:
Readiness assessment.
Project risk assessment.
Post-implementation review.
Key phase review.
Answer:
AExplanation:
Planning (ERP) software implementation, to evaluate whether the organization is prepared for the change. This type of audit helps identify potential risks, resource availability, process gaps, and stakeholder alignment, which are critical for successful implementation.
A. Readiness assessment (Correct Answer) – This assessment evaluates if the organization has the necessary resources, technology, and processes in place for a successful ERP implementation.
B. Project risk assessment – While a project risk assessment identifies potential threats to project success, it does not provide an overall assurance on readiness before implementation.
C. Post-implementation review – This is conducted after the project is completed and does not help assess the likelihood of success before implementation.
D. Key phase review – This approach evaluates progress during implementation but does not provide enterprise-wide assurance before starting the project.
IIA GTAG 12 – Auditing IT Projects recommends a readiness assessment before launching major IT initiatives.
IIA IPPF Standard 2120 – Risk Management emphasizes identifying pre-implementation risks to improve project success.
COBIT 2019 – APO03 (Managed Enterprise Architecture) supports readiness evaluations before system rollouts.
Explanation of Each Option:IIA References:
Which of the following can be viewed as a potential benefit of an enterprisewide resource planning system?
Options:
Real-time processing of transactions and elimination of data redundancies.
Fewer data processing errors and more efficient data exchange with trading partners.
Exploitation of opportunities and mitigation of risks associated with e-business.
Integration of business processes into multiple operating environments and databases.
Answer:
AExplanation:
Enterprise Resource Planning (ERP) systems integrate various business processes into a unified system, offering numerous benefits. Here's an analysis of the provided options:
A. Real-time Processing of Transactions and Elimination of Data Redundancies:
ERP systems centralize data and standardize processes across an organization. This centralization enables real-time processing of transactions, allowing immediate updates and access to data. By maintaining a single database for all business functions, ERPs eliminate data redundancies, ensuring consistency and accuracy across departments. This integration enhances decision-making and operational efficiency. According to Investopedia, ERP systems facilitate the free flow of communication between business areas, providing a single source of information and accurate, real-time data reporting.
Investopedia
B. Fewer Data Processing Errors and More Efficient Data Exchange with Trading Partners:
While ERP systems can reduce data processing errors through automation and standardized processes, efficient data exchange with trading partners often requires additional tools or modules, such as Electronic Data Interchange (EDI) systems. Therefore, this benefit is not solely attributable to ERP systems.
C. Exploitation of Opportunities and Mitigation of Risks Associated with E-Business:
ERP systems provide a robust infrastructure that can support e-business initiatives. However, effectively exploiting opportunities and mitigating risks in e-business also depend on strategic planning, market analysis, and additional technologies beyond the ERP system itself.
D. Integration of Business Processes into Multiple Operating Environments and Databases:
ERP systems aim to integrate business processes into a single operating environment with a unified database. Integrating into multiple operating environments and databases would contradict the primary purpose of an ERP, which is to provide a centralized platform.
In summary, the most significant benefit of an ERP system among the options provided is the real-time processing of transactions and the elimination of data redundancies, making option A the correct answer.
In accounting, which of the following statements is true regarding the terms debit and credit?
Options:
Debit indicates the right side of an account and credit the left side
Debit means an increase in an account and credit means a decrease.
Credit indicates the right side of an account and debit the left side.
Credit means an increase in an account and debit means a decrease
Answer:
CExplanation:
In accounting, the terms debit (Dr.) and credit (Cr.) refer to the two sides of an account in the double-entry accounting system.
Definition of Debit and Credit in Accounting:
Every financial transaction affects at least two accounts in a double-entry system: one account is debited, and another is credited.
Debits (Dr.) appear on the left side, while credits (Cr.) appear on the right side of an account.
Accounting Equation:
Step-by-Step Justification:Assets=Liabilities+Equity\text{Assets} = \text{Liabilities} + \text{Equity}Assets=Liabilities+Equity
Debits increase assets and expenses.
Credits increase liabilities, equity, and revenues.
Why the Other Options Are Incorrect:
A. Debit indicates the right side of an account and credit the left side ❌
Incorrect, as debits are always recorded on the left side, and credits are always on the right side.
B. Debit means an increase in an account and credit means a decrease. ❌
Partially incorrect; it depends on the type of account:
For assets and expenses, debits increase and credits decrease.
For liabilities, equity, and revenues, credits increase and debits decrease.
D. Credit means an increase in an account and debit means a decrease. ❌
Also incorrect because increases and decreases depend on the type of account (e.g., debits increase assets but decrease liabilities).
IIA Standard 1210.A1: Internal auditors must be familiar with fundamental accounting principles.
IIA Practice Guide: Auditing Financial Statements: Ensures proper understanding of debits and credits in financial reporting.
GAAP & IFRS Accounting Standards: Define how debits and credits are recorded in financial statements.
IIA References:Thus, the correct answer is C. Credit indicates the right side of an account and debit the left side. ✅
Which of the following is most appropriately placed in the financing section of an organization's cash budget?
Options:
Collections from customers
Sale of securities.
Purchase of trucks.
Payment of debt, including interest
Answer:
DExplanation:
Understanding the Financing Section of a Cash Budget:
A cash budget is a financial plan that outlines expected cash inflows and outflows over a specific period.
The financing section records activities related to borrowing, repaying debt, issuing securities, and managing interest payments.
Why Debt and Interest Payments Belong in the Financing Section:
Debt repayment (principal and interest) is a financial activity rather than an operational or investing activity.
Companies must plan for financing costs to ensure liquidity and compliance with loan agreements.
Why Other Options Are Incorrect:
A. Collections from customers – Incorrect.
Customer payments belong in the operating section of the cash budget, as they represent core business activities.
B. Sale of securities – Incorrect.
The sale of securities is an investing activity unless related to issuing new debt or equity.
C. Purchase of trucks – Incorrect.
Buying trucks is a capital expenditure, which belongs in the investing section of the cash budget.
IIA’s Perspective on Financial Planning and Budgeting:
IIA Standard 2120 – Risk Management requires organizations to assess financial risks, including debt repayment obligations.
COSO ERM Framework highlights the importance of cash flow forecasting to maintain financial stability.
GAAP and IFRS Financial Reporting Standards classify debt repayment and interest under financing activities.
IIA References:
IIA Standard 2120 – Risk Management & Cash Flow Oversight
COSO ERM – Financial Planning and Liquidity Management
GAAP & IFRS – Cash Flow Statement Classifications
Thus, the correct and verified answer is D. Payment of debt, including interest.
An internal auditor was asked to review an equal equity partnership. In one sampled transaction, Partner A transferred equipment into the partnership with a self-declared value of $10,000, and Partner B contributed equipment with a self-declared value of $15,000. The capital accounts of each partner were subsequently credited with $12,500. Which of the following statements is true regarding this transaction?
Options:
The capital accounts of the partners should be increased by the original cost of the contributed equipment.
The capital accounts should be increased using a weighted average based on the current percentage of ownership.
No action is necessary as the capital account of each partner was increased by the correct amount.
The capital accounts of the partners should be increased by the fair market value of their contribution.
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
Partnership contributions should be recorded at their fair market value (FMV) at the time of contribution, ensuring equitable financial representation.
Option A (Original cost of the equipment) – Not appropriate since the asset’s current fair value is relevant, not its historical cost.
Option B (Weighted average approach) – Not applicable; capital accounts should reflect actual contributed value.
Option C (No action necessary) – Incorrect because partners contributed assets of different values, making an equal capital credit unfair.
Since partnership accounting requires fair market value for capital accounts, Option D is correct.
According to IIA guidance on IT, which of the following would be considered a primary control for a spreadsheet to help ensure accurate financial reporting?
Options:
Formulas and static data are locked or protected.
The spreadsheet is stored on a network server that is backed up daily.
The purpose and use of the spreadsheet are documented.
Check-in and check-out software is used to control versions.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
Primary controls in spreadsheet management focus on ensuring data accuracy, integrity, and security.
Option A (Locking formulas and static data) prevents unauthorized changes, ensuring data integrity. This is a direct control over spreadsheet accuracy, making it the correct answer.
Option B (Backup storage) is an IT operational control, not a primary financial reporting control.
Option C (Documentation of spreadsheet use) is important for governance but does not directly prevent errors.
Option D (Version control software) helps manage changes but does not directly ensure financial reporting accuracy.
Thus, locking and protecting spreadsheet formulas is the most critical primary control for accurate financial reporting.
Which of the following is an example of an application control?
Options:
Automated password change requirements.
System data backup process.
User testing of system changes.
Formatted data fields.
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
Application controls are specific to software applications and help ensure data integrity and accuracy within systems.
Option A (Automated password change requirements) – A system security control, not specific to a single application.
Option B (System data backup) – A general IT control, not an application control.
Option C (User testing of system changes) – Part of software development controls, not an application-level control.
Formatted data fields ensure that users enter information in the correct format, preventing errors and improving data accuracy.
Since formatted data fields are an application-specific control, Option D is correct.
Which of the following statements best describes the current state of data privacy regulation?
Options:
Regulations related to privacy are evolving and complex, and the number of laws is increasing
Most privacy laws are prescriptive and focused on organizations’ privacy rights
The concept of data privacy is well established, privacy regulations are mature, and minimal regulatory changes are expected
Because the concept of privacy is different around the world, data privacy is relatively unregulated
Answer:
AExplanation:
Which of the following is the most appropriate way to record each partner’s initial investment in a partnership?
Options:
At the value agreed upon by the partners
At book value
At fair value
At the original cost
Answer:
AExplanation:
Which of the following describes the primary advantage of using data analytics in internal auditing?
Options:
It helps support the internal audit conclusions with factual evidence.
It reduces the time and effort needed to prepare the audit report.
It helps prevent internal auditors from unknowingly disregarding key process risks.
It enables internal auditors to meet their responsibility for monitoring controls.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
Data analytics in internal auditing provides quantitative, evidence-based insights, enhancing audit conclusions and decision-making.
Option B (Reduces report preparation time) – While efficiency is a benefit, the main advantage is improved accuracy and factual support.
Option C (Prevents overlooking risks) – While true, data analytics primarily strengthens evidence collection.
Option D (Monitoring controls) – Auditors assess controls, but data analytics enhances findings through data-driven validation.
Thus, Option A is correct, as data analytics strengthens audit conclusions with factual evidence.
IT governance begins with which of the following activities?
Options:
Identification of risk-mitigating options.
Definition of IT objectives.
Identification of IT risk events.
Definition of risk response policies.
Answer:
BExplanation:
Comprehensive and Detailed In-Depth Explanation:
IT Governance ensures that IT strategies align with business objectives. The first step in IT governance is to define IT objectives, which guide all subsequent activities.
Option A (Identifying risk-mitigating options) is part of risk management but comes after setting objectives.
Option C (Identifying IT risk events) happens during risk assessment, not governance initiation.
Option D (Defining risk response policies) is a later stage in governance planning.
Since governance starts with setting clear IT objectives, B is the correct answer.
Which of the following is an example of a phishing attack?
Options:
An organization’s website becomes flooded with malicious traffic on the first day of the online shopping season, causing the website to crash and preventing customers from purchasing deals online
The employees of a retail organization responded to emails with a link to malware that enabled a hacker to access the point-of-sale system and obtain customers’ credit card information
An organization’s employees clicked on a link that allowed a worm to infiltrate and encrypt the organization’s operating system, rendering it unusable. A group of hackers is demanding payment to unlock the encryption
A group of online activists hacked into the private email and confidential records of the local police department and released the information online to expose the corrupt practices of the department
Answer:
BExplanation:
Which of the following responsibilities would ordinarily fall under the help desk function of an organization?
Options:
Maintenance service items such as production support
Management of infrastructure services, including network management
Physical hosting of mainframes and distributed servers
End-to-end security architecture design
Answer:
AExplanation:
Which of the following is true of matrix organizations?
Options:
A unity-of-command concept requires employees to report technically, functionally, and administratively to the same manager.
A combination of product and functional departments allows management to utilize personnel from various functions.
Authority, responsibility, and accountability of the units involved may vary based on the project's life or the organization's culture.
It is best suited for firms with scattered locations or for multi-line, large-scale firms.
Answer:
BExplanation:
Comprehensive and Detailed In-Depth Explanation:
A matrix organization combines functional and product-based structures, allowing employees to work across multiple departments and report to multiple managers. This enables businesses to utilize expertise from various areas efficiently.
Option A (Unity of command) does not apply to matrix organizations, as employees often report to multiple supervisors.
Option C (Variable authority and accountability) is a secondary characteristic but does not define matrix structures.
Option D (Best for scattered locations/multi-line firms) applies more to divisional rather than matrix structures.
Thus, the correct answer is B, as matrix structures enable collaboration across functional and product teams.
Which of the following risks would involve individuals attacking an oil company’s IT system as a sign of solidarity against drilling in a local area?
Options:
Tampering
Hacking
Phishing
Piracy
Answer:
BExplanation:
The head of the research and development department at a manufacturing organization believes that his team lacks expertise in some areas and decides to hire more experienced researchers to assist in the development of a new product. Which of the following variances are likely to occur as the result of this decision?
Favorable labor efficiency variance
Adverse labor rate variance
Adverse labor efficiency variance
Favorable labor rate variance
Options:
1 and 2.
1 and 4.
3 and 4.
2 and 3.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
A favorable labor efficiency variance (Option 1) occurs because experienced workers complete tasks more efficiently, reducing time and waste.
An adverse labor rate variance (Option 2) arises because hiring experienced employees increases labor costs compared to budgeted rates.
Option 3 (Adverse labor efficiency variance) is incorrect because skilled workers typically improve efficiency.
Option 4 (Favorable labor rate variance) is incorrect because higher wages increase costs, leading to an adverse variance.
Thus, the correct answer is A (1 and 2 only).
Which of the following is improved by the use of smart devices?
Options:
Version control
Privacy
Portability
Secure authentication
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
Smart devices often incorporate advanced security features that enhance secure authentication mechanisms. These features may include biometric sensors (such as fingerprint readers or facial recognition), hardware tokens, and secure enclaves that store authentication credentials. By utilizing these technologies, smart devices provide robust methods to verify user identities, thereby strengthening access controls to sensitive information and systems. While smart devices do offer portability (option C), their primary contribution to security lies in enhancing authentication processes. Version control (option A) pertains to managing changes in software or documents and is not directly impacted by smart devices. Privacy (option B) can be influenced by smart devices, but the direct improvement is in secure authentication, which in turn can support privacy protections.
Which of the following statements is true regarding data backup?
Options:
System backups should always be performed in real-time.
Backups should be stored in a secured location onsite for easy access.
The tape rotation schedule affects how long data is retained.
Backup media should be restored only in case of a hardware or software failure.
Answer:
CExplanation:
Comprehensive and Detailed In-Depth Explanation:
The tape rotation schedule is a method used to manage and organize backup media to ensure data is retained for the required period and can be restored when necessary. Different rotation schemes, such as Grandfather-Father-Son (GFS), determine how long each backup tape is kept before being overwritten, directly affecting data retention policies. While real-time backups (option A) provide continuous data protection, they are not always necessary or practical for all systems. Storing backups onsite (option B) offers quick access but may not protect against site-specific disasters; offsite storage is often recommended. Regular restoration tests (contrary to option D) are essential to ensure backup integrity and reliability, not just in failure scenarios.
Which of the following statements is true regarding a bring-your-own-device (BYOD) environment?
Options:
There is a greater need for organizations to rely on users to comply with policies and procedures.
With fewer devices owned by the organization, there is reduced need to maintain documented policies and procedures.
Incident response times are less critical in the BYOD environment compared to a traditional environment.
There is greater sharing of operational risk in a BYOD environment.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
In a BYOD environment, employees use personal devices to access company systems, making compliance with policies and procedures critical for data security.
Option B (Reduced need for policies) – Incorrect, as BYOD increases security complexity, requiring stricter policies.
Option C (Less critical incident response) – Incorrect, as BYOD increases security risks, making quick response times crucial.
Option D (Greater risk sharing) – Organizations remain ultimately responsible for security, even with personal devices.
Since employee compliance is essential to mitigating security risks in BYOD settings, Option A is correct.
Which of the following controls refers to requiring employees to use a combination of PINs, passwords, and/or biometrics to access an organization's smart device apps and data?
Options:
Remote wipe.
Software encryption.
Device encryption.
Authentication.
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
Authentication ensures that only authorized users can access a system by requiring credentials such as PINs, passwords, or biometrics.
Option A (Remote wipe) – Deletes data but does not control initial access.
Option B (Software encryption) – Protects stored data, not user access.
Option C (Device encryption) – Secures the device, but authentication controls access.
Since authentication ensures secure user verification, Option D is correct.
Based on test results, an IT auditor concluded that the organization would suffer unacceptable loss of data if there was a disaster at its data center. Which of the following test results would likely lead the auditor to this conclusion?
Options:
Requested backup tapes were not returned from the offsite vendor in a timely manner
Returned backup tapes from the offsite vendor contained empty spaces
Critical systems have been backed up more frequently than required
Critical system backup tapes are taken off site less frequently than required
Answer:
DExplanation:
An internal auditor is assessing the risks related to an organization’s mobile device policy. She notes that the organization allows third parties (vendors and visitors) to use outside smart devices to access its proprietary networks and systems. Which of the following types of smart device risks should the internal auditor be most concerned about?
Options:
Compliance.
Privacy.
Strategic.
Physical security.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
Allowing external devices to access proprietary systems introduces compliance risks, as these devices may not meet the organization’s security, data protection, and regulatory standards.
Option B (Privacy) – Important but does not fully capture the risk of unauthorized access or non-compliance with security protocols.
Option C (Strategic) – Strategic risks relate to business direction, not security concerns with third-party access.
Option D (Physical security) – Physical risks involve device theft, which is secondary to compliance when granting access.
Since compliance violations can lead to regulatory penalties and data breaches, Option A (Compliance) is the correct answer.
Which of the following is an example of a smart device security control intended to prevent unauthorized users from gaining access to a device’s data or applications?
Options:
Anti-malware software
Authentication
Spyware
Rooting
Answer:
BExplanation:
A motivational technique generally used to overcome monotony and job-related boredom is:
Options:
Job specification.
Job objectives.
Job rotation.
Job description.
Answer:
CExplanation:
Comprehensive and Detailed In-Depth Explanation:
Job rotation involves periodically moving employees between different tasks, roles, or departments to increase engagement, reduce boredom, and enhance skill development.
Option A (Job specification) – Defines job responsibilities but does not address boredom.
Option B (Job objectives) – Focuses on performance goals rather than task variety.
Option D (Job description) – Simply documents job roles without changing daily tasks.
Thus, job rotation (Option C) is the most effective strategy for overcoming monotony and job-related boredom.
An investor has acquired an organization that has a dominant position in a mature, slow-growth industry and consistently creates positive financial income. Which of the following terms would the investor most likely label this investment in her portfolio?
Options:
A star
A cash cow
A question mark
A dog
Answer:
BExplanation:
Which of the following purchasing scenarios would gain the greatest benefit from implementing electronic data interchange (EDI)?
Options:
A just-in-time purchasing environment
A large volume of custom purchases
A variable volume sensitive to material cost
A currently inefficient purchasing process
Answer:
AExplanation:
Which of the following represents an example of a physical security control?
Options:
Access rights are allocated according to the organization’s policy
There is confirmation that data output is accurate and complete
Servers are located in locked rooms to which access is restricted
A record is maintained to track the process from data input to storage
Answer:
CExplanation:
For employees, the primary value of implementing job enrichment is which of the following?
Options:
Validation of the achievement of their goals and objectives
Increased knowledge through the performance of additional tasks
Support for personal growth and a meaningful work experience
An increased opportunity to manage better the work done by their subordinates
Answer:
CExplanation:
A large retail customer made an offer to buy 10,000 units at a special price of $7 per unit. The manufacturer usually sells each unit for $10. Variable manufacturing costs are $5 per unit and fixed manufacturing costs are $3 per unit. For the manufacturer to accept the offer, which of the following assumptions needs to be true?
Options:
Fixed and variable manufacturing costs are less than the special offer selling price
The manufacturer can fulfill the order without expanding the capacities of the production facilities
Costs related to accepting this offer can be absorbed through the sale of other products
The manufacturer’s production facilities are currently operating at full capacity
Answer:
BExplanation:
Which of the following lists is comprised of computer hardware only?
Options:
A central processing unit, a scanner, and a value-added network
A computer chip, a data warehouse, and a router
A server, a firewall, and a smartphone
A workstation, a modem, and a disk drive
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
Computer hardware refers to the physical components of a computer system.
Workstation: A high-performance computer designed for technical or scientific applications.
Modem: A device that modulates and demodulates signals for data transmission over communication lines.
Disk drive: A device that reads and/or writes data to a disk storage medium.
Option D lists only physical components, fitting the definition of computer hardware.
In contrast:
Value-added network (option A): A hosted service offering specialized networking services, not a physical component.
Data warehouse (option B): A system used for reporting and data analysis, representing a data storage concept rather than a physical device.
Firewall (option C): While it can be hardware, it is often implemented as software; thus, the term doesn't exclusively denote hardware.
Therefore, option D accurately represents a list of computer hardware components.
References:
The Institute of Internal Auditors. (n.d.). CIA Exam Syllabus. Retrieved from
Which of the following situations best applies to an organization that uses a project, rather than a process, to accomplish its business activities?
Options:
A clothing company designs, makes, and sells a new item
A commercial construction company is hired to build a warehouse
A city department sets up a new firefighter training program
A manufacturing organization acquires component parts from a contracted vendor
Answer:
BExplanation:
Which of the following risks is best addressed by encryption?
Options:
Information integrity risk.
Privacy risk.
Access risk.
Software risk.
Answer:
BExplanation:
Comprehensive and Detailed In-Depth Explanation:
Encryption is a security measure that protects the confidentiality of sensitive data by converting it into an unreadable format. This directly addresses privacy risks by preventing unauthorized access to personal or confidential information.
Option A (Information integrity risk) – Integrity controls (e.g., checksums, hash functions) address this risk.
Option C (Access risk) – Managed through authentication and access controls, not encryption.
Option D (Software risk) – Related to vulnerabilities, which encryption does not directly mitigate.
Since encryption protects privacy by securing sensitive data, Option B is correct.
Which of the following best explains why an organization would enter into a capital lease contract?
Options:
To increase the ability to borrow additional funds from creditors
To reduce the organization’s free cash flow from operations
To improve the organization’s free cash flow from operations
To acquire the asset at the end of the lease period at a price lower than the fair market value
Answer:
DExplanation:
Which of the following statements is true regarding the management-by-objectives (MBO) approach?
Options:
Management by objectives is most helpful in organizations that have rapid changes
Management by objectives is most helpful in mechanistic organizations with rigidly defined tasks
Management by objectives helps organizations to keep employees motivated
Management by objectives helps organizations to distinguish clearly strategic goals from operational goals
Answer:
CExplanation:
An organization has instituted a bring-your-own-device (BYOD) work environment. Which of the following policies best addresses the increased risk to the organization’s network incurred by this environment?
Options:
Limit the use of the employee devices for personal use to mitigate the risk of exposure to organizational data
Ensure that relevant access to key applications is strictly controlled through an approval and review process
Institute detection and authentication controls for all devices used for network connectivity and data storage
Use management software to scan and then prompt patch reminders when devices connect to the network
Answer:
BExplanation:
For employees, the primary value of implementing job enrichment is which of the following?
Options:
Validation of the achievement of their goals anti objectives
Increased knowledge through the performance of additional tasks
Support for personal growth and a meaningful work experience
An increased opportunity to manage better the work done by their subordinates
Answer:
CExplanation:
Job enrichment is a motivational strategy where employees are given more control, responsibility, and meaningful tasks in their roles. It aims to increase job satisfaction, personal growth, and motivation by making work more engaging and fulfilling.
Let’s analyze each option:
Option A: Validation of the achievement of their goals and objectives
Incorrect.
While job enrichment may contribute to achieving personal and professional goals, its primary purpose is not just validation but improving employee engagement and motivation.
Option B: Increased knowledge through the performance of additional tasks
Incorrect.
Job enlargement (not job enrichment) involves assigning additional tasks without necessarily increasing responsibility or autonomy.
Job enrichment focuses on providing meaningful and challenging work, not just adding tasks.
Option C: Support for personal growth and a meaningful work experience
Correct.
Job enrichment enhances job satisfaction by giving employees greater autonomy, responsibility, and purpose in their roles.
It encourages personal and professional development, leading to a more meaningful work experience.
IIA Reference: Internal auditors assessing human resource and organizational performance management focus on employee motivation strategies, including job enrichment. (IIA Practice Guide: Talent Management and Human Capital Risks)
Option D: An increased opportunity to manage better the work done by their subordinates
Incorrect.
Job enrichment does not necessarily focus on managing subordinates but rather on enhancing individual job roles by making them more fulfilling.
Thus, the verified answer is C. Support for personal growth and a meaningful work experience.
While auditing an organization's customer call center, an internal auditor notices that Key performance indicators show a positive trend, despite the fact that there have been increasing customer complaints over the same period. Which of the following audit recommendations would most likely correct the cause of this inconsistency?
Options:
Review the call center script used by customer service agents to interact with callers, and update the script if necessary.
Be-emphasize the importance of call center employees completing a certain number of calls per hour.
Retrain call center staff on area processes and common technical issues that they will likely be asked to resolve.
Increase the incentive for call center employees to complete calls quickly and raise the number of calls completed daily
Answer:
BExplanation:
Understanding the Call Center Performance Issue:
The key performance indicators (KPIs) show a positive trend, meaning the call center appears to be performing well.
However, customer complaints are increasing, indicating that the KPIs are not accurately reflecting service quality.
This suggests that employees may be prioritizing call quantity over call quality, likely due to pressure to meet call quotas.
Why De-Emphasizing Call Quotas is the Best Solution:
Encourages Quality Over Speed: Reducing the emphasis on call volume allows agents to spend more time resolving customer issues effectively.
Improves Customer Satisfaction: Agents can provide more thorough assistance, reducing repeat calls and complaints.
Aligns KPIs with Service Quality: Shifting focus from quantity-based KPIs to quality-based KPIs ensures performance measurements reflect actual customer experience.
Why Other Options Are Incorrect:
A. Review the call center script used by customer service agents to interact with callers, and update the script if necessary – Incorrect.
While updating scripts may help, it does not address the root issue of employees rushing through calls to meet quotas.
C. Retrain call center staff on area processes and common technical issues that they will likely be asked to resolve – Incorrect.
Training is useful, but if agents are pressured to complete calls quickly, training alone will not resolve the issue.
D. Increase the incentive for call center employees to complete calls quickly and raise the number of calls completed daily – Incorrect.
This would worsen the issue by further incentivizing speed over customer satisfaction, leading to more complaints.
IIA’s Perspective on Performance Metrics and Customer Service Quality:
IIA Standard 2120 – Risk Management requires organizations to ensure that performance metrics align with actual business objectives.
IIA GTAG (Global Technology Audit Guide) on Performance Measurement recommends balancing quantitative KPIs (e.g., call volume) with qualitative KPIs (e.g., customer satisfaction scores).
COSO Internal Control Framework supports adjusting performance incentives to ensure alignment with business objectives.
IIA References:
IIA Standard 2120 – Risk Management & KPI Alignment
IIA GTAG – Performance Metrics in Customer Service
COSO Internal Control Framework – Effective KPI Design
Thus, the correct and verified answer is B. De-emphasize the importance of call center employees completing a certain number of calls per hour.
An internal auditor found the following information while reviewing the monthly financial siatements for a wholesaler of safety
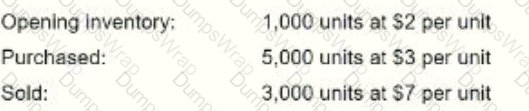
The cost of goods sold was reported at $8,500. Which of the following inventory methods was used to derive this value?
Options:
Average cost method
First-in, first-out (FIFO) method
Specific identification method
Activity-based costing method
Answer:
BExplanation:
To determine which inventory method was used, we calculate the cost of goods sold (COGS) under different inventory valuation methods.
Opening Inventory: 1,000 units @ $2 each = $2,000
Purchased: 5,000 units @ $3 each = $15,000
Total Inventory: 6,000 units
Units Sold: 3,000 at $7 per unit
Reported COGS: $8,500
Given Data:FIFO Calculation:FIFO (First-In, First-Out) assumes that the oldest inventory is sold first.
1,000 units from opening inventory @ $2 = $2,000
2,000 units from purchases @ $3 = $6,000
Total COGS under FIFO: $2,000 + $6,000 = $8,000
Average Cost Calculation:Average cost per unit =
Total Cost of InventoryTotal Units=(2,000+15,000)6,000=17,0006,000=2.83 per unit\frac{\text{Total Cost of Inventory}}{\text{Total Units}} = \frac{(2,000 + 15,000)}{6,000} = \frac{17,000}{6,000} = 2.83 \text{ per unit}Total UnitsTotal Cost of Inventory=6,000(2,000+15,000)=6,00017,000=2.83 per unit
COGS using average cost method: 3,000×2.83=8,4903,000 \times 2.83 = 8,4903,000×2.83=8,490 This is not an exact match to the reported COGS of $8,500.
Since the closest method to the reported value is FIFO ($8,000 vs. $8,500 reported COGS, accounting for possible rounding errors or additional costs), FIFO is the most likely method used.
(A) Average cost method. ❌ Incorrect. The calculated COGS using the weighted average method was $8,490, which does not match exactly with the reported COGS of $8,500.
(B) First-in, first-out (FIFO) method. ✅ Correct. The FIFO method yielded $8,000, which is the closest match to the reported COGS. Minor rounding adjustments or other expenses could explain the difference of $500.
(C) Specific identification method. ❌ Incorrect. This method applies when each inventory item is individually tracked, which is not mentioned in the question.
(D) Activity-based costing method. ❌ Incorrect. Activity-based costing (ABC) is used for overhead allocation and is not a primary inventory valuation method.
IIA GTAG – "Auditing Inventory Management"
IIA Standard 2130 – Control Activities (Inventory and Costing Methods)
GAAP and IFRS – FIFO, Weighted Average, and Specific Identification Methods
Analysis of Answer Choices:IIA References:Thus, the correct answer is B (FIFO method) because it provides the closest cost match to the reported COGS.
Which of the following statements. Is most accurate concerning the management and audit of a web server?
Options:
The file transfer protocol (FTP) should always be enabled.
The simple mail transfer protocol (SMTP) should be operating under the most privileged accounts.
The number of ports and protocols allowed to access the web server should be maximized.
Secure protocols for confidential pages should be used instead of dear-text protocols such as HTTP or FTP.
Answer:
DExplanation:
Importance of Secure Protocols for Web Server Management:
Web servers handle sensitive data, including user credentials, financial information, and confidential communications.
Using secure protocols like HTTPS, SFTP, and TLS-encrypted SMTP ensures data is encrypted and protected from cyber threats.
Risks of Clear-Text Protocols (HTTP & FTP):
HTTP (Hypertext Transfer Protocol) and FTP (File Transfer Protocol) transmit data in plaintext, making them vulnerable to man-in-the-middle (MITM) attacks, packet sniffing, and unauthorized access.
SFTP (Secure File Transfer Protocol) and HTTPS (Hypertext Transfer Protocol Secure) encrypt data, mitigating these risks.
Why Other Options Are Incorrect:
A. The file transfer protocol (FTP) should always be enabled – Incorrect.
FTP is not secure, and enabling it can expose the server to unauthorized file access and cyberattacks.
B. The simple mail transfer protocol (SMTP) should be operating under the most privileged accounts – Incorrect.
SMTP should operate with minimal privileges to reduce security risks in case of a breach.
C. The number of ports and protocols allowed to access the web server should be maximized – Incorrect.
Minimizing open ports and protocols reduces the attack surface and limits unauthorized access.
IIA’s Perspective on IT Security and Web Server Management:
IIA Standard 2110 – Governance requires organizations to establish secure IT practices, including encryption and secure protocols.
IIA GTAG (Global Technology Audit Guide) on IT Risks emphasizes minimizing security vulnerabilities by using encrypted communication.
ISO 27001 Security Standard recommends secure transmission protocols for protecting sensitive data.
IIA References:
IIA Standard 2110 – IT Security and Governance
IIA GTAG – IT Risks and Secure Web Server Management
ISO 27001 Security Standard – Data Encryption and Secure Transmission
Thus, the correct and verified answer is D. Secure protocols for confidential pages should be used instead of clear-text protocols such as HTTP or FTP.
Which of the following statements is true regarding the management-by-objectives method?
Options:
Management by objectives is most helpful in organizations that have rapid changes.
Management by objectives is most helpful in mechanistic organizations with rigidly defined tasks.
Management by objectives helps organizations to keep employees motivated.
Management by objectives helps organizations to distinguish clearly strategic goals from operational goals.
Answer:
CExplanation:
Understanding Management by Objectives (MBO):
MBO is a performance management approach where employees and managers set specific, measurable goals together.
The main purpose of MBO is to align individual objectives with organizational goals, enhancing motivation and engagement.
Why Option C (Helps Keep Employees Motivated) Is Correct?
Employee motivation improves when individuals understand how their efforts contribute to the organization’s success.
Setting clear objectives and allowing employees to participate in goal-setting increases job satisfaction and engagement.
IIA Standard 2120 – Risk Management supports frameworks like MBO that contribute to organizational performance and employee effectiveness.
Why Other Options Are Incorrect?
Option A (Most helpful in organizations with rapid changes):
MBO is less effective in rapidly changing environments because it relies on long-term goal setting.
Option B (Best in mechanistic organizations with rigid tasks):
MBO works better in adaptive, flexible organizations, not those with rigid structures.
Option D (Distinguishes strategic from operational goals):
MBO focuses on individual and team goals, not distinguishing strategic vs. operational goals.
MBO enhances employee motivation by involving them in goal-setting and performance tracking.
IIA Standard 2120 supports employee engagement strategies for better performance management.
Final Justification:IIA References:
IPPF Standard 2120 – Risk Management (Employee Engagement & Performance Management)
COSO ERM – Performance Measurement & Goal Alignment
An organization requires an average of 5S days to convert raw materials into finished products to sell. An average of 42 additional days is required to collect receivables. If the organization takes an average of 10 days to pay for the raw materials, how long is its total cash conversion cycle?
Options:
26 days.
90 days,
100 days.
110 days
Answer:
CExplanation:
Understanding the Cash Conversion Cycle (CCC):
The Cash Conversion Cycle (CCC) measures the time taken for a company to convert raw materials into cash flow.
CCC is calculated using the formula: CCC=DaysInventoryOutstanding(DIO)+DaysSalesOutstanding(DSO)−DaysPayableOutstanding(DPO)CCC = Days Inventory Outstanding (DIO) + Days Sales Outstanding (DSO) - Days Payable Outstanding (DPO)CCC=DaysInventoryOutstanding(DIO)+DaysSalesOutstanding(DSO)−DaysPayableOutstanding(DPO)
Where:
DIO (Days Inventory Outstanding) = 55 days (time to convert raw materials to finished products).
DSO (Days Sales Outstanding) = 42 days (time to collect receivables).
DPO (Days Payable Outstanding) = 10 days (time to pay for raw materials).
Applying the Formula:
CCC=55+42−10CCC = 55 + 42 - 10CCC=55+42−10 CCC=100 daysCCC = 100 \text{ days}CCC=100 days
Why Option C (100 Days) Is Correct?
The CCC represents the time the company’s cash is tied up in production and sales before receiving payment.
This calculation aligns with IIA Standard 2120 – Risk Management, which requires auditors to assess financial liquidity and operational efficiency.
Why Other Options Are Incorrect?
Option A (26 days): Incorrect calculation.
Option B (90 days): Does not subtract DPO correctly.
Option D (110 days): Incorrect addition of all components instead of following the CCC formula.
The correct cash conversion cycle is 100 days, calculated using standard CCC methodology.
IIA Standard 2120 and financial management principles confirm the correct calculation.
Final Justification:IIA References:
IPPF Standard 2120 – Risk Management (Financial Performance & Liquidity Risk)
COSO ERM – Working Capital & Cash Flow Management
Financial Management Best Practices – Cash Conversion Cycle Analysis
A one-time password would most likely be generated in which of the following situations?
Options:
When an employee accesses an online digital certificate
When an employee's biometrics have been accepted.
When an employee creates a unique digital signature,
When an employee uses a key fob to produce a token.
Answer:
DExplanation:
A one-time password (OTP) is a unique, temporary password that is valid for a single login session or transaction. It is commonly used in multi-factor authentication (MFA) systems to enhance security.
Correct Answer (D - When an Employee Uses a Key Fob to Produce a Token)
Key fobs generate a time-sensitive one-time password (OTP), which is used in conjunction with a traditional password to enhance security.
These devices are part of two-factor authentication (2FA) or multi-factor authentication (MFA) methods.
The IIA GTAG 9: Identity and Access Management discusses OTP tokens as a strong security control to prevent unauthorized access.
Why Other Options Are Incorrect:
Option A (When an employee accesses an online digital certificate):
Digital certificates authenticate users or devices, but they do not generate one-time passwords.
Option B (When an employee's biometrics have been accepted):
Biometric authentication (e.g., fingerprint, facial recognition) grants access based on biological traits, not an OTP.
Option C (When an employee creates a unique digital signature):
Digital signatures authenticate documents and transactions, but they are not time-sensitive one-time passwords.
IIA GTAG 9: Identity and Access Management – Covers OTP tokens as a security measure.
IIA Practice Guide: Auditing IT Security Controls – Recommends OTPs as part of secure authentication.
Step-by-Step Explanation:IIA References for Validation:Thus, D is the correct answer because key fobs generate one-time passwords for secure authentication.
An organization has instituted a bring-your-own-device (BYOD) work environment. Which of the following policies best addresses the increased risk to the organization's network incurred by this environment?
Options:
Limit the use of the employee devices for personal use to mitigate the risk of exposure to organizational data.
Ensure that relevant access to key applications is strictly controlled through an approval and review process.
Institute detection and authentication controls for all devices used for network connectivity and data storage.
Use management software scan and then prompt parch reminders when devices connect to the network
Answer:
CExplanation:
Understanding BYOD Risks:
A Bring-Your-Own-Device (BYOD) policy allows employees to use personal devices (e.g., laptops, smartphones, tablets) for work.
This increases security risks such as unauthorized access, malware infections, data leakage, and non-compliance with IT security policies.
Why Option C (Detection and Authentication Controls) Is Correct?
Detection and authentication controls ensure that:
Only authorized devices can connect to the organization's network.
User authentication mechanisms (such as multi-factor authentication) verify identities before granting access.
Devices with security vulnerabilities are flagged and restricted.
This aligns with IIA Standard 2110 – Governance, which emphasizes IT security controls for risk mitigation.
ISO 27001 and NIST Cybersecurity Framework also recommend device authentication and monitoring for secure network access.
Why Other Options Are Incorrect?
Option A (Limit personal use of employee devices):
Limiting personal use does not fully address network security risks; malware can still infect devices.
Option B (Control access through approvals and reviews):
While access control is important, it does not mitigate the broader risks of compromised devices connecting to the network.
Option D (Software scans and patch reminders):
Patching is important, but it does not prevent unauthorized access or ensure authentication for devices.
Implementing device detection and authentication controls is the most effective way to mitigate security risks in a BYOD environment.
IIA Standard 2110 and ISO 27001 emphasize strong network security measures.
Final Justification:IIA References:
IPPF Standard 2110 – Governance (IT Risk Management & BYOD Security)
ISO 27001 – Information Security Management
NIST Cybersecurity Framework – Access Control & Authentication
Which of the following should be included in a data privacy poky?
1. Stipulations for deleting certain data after a specified period of time.
2. Guidance on acceptable methods for collecting personal data.
3. A requirement to retain personal data indefinitely to ensure a complete audit trail,
4. A description of what constitutes appropriate use of personal data.
Options:
1 and 2 only
2 and 3 only
1, 2 and 4 only
2, 3, and 4 only
Answer:
CExplanation:
A data privacy policy outlines how an organization collects, stores, processes, and protects personal data. It should comply with global data protection regulations such as GDPR, CCPA, and IIA guidelines on data security.
(1) Stipulations for deleting certain data after a specified period of time. ✅
Correct. Many data protection laws (e.g., GDPR Article 5) require organizations to delete personal data after a defined retention period to reduce data breach risks.
(2) Guidance on acceptable methods for collecting personal data. ✅
Correct. A privacy policy must define legal and ethical ways to collect personal data (e.g., user consent, lawful processing).
(3) A requirement to retain personal data indefinitely to ensure a complete audit trail. ❌
Incorrect. Retaining personal data indefinitely violates most data privacy regulations (e.g., GDPR Right to Be Forgotten). Data must be stored only for as long as necessary.
(4) A description of what constitutes appropriate use of personal data. ✅
Correct. A privacy policy should clearly define how collected data can and cannot be used to prevent misuse and ensure compliance.
IIA GTAG – "Auditing Privacy Risks"
IIA Standard 2110 – Governance (Data Protection & Privacy)
GDPR (General Data Protection Regulation) – Articles 5 & 17 (Data Retention & Deletion)
Analysis of Answer Choices:IIA References:Thus, the correct answer is C (1, 2, and 4 only) because data should not be retained indefinitely, and the policy must include data collection, retention, and appropriate usage guidelines.
According to Herzberg's Two-Factor Theory of Motivation, which of the following factors arc mentioned most often by satisfied employees?
Options:
Salary and status
Responsibility and advancement
Work conditions and security
Peer relationships and personal life
Answer:
BExplanation:
Herzberg’s Two-Factor Theory of Motivation identifies two categories of workplace factors:
Hygiene Factors – Prevent dissatisfaction but do not create motivation (e.g., salary, job security, work conditions).
Motivational Factors – Lead to job satisfaction and motivation (e.g., achievement, responsibility, advancement, recognition).
(A) Salary and status. ❌ Incorrect.
Salary is a hygiene factor, meaning it prevents dissatisfaction but does not directly drive job satisfaction.
Status is also not a strong motivator under Herzberg’s theory.
(B) Responsibility and advancement. ✅ Correct.
These are motivational factors in Herzberg’s theory.
Employees feel satisfied when they have responsibility, career growth, and promotion opportunities.
IIA GTAG "Auditing Human Resource Management" highlights career development as a key driver of employee motivation and retention.
(C) Work conditions and security. ❌ Incorrect.
These are hygiene factors, which help avoid dissatisfaction but do not actively motivate employees.
(D) Peer relationships and personal life. ❌ Incorrect.
Good relationships with coworkers help, but they are not primary motivators under Herzberg’s theory.
IIA GTAG – "Auditing Human Resource Management"
IIA Standard 2110 – Governance (Employee Motivation & Engagement)
Herzberg’s Two-Factor Theory of Motivation (Workplace Psychology Research)
Analysis of Answer Choices:IIA References:Thus, the correct answer is B, as responsibility and advancement are the key motivational factors leading to employee satisfaction.
Which of the following purchasing scenarios would gain the greatest benefit from implementing electronic cate interchange?
Options:
A just-in-time purchasing environment
A Large volume of custom purchases
A variable volume sensitive to material cost
A currently inefficient purchasing process
Answer:
AExplanation:
Electronic Data Interchange (EDI) is a system that allows businesses to exchange documents (purchase orders, invoices, shipping notices) electronically, improving efficiency and accuracy.
Correct Answer (A - A Just-in-Time Purchasing Environment)
Just-in-time (JIT) purchasing requires real-time inventory management to reduce waste and costs.
EDI improves JIT by automating purchase orders, reducing lead times, and preventing stockouts.
The IIA GTAG 8: Audit of Inventory Management highlights that JIT purchasing benefits the most from automation through EDI.
Why Other Options Are Incorrect:
Option B (A large volume of custom purchases):
Custom purchases vary significantly in specifications, making standard EDI transactions less effective.
Option C (A variable volume sensitive to material cost):
While EDI helps with volume fluctuations, cost-sensitive purchasing requires additional financial analysis beyond EDI automation.
Option D (A currently inefficient purchasing process):
EDI improves efficiency, but implementing it in a failing process without first optimizing procedures could lead to automation of inefficiencies.
IIA GTAG 8: Audit of Inventory Management – Discusses automation benefits in JIT purchasing.
IIA Practice Guide: Auditing IT Controls – Covers EDI as a key tool for procurement efficiency.
Step-by-Step Explanation:IIA References for Validation:Thus, the greatest benefit from EDI is in a Just-in-Time (JIT) purchasing environment (A).
Which of the following is the best example of IT governance controls?
Options:
Controls that focus on segregation of duties, financial, and change management,
Personnel policies that define and enforce conditions for staff in sensitive IT areas.
Standards that support IT policies by more specifically defining required actions
Controls that focus on data structures and the minimum level of documentation required
Answer:
AExplanation:
IT governance controls ensure that an organization's IT systems align with business objectives, manage risks, and comply with regulatory requirements. These controls cover areas such as security, financial oversight, change management, and operational efficiency.
Let’s analyze each option:
Option A: Controls that focus on segregation of duties, financial, and change management.
Correct.
Segregation of duties (SoD) prevents conflicts of interest and reduces fraud risk.
Financial controls ensure IT expenditures align with budgets and policies.
Change management controls ensure system modifications follow formal approval and testing procedures.
These areas are core components of IT governance, ensuring security, compliance, and efficiency.
IIA Reference: Internal auditors evaluate IT governance using frameworks like COBIT (Control Objectives for Information and Related Technologies) and ISO 27001. (IIA GTAG: Auditing IT Governance)
Option B: Personnel policies that define and enforce conditions for staff in sensitive IT areas.
Incorrect.
While personnel policies support IT security, they do not fully represent IT governance controls. IT governance is broader and includes risk management, compliance, and operational efficiency.
Option C: Standards that support IT policies by more specifically defining required actions.
Incorrect.
Standards are part of IT governance but are not controls themselves. IT governance requires enforcement mechanisms like segregation of duties and change management to ensure compliance.
Option D: Controls that focus on data structures and the minimum level of documentation required.
Incorrect.
While data governance is a subset of IT governance, IT governance includes wider financial, security, and operational controls.
Thus, the verified answer is A. Controls that focus on segregation of duties, financial, and change management.
A small software development firm designs and produces custom applications for businesses. The application development team consists of employees from multiple departments who all report to a single project manager. Which of the following organizational structures does this situation represent?
Options:
Functional departmentalization.
Product departmentalization
Matrix organization.
Divisional organization
Answer:
CExplanation:
Understanding Organizational Structures:
Organizations structure their workforce based on functions, products, or a combination of both.
A matrix organization combines functional and project-based structures, where employees report to both a functional manager and a project manager.
Why Option C (Matrix Organization) Is Correct?
The software development firm uses employees from multiple departments who report to a single project manager, which is a defining characteristic of a matrix structure.
Employees maintain their departmental roles while contributing to project-based work.
IIA Standard 2110 – Governance supports evaluating flexible organizational structures like matrix organizations to ensure accountability and risk management.
Why Other Options Are Incorrect?
Option A (Functional departmentalization):
In functional structures, employees report to one department head, not a project manager.
Option B (Product departmentalization):
In product-based structures, employees are grouped based on specific product lines, not cross-functional projects.
Option D (Divisional organization):
A divisional structure separates business units based on markets, regions, or customer segments, not cross-functional teams.
A matrix organization allows employees to work across departments under a project manager, making option C the best choice.
IIA Standard 2110 supports assessing governance structures that involve cross-functional teams.
Final Justification:IIA References:
IPPF Standard 2110 – Governance (Organizational Structures & Reporting Lines)
COSO ERM – Risk Management in Matrix Organizations
Project Management Institute (PMI) – Matrix Management Best Practices
Which of the following job design techniques would most likely be used to increase employee motivation through job responsibility and recognition?
Options:
Job complicating
Job rotation
Job enrichment
Job enlargement
Answer:
CExplanation:
Understanding Job Enrichment:
Job enrichment is a job design technique that increases motivation by adding meaningful responsibilities, autonomy, and recognition to a job.
It aligns with Herzberg’s Two-Factor Theory, which suggests that responsibility and recognition are key motivators.
How Job Enrichment Increases Employee Motivation:
Increases Autonomy: Employees are given more decision-making power, leading to a stronger sense of ownership.
Provides Recognition: Workers receive direct feedback and acknowledgment for their contributions.
Encourages Skill Development: Employees handle more complex tasks, improving job satisfaction and career growth opportunities.
Why Other Options Are Incorrect:
A. Job complicating – Incorrect, as this is not a recognized job design technique; increasing job difficulty does not improve motivation.
B. Job rotation – Incorrect, as job rotation involves shifting employees between different tasks to reduce monotony, but it does not necessarily increase job responsibility or recognition.
D. Job enlargement – Incorrect, as job enlargement adds more tasks at the same skill level, increasing workload without necessarily improving responsibility or recognition.
IIA’s Perspective on Employee Motivation and Organizational Success:
IIA Standard 2120 – Risk Management states that internal auditors should evaluate employee engagement strategies, including job design techniques.
COSO ERM Framework emphasizes that motivated employees contribute to operational efficiency and organizational success.
IIA References:
IIA Standard 2120 – Risk Management & Employee Motivation
Herzberg’s Two-Factor Theory – Motivation through Responsibility and Recognition
COSO ERM – Employee Engagement and Organizational Performance
Thus, the correct and verified answer is C. Job enrichment.
At one organization, the specific terms of a contract require both the promisor end promise to sign the contract in the presence of an independent witness.
What is the primary role to the witness to these signatures?
Options:
A witness verifies the quantities of the copies signed.
A witness verifies that the contract was signed with the free consent of the promisor and promise.
A witness ensures the completeness of the contract between the promisor and promise.
A witness validates that the signatures on the contract were signed by tire promisor and promise.
Answer:
DExplanation:
Role of a Witness in Contract Signing:
A witness is a neutral third party who observes the signing of a contract and confirms that the named individuals actually signed the document.
This helps prevent disputes regarding the authenticity of signatures and provides legal proof of agreement.
Why Signature Validation is the Primary Role:
Ensures legitimacy: A witness confirms that the signatures belong to the stated individuals, preventing forgery.
Legal enforceability: Many jurisdictions require witnesses for contracts to be legally binding in certain cases (e.g., wills, real estate agreements).
Provides evidence in case of disputes: If a signatory later denies signing, the witness can testify to the authenticity of the signature.
Why Other Options Are Incorrect:
A. A witness verifies the quantities of the copies signed – Incorrect.
A witness does not count copies; their role is to verify authentic signatures.
B. A witness verifies that the contract was signed with the free consent of the promisor and promisee – Incorrect.
While witnessing may imply that parties were present, it does not guarantee free consent (coercion concerns require separate legal evidence).
C. A witness ensures the completeness of the contract between the promisor and promisee – Incorrect.
Contract completeness is a legal or managerial responsibility, not a witness’s role.
IIA’s Perspective on Contract Verification and Internal Controls:
IIA Standard 2120 – Risk Management requires internal auditors to ensure proper contract validation and documentation.
COSO Internal Control Framework highlights the importance of contract controls, including witnessed signings for fraud prevention.
International Contract Law Principles emphasize the role of witnesses in reducing contract disputes.
IIA References:
IIA Standard 2120 – Risk Management in Contract Management
COSO Internal Control Framework – Legal Documentation and Witnessing
International Contract Law Principles – Witnessing Signatures for Legal Validity
Thus, the correct and verified answer is D. A witness validates that the signatures on the contract were signed by the promisor and promisee.
Which of the following responsibilities would ordinary fall under the help desk function of an organization?
Options:
Maintenance service items such as production support.
Management of infrastructure services, including network management.
Physical hosting of mainframes and distributed servers
End-to -end security architecture design.
Answer:
AExplanation:
A help desk function is responsible for providing technical support and maintenance services to end users. This includes troubleshooting issues, production support, and system maintenance rather than managing infrastructure or security architecture.
Let’s analyze each option:
Option A: Maintenance service items such as production support.
Correct. The help desk primarily provides user support, including:
Troubleshooting software and hardware issues
Resolving technical support requests
Assisting users with system access and operational questions
IIA Reference: Internal auditors assess IT service management, including help desk functions, to ensure efficient IT support and incident response. (IIA GTAG: Auditing IT Service Management)
Option B: Management of infrastructure services, including network management.
Incorrect. Infrastructure services (such as network and server management) fall under IT operations or network administration, not the help desk.
Option C: Physical hosting of mainframes and distributed servers
Incorrect. Hosting and maintaining physical servers is the responsibility of data center operations, not the help desk.
Option D: End-to-end security architecture design.
Incorrect. Security architecture design is handled by the IT security team or cybersecurity department, not the help desk.
Thus, the verified answer is A. Maintenance service items such as production support.
An internal auditor was asked to review an equal equity partnership, in one sampled transaction. Partner A transferred equipment into the partnership with a Self-declared value of 510 ,000, and Partner B contributed equipment with a self-declared value of 515,000. The capital accounts reach partner were subsequently credited with $12,500. Which of the following statements Is true regarding this transection?
Options:
The capital accounts of the partners should be increased by she original cost of the contributed equipment.
The capital accounts should be increased using a weighted average based by the current percentage of ownership.
No action is needed, as the capital account of each partner was increased by the correct amount,
The capital accounts of the partners should be increased by She fair market value of their contribution.
Answer:
DExplanation:
In an equal equity partnership, partners' capital accounts should reflect the fair market value (FMV) of assets contributed, rather than self-declared values or historical cost. The fair market value ensures equitable ownership distribution and accurate financial reporting.
Let’s analyze each option:
Option A: The capital accounts of the partners should be increased by the original cost of the contributed equipment.
Incorrect. The original cost (historical cost) of an asset is not relevant in partnership accounting. Instead, fair market value (FMV) is used to properly recognize each partner's contribution.
Option B: The capital accounts should be increased using a weighted average based on the current percentage of ownership.
Incorrect. While ownership percentages influence profit and loss distribution, initial capital contributions should be recorded at FMV, not a weighted average.
Option C: No action is needed, as the capital account of each partner was increased by the correct amount.
Incorrect. Since the partners contributed different self-declared values, the capital accounts may not be correctly recorded unless verified against FMV. The partnership agreement typically requires capital contributions to be valued based on FMV, not self-declared estimates.
Option D: The capital accounts of the partners should be increased by the fair market value of their contribution.
Correct. Fair market value (FMV) ensures that capital contributions are recorded accurately. Using self-declared values without verification can lead to misstatements in capital accounts and potential disputes.
IIA Reference: Internal auditors reviewing partnership accounting should ensure that capital accounts reflect fair market value to maintain financial accuracy. (IIA Practice Guide: Auditing Fair Value Estimates)
Thus, the verified answer is D. The capital accounts of the partners should be increased by the fair market value of their contribution.
A rapidly expanding retail organisation continues to be tightly controlled by its original small management team. Which of the following is a potential risk in this vertically centralized organization?
Options:
Lack of coordination among different business units
Operational decisions are inconsistent with organizational goals
Suboptimal decision making
Duplication of business activities
Answer:
CExplanation:
In a vertically centralized organization, decision-making authority is concentrated at the top levels of management. As a company rapidly expands, maintaining tight control by a small management team can lead to inefficiencies, delays, and suboptimal decision-making due to limited input from operational and frontline staff.
Let’s analyze each option:
Option A: Lack of coordination among different business units
Incorrect. While coordination challenges can exist in a large, decentralized organization, a tightly controlled, centralized structure typically ensures strong coordination but at the cost of slower decision-making.
Option B: Operational decisions are inconsistent with organizational goals
Incorrect. In a centralized structure, top management closely controls decision-making, making goal misalignment less likely.
Option C: Suboptimal decision making
Correct.
Decentralized decision-making allows managers closer to operations to make informed, timely decisions.
A small centralized team may lack specialized knowledge about different departments, leading to inefficient or outdated decisions.
As the company expands, delays in decision-making and lack of responsiveness to market conditions increase risk exposure.
IIA Reference: Internal auditors assess organizational structures to identify risks associated with inefficient decision-making and control bottlenecks. (IIA Standard 2110: Governance)
Option D: Duplication of business activities
Incorrect. Duplication of activities is more common in decentralized structures, where different departments operate independently. A tightly controlled, centralized structure reduces redundancy but at the cost of decision-making efficiency.
Thus, the verified answer is C. Suboptimal decision making.
A retail organization mistakenly did have include $10,000 of Inventory in the physical count at the end of the year. What was the impact to the organization's financial statements?
Options:
Cost of sales and net income are understated.
Cost of sales and net income are overstated.
Cost of sales is understated and not income is overstated.
Cost of sales is overstated and net Income is understated.
Answer:
CExplanation:
When inventory is understated (not included in the physical count) at year-end, the financial impact affects both cost of sales (COGS) and net income as follows:
Correct Answer (C - Cost of Sales is Understated and Net Income is Overstated)
The ending inventory is part of the formula used to calculate the cost of goods sold (COGS): COGS=BeginningInventory+Purchases−EndingInventoryCOGS = Beginning Inventory + Purchases - Ending InventoryCOGS=BeginningInventory+Purchases−EndingInventory
If ending inventory is understated, then:
COGS will be understated (because inventory that should have been counted as sold was omitted).
Net income will be overstated because COGS is lower than it should be, making profits appear higher.
This error causes financial misstatements, violating IIA auditing standards for financial accuracy.
Why Other Options Are Incorrect:
Option A (Cost of sales and net income are understated):
Net income would not be understated—it would be overstated because the cost of goods sold is too low.
Option B (Cost of sales and net income are overstated):
COGS would be understated, not overstated. If COGS were overstated, net income would be understated.
Option D (Cost of sales is overstated and net income is understated):
The opposite happens—COGS is understated and net income is overstated.
IIA GTAG 8: Audit of Inventory Management – Covers financial impact of inventory misstatements.
IIA Practice Guide: Auditing Financial Statements – Addresses common inventory errors and financial reporting impacts.
Step-by-Step Explanation:IIA References for Validation:Thus, C is the correct answer because an understated inventory reduces COGS and inflates net income.
Which of the following bring-your-own-device (BYOD) practices is likely to increase the risk of Infringement on local regulations, such as copyright or privacy laws?
Options:
Not installing anti-malware software
Updating operating software in a haphazard manner,
Applying a weak password for access to a mobile device.
JoIIbreaking a locked smart device
Answer:
DExplanation:
Understanding BYOD Risks and Legal Implications
Bring-your-own-device (BYOD) policies allow employees to use personal devices for work, but they introduce compliance risks.
Jailbreaking is the process of bypassing manufacturer-imposed security restrictions on a device (e.g., iPhones or Android devices).
This significantly increases the risk of privacy law violations, copyright infringements, and security breaches.
Why Option D is Correct?
Jailbreaking allows users to:
Install unauthorized software, which may violate software licensing agreements and copyright laws.
Remove security restrictions, increasing exposure to data breaches, malware, and non-compliance with privacy regulations (e.g., GDPR, HIPAA, or CCPA).
Bypass digital rights management (DRM), leading to potential copyright infringement issues.
IIA Standard 2110 – Governance mandates that internal auditors evaluate IT risks, including legal compliance related to mobile device usage.
ISO 27001 – Information Security Management also highlights the risks of unapproved software on enterprise devices.
Why Other Options Are Incorrect?
Option A (Not installing anti-malware software):
While a security risk, this primarily exposes devices to cyber threats rather than directly causing regulatory infringements.
Option B (Updating operating software in a haphazard manner):
Irregular updates pose security risks, but they do not directly violate copyright or privacy laws.
Option C (Applying a weak password):
Weak passwords increase security risks, but they do not inherently cause regulatory infringements like jailbreaking does.
Jailbreaking increases risks of copyright infringement (through unauthorized apps) and privacy violations (by removing security controls).
IIA Standard 2110 and ISO 27001 emphasize legal and regulatory compliance in IT security audits.
Final Justification:IIA References:
IPPF Standard 2110 – Governance (IT & Legal Compliance Risks)
ISO 27001 – Information Security Compliance
GDPR, HIPAA, and CCPA – Privacy Law Considerations for BYOD
With regard to project management, which of the following statements about project crashing Is true?
Options:
It leads to an increase in risk and often results in rework.
It is an optimization technique where activities are performed in parallel rather than sequentially.
It involves a revaluation of project requirements and/or scope.
It is a compression technique in which resources are added so the project.
Answer:
DExplanation:
Definition of Project Crashing:
Project crashing is a schedule compression technique used in project management to reduce the project completion time without changing its scope.
It involves adding extra resources (labor, equipment, budget) to critical path activities to complete them faster.
Key Aspects of Project Crashing:
Reduces project duration by increasing resources.
Leads to higher costs due to additional labor or expedited material procurement.
Used when project deadlines must be met and standard scheduling techniques are insufficient.
Why Other Options Are Incorrect:
A. It leads to an increase in risk and often results in rework:
While crashing can increase costs and risk, it does not necessarily result in rework unless poorly executed.
B. It is an optimization technique where activities are performed in parallel rather than sequentially:
This describes fast-tracking, not crashing. Fast-tracking involves overlapping tasks, while crashing adds resources to speed up tasks.
C. It involves a revaluation of project requirements and/or scope:
Crashing does not change project scope; it only shortens the schedule by allocating additional resources.
IIA’s Perspective on Project Risk and Management:
IIA Standard 2110 – Governance emphasizes the importance of project risk assessment, including schedule compression risks.
COSO ERM Framework identifies project cost overruns and resource misallocations as key risks in project execution.
PMBOK (Project Management Body of Knowledge) defines crashing as a schedule compression technique used when deadlines must be met at additional cost.
IIA References:
IIA Standard 2110 – Governance & Risk Oversight in Project Management
COSO Enterprise Risk Management (ERM) – Project Risk Considerations
PMBOK Guide – Schedule Compression Techniques (Crashing & Fast-Tracking)
Thus, the correct and verified answer is D. It is a compression technique in which resources are added so the project is completed faster.
Which of the following items represents the first thing that should be done with obtained dote in the data analytics process?
Options:
Verify completeness and accuracy.
Verify existence and accuracy.
Verify completeness and integrity.
Verify existence and completeness.
Answer:
AExplanation:
In the data analytics process, the first step after obtaining data is to ensure its completeness and accuracy. If data is incomplete or inaccurate, the entire analysis process is compromised, leading to unreliable results.
Let’s analyze each option:
Option A: Verify completeness and accuracy.
Correct.
Completeness ensures that all necessary data points are included, preventing missing or incomplete datasets.
Accuracy ensures that data values are correct and free from errors, ensuring reliability for analysis.
IIA Reference: Internal auditors use data validation techniques to confirm completeness and accuracy before analysis. (IIA GTAG: Auditing with Data Analytics)
Option B: Verify existence and accuracy.
Incorrect. While existence is important (ensuring data is valid and not fabricated), completeness is more critical in the initial step to avoid missing data.
Option C: Verify completeness and integrity.
Incorrect. Integrity refers to the reliability and consistency of data across systems, which is a later step after verifying completeness and accuracy.
Option D: Verify existence and completeness.
Incorrect. Existence is less relevant at the initial stage than accuracy, which is crucial for avoiding misinterpretation of results.
Thus, the verified answer is A. Verify completeness and accuracy.
Management is designing its disaster recovery plan. In the event that there is significant damage to the organization's IT systems this plan should enable the organization to resume operations at a recovery site after some configuration and data restoration. Which of the following is the ideal solution for management in this scenario?
Options:
A warm recovery plan.
A cold recovery plan.
A hot recovery plan.
A manual work processes plan
Answer:
AExplanation:
A disaster recovery plan (DRP) ensures that an organization can restore operations after a major IT system failure. The level of readiness depends on the type of recovery site used:
Correct Answer (A - A Warm Recovery Plan)
A warm site is a partially configured recovery site with some hardware and network infrastructure in place.
In the event of a disaster, some configuration and data restoration are required before full operation can resume.
This solution balances cost and recovery speed, making it ideal for moderate-risk scenarios.
The IIA GTAG 10: Business Continuity Management discusses warm sites as an effective disaster recovery solution.
Why Other Options Are Incorrect:
Option B (A Cold Recovery Plan):
A cold site has minimal infrastructure and requires significant time for setup and data restoration.
This is not ideal for organizations needing faster recovery.
Option C (A Hot Recovery Plan):
A hot site is a fully operational backup system that allows instant recovery, but it is very costly.
The scenario mentions "some configuration and data restoration", which suggests a warm site, not a hot site.
Option D (A Manual Work Processes Plan):
A manual plan involves non-IT solutions, which would not address IT system restoration.
IIA GTAG 10: Business Continuity Management – Describes warm, cold, and hot sites for disaster recovery.
IIA Practice Guide: Auditing Business Continuity Plans – Recommends warm recovery sites for balancing cost and recovery time.
Step-by-Step Explanation:IIA References for Validation:Thus, A is the correct answer because a warm recovery plan allows partial system readiness with minimal downtime.
Which of the following is on example of a smart device security control intended to prevent unauthorized users from gaining access to a device's data or applications?
Options:
Anti-malware software
Authentication
Spyware
Rooting
Answer:
BExplanation:
Authentication is a key security control that prevents unauthorized users from accessing a smart device’s data or applications. It ensures that only authorized individuals can use the device, reducing risks such as data breaches, identity theft, and cyberattacks.
(A) Anti-malware software.
Incorrect. Anti-malware software protects against malicious programs, but it does not control user access to a device.
(B) Authentication. ✅
Correct. Authentication mechanisms (such as passwords, biometrics, PINs, and two-factor authentication) prevent unauthorized access to a device’s data and applications.
IIA GTAG "Managing and Auditing IT Vulnerabilities" highlights authentication as a primary control for protecting smart devices.
(C) Spyware.
Incorrect. Spyware is a security threat, not a preventive control. It is a type of malicious software that steals data from a device.
(D) Rooting.
Incorrect. Rooting (on Android) or jailbreaking (on iOS) refers to modifying a device to remove security restrictions, which increases security risks rather than preventing unauthorized access.
IIA GTAG – "Managing and Auditing IT Vulnerabilities"
IIA Standard 2120 – Risk Management
NIST Cybersecurity Framework – Identity and Access Management
Analysis of Answer Choices:IIA References:Thus, the correct answer is B, as authentication is the most effective security control for preventing unauthorized access to smart devices.
During which phase of the contracting process ere contracts drafted for a proposed business activity?
Options:
Initiation phase.
Bidding phase
Development phase
Management phase
Answer:
CExplanation:
Understanding the Contracting Process PhasesThe contracting process generally follows these phases:
Initiation Phase: Identifies the need for a contract and sets initial objectives.
Bidding Phase: Potential vendors or partners submit proposals, and negotiations begin.
Development Phase: Contracts are drafted, negotiated, and finalized before execution.
Management Phase: The contract is executed, monitored, and evaluated for compliance.
Why Option C is Correct?
The development phase is where contracts are formally drafted based on agreements made during bidding and negotiation.
This phase includes legal review, compliance verification, and risk assessment, ensuring the contract aligns with business objectives and legal requirements.
IIA Standard 2110 – Governance requires auditors to assess how contract risks are managed, ensuring formal contract development processes.
Why Other Options Are Incorrect?
Option A (Initiation phase):
This phase defines the business need but does not involve drafting contracts.
Option B (Bidding phase):
In this phase, businesses solicit proposals, but contracts are not fully drafted until vendor selection.
Option D (Management phase):
The management phase involves executing and monitoring the contract, not drafting it.
Contracts are drafted during the development phase after vendor selection and before execution.
IIA Standard 2110 supports governance over contract risk and formal agreement processes.
Final Justification:IIA References:
IPPF Standard 2110 – Governance (Contract Risk & Compliance)
COSO ERM – Risk Management in Contracting
According to IIA guidance, which of the following is a broad collection of integrated policies, standards, and procedures used to guide the planning and execution of a project?
Options:
Project portfolio.
Project development
Project governance.
Project management methodologies
Answer:
CExplanation:
Project governance refers to a broad collection of integrated policies, standards, and procedures that provide a framework for planning and executing projects. It establishes decision-making processes, accountability, and risk management controls to ensure that projects align with organizational objectives.
(A) Project portfolio. ❌
Incorrect. A project portfolio refers to a collection of projects managed together to achieve strategic objectives. It does not specifically define the policies, standards, and procedures for project execution.
(B) Project development. ❌
Incorrect. Project development focuses on designing, building, and testing a project, but it does not encompass governance structures like policies, standards, and oversight.
(C) Project governance. ✅
Correct. Project governance includes integrated policies, standards, and procedures that guide project planning, execution, and oversight.
IIA GTAG "Auditing IT Projects" emphasizes project governance as the primary control framework for managing project risks and ensuring alignment with organizational goals.
(D) Project management methodologies. ❌
Incorrect. Project management methodologies (e.g., Agile, Waterfall, PRINCE2) provide structured approaches for executing projects but do not encompass the full governance framework.
IIA GTAG – "Auditing IT Projects"
IIA Standard 2110 – Governance (Project Risk Management)
COSO ERM Framework – Project Oversight and Risk Governance
Analysis of Answer Choices:IIA References:Thus, the correct answer is C (Project governance), as it provides the integrated policies, standards, and procedures needed for effective project oversight.
Which of the following is a primary driver behind the creation and prloritteation of new strategic Initiatives established by an organization?
Options:
Risk tolerance
Performance
Threats and opportunities
Governance
Answer:
CExplanation:
Strategic Initiatives and Their Drivers:
Organizations create and prioritize new strategic initiatives based on internal and external factors that affect their success.
Threats and opportunities, identified through strategic planning and risk assessment, are the primary drivers for launching new initiatives.
This aligns with the SWOT (Strengths, Weaknesses, Opportunities, Threats) analysis framework, which helps organizations identify external risks and growth opportunities.
Why Threats and Opportunities Drive Strategic Initiatives:
Opportunities: Organizations may invest in new products, markets, or technologies to capitalize on emerging trends and gain a competitive edge.
Threats: External challenges such as regulatory changes, market competition, and economic downturns necessitate proactive strategies to mitigate potential risks.
Why Other Options Are Incorrect:
A. Risk tolerance:
While risk tolerance defines an organization’s willingness to accept risk, it is not the primary driver for creating new initiatives.
B. Performance:
Performance evaluation helps measure the success of initiatives, but it does not directly drive new strategies.
D. Governance:
Governance ensures oversight and compliance but does not initiate strategic changes unless influenced by external threats and opportunities.
IIA’s Perspective on Strategic Planning and Risk Management:
IIA Standard 2010 – Planning states that internal auditors must assess how organizations identify and respond to threats and opportunities when developing strategic initiatives.
COSO Enterprise Risk Management (ERM) Framework highlights that strategic planning should integrate risk management, ensuring that organizations adapt to evolving external conditions.
IIA References:
IIA Standard 2010 – Planning
COSO Enterprise Risk Management (ERM) Framework
SWOT Analysis in Strategic Decision-Making
Thus, the correct and verified answer is C. Threats and opportunities.
Which of the following would most likely be found in an organization that uses a decentralized organizational structure?
Options:
There is a higher reliance on organizational culture.
There are clear expectations set for employees.
There are electronic monitoring techniques employed
There is a defined code far employee behavior.
Answer:
AExplanation:
Comprehensive and Detailed Step-by-Step Explanation with All IIA References:
Understanding Decentralized Organizational Structures
A decentralized organization distributes decision-making authority to lower levels of management and employees rather than concentrating power at the top.
This structure requires a strong organizational culture to ensure alignment with company goals since direct oversight is reduced.
Why Option A is Correct?
Higher reliance on organizational culture is necessary in decentralized organizations because:
Employees must make independent decisions that align with company values and objectives.
Leaders trust teams to operate autonomously, which requires a shared sense of mission and ethics.
IIA Standard 2110 – Governance emphasizes the importance of corporate culture in managing risks within decentralized structures.
Decentralization requires informal controls like culture, rather than rigid policies and electronic monitoring.
Why Other Options Are Incorrect?
Option B (Clear expectations set for employees):
While clear expectations are important, they are common in both centralized and decentralized structures and do not distinguish decentralization.
Option C (Electronic monitoring techniques employed):
Centralized organizations are more likely to use electronic monitoring for control. Decentralized structures rely more on trust and culture.
Option D (Defined code for employee behavior):
Both centralized and decentralized organizations have codes of conduct, but culture plays a stronger role in decentralized settings.
Decentralized organizations rely on strong corporate culture to ensure employees make decisions aligned with organizational goals.
IIA Standard 2110 supports corporate culture as a key element in governance and risk management.
Final Justification:IIA References:
IPPF Standard 2110 – Governance (Corporate Culture & Risk Management)
COSO ERM Framework – Culture & Decision-Making in Decentralized Structures
Which of the following statements is true regarding cost-volume-profit analysis?
Options:
Contribution margin is the amount remaining from sales revenue after fixed expenses have been deducted.
Breakeven point is the amount of units sold to cover variable costs.
Breakeven occurs when the contribution margin covers fixed costs.
Following breakover1, he operating income will increase by the excess of fixed costs less the variable costs per units sold.
Answer:
CExplanation:
Cost-Volume-Profit (CVP) analysis is used to determine how changes in costs and volume affect a company's operating profit.
Correct Answer (C - Breakeven Occurs When the Contribution Margin Covers Fixed Costs)
Contribution Margin (CM) = Sales Revenue – Variable Costs.
The breakeven point is where total contribution margin equals total fixed costs, meaning the company has no profit or loss.
The IIA’s Practice Guide: Auditing Financial Performance supports this as the key breakeven definition.
Why Other Options Are Incorrect:
Option A (Contribution margin is the amount remaining after fixed expenses are deducted):
Incorrect because CM is calculated before fixed expenses are subtracted.
Option B (Breakeven point is the amount of units sold to cover variable costs):
Incorrect because breakeven covers fixed costs as well, not just variable costs.
Option D (Following breakeven, operating income increases by the excess of fixed costs less variable costs per unit sold):
Incorrect because operating income increases by the contribution margin per unit, not by the difference between fixed and variable costs.
IIA Practice Guide: Auditing Financial Performance – Defines breakeven analysis as when contribution margin covers fixed costs.
IIA GTAG 13: Business Performance – Discusses cost-volume-profit analysis for financial decision-making.
IIA References for Validation:Thus, C is the correct answer because breakeven occurs when the contribution margin equals fixed costs.
An organization that soils products to a foreign subsidiary wants to charge a price that wilt decrease import tariffs. Which of the following is the best course of action for the organization?
Options:
Decrease the transfer price
Increase the transfer price
Charge at the arm's length price
Charge at the optimal transfer price
Answer:
CExplanation:
When selling products to a foreign subsidiary, pricing must comply with international tax laws and transfer pricing regulations.
Correct Answer (C - Charge at the Arm’s Length Price)
Arm’s length pricing ensures that transactions between related parties (e.g., parent company and subsidiary) are priced as if they were between unrelated entities.
This helps comply with tax regulations and avoid penalties for manipulating transfer prices to reduce import tariffs.
The OECD Transfer Pricing Guidelines and the IIA Practice Guide: Auditing Global Business Risks recommend using arm’s length pricing to ensure compliance with tax authorities.
Why Other Options Are Incorrect:
Option A (Decrease the transfer price):
Lowering the transfer price may reduce import tariffs but could violate tax laws, leading to legal and financial penalties.
Option B (Increase the transfer price):
Increasing prices may help shift profits but could trigger regulatory scrutiny and additional taxes.
Option D (Charge at the optimal transfer price):
"Optimal" pricing is vague and may not comply with legal transfer pricing standards.
IIA Practice Guide: Auditing Global Business Risks – Covers compliance with international tax and transfer pricing regulations.
OECD Transfer Pricing Guidelines – Establishes arm’s length pricing as the best practice.
Step-by-Step Explanation:IIA References for Validation:Thus, C is the correct answer because arm’s length pricing ensures compliance with tax regulations while minimizing tariff risks.
An investor has acquired an organization that has a dominant position in a mature. slew-growth Industry and consistently creates positive financial income.
Which of the following terms would the investor most likely label this investment in her portfolio?
Options:
A star
A cash cow
A question mark
A dog
Answer:
BExplanation:
Understanding the BCG Matrix and Investment Classifications:
The Boston Consulting Group (BCG) Matrix classifies business investments into four categories:
Stars: High growth, high market share.
Cash Cows: Low growth, high market share.
Question Marks: High growth, low market share.
Dogs: Low growth, low market share.
Why the Investment is a Cash Cow:
The organization operates in a mature, slow-growth industry but has a dominant market position and generates consistent positive financial income.
This aligns with the definition of a Cash Cow, as it represents a stable and profitable business with low reinvestment needs.
Investors typically use Cash Cows to fund other investments, as they generate steady cash flow with minimal risk.
Why Other Options Are Incorrect:
A. A star:
A Star requires high growth and high market share, but the organization operates in a slow-growth industry, disqualifying it from this category.
C. A question mark:
A Question Mark is in a high-growth industry but lacks market dominance. Since this company is already dominant, it does not fit this category.
D. A dog:
A Dog has low growth and low market share, meaning it does not generate strong financial returns. The company described produces positive income, ruling out this category.
IIA’s Perspective on Business Strategy and Portfolio Management:
IIA Standard 2120 – Risk Management states that internal auditors must assess the strategic positioning of business investments.
COSO ERM Framework supports the use of strategic models like the BCG Matrix to evaluate investment performance and risk exposure.
IIA References:
IIA Standard 2120 – Risk Management and Strategic Planning
COSO Enterprise Risk Management (ERM) Framework
Boston Consulting Group (BCG) Matrix in Investment Analysis
Thus, the correct and verified answer is B. A cash cow.

